Posts tagged Detection and Response

Threat Research
Forrester Tech Tide for Detection and Response: Is 2019 the Year of Convergence?
Eric Sun

Detection and Response
Utilize File Integrity Monitoring to Address Critical Compliance Needs
Alex Teng

Detection and Response
How to Alert on Rogue DHCP Servers
Rapid7
Vulnerabilities and Exploits
PHP Extension and Application Repository (PEAR) Compromise: What You Need to Know
boB Rudis

Detection and Response
Automation: The Ultimate Enabler for Threat Detection and Response
Eric Sun

Security Operations
PowerShell: How to Defend Against Malicious PowerShell Attacks
Josh Frantz

Detection and Response
Detecting Inbound RDP Activity From External Clients
Rapid7

Detection and Response
CIS Critical Security Control 19: Steps for Crafting an Efficient Incident Response and Management Strategy
Christy Draicchio

Detection and Response
Q&A with Rebekah Brown, Rapid7 Threat Intel Lead, on Attacker Behavior Analytics
Christie Ott
Products and Tools
MAC Address Tracker: Generating a Network Inventory Database Using Network Traffic Analysis
Rapid7

Detection and Response
Do You Need Coding Resources on Your Security Team?
Jen Andre

Detection and Response
Deception Technology in InsightIDR: Setting Up Honeypots
Aneel Dadani
Detection and Response
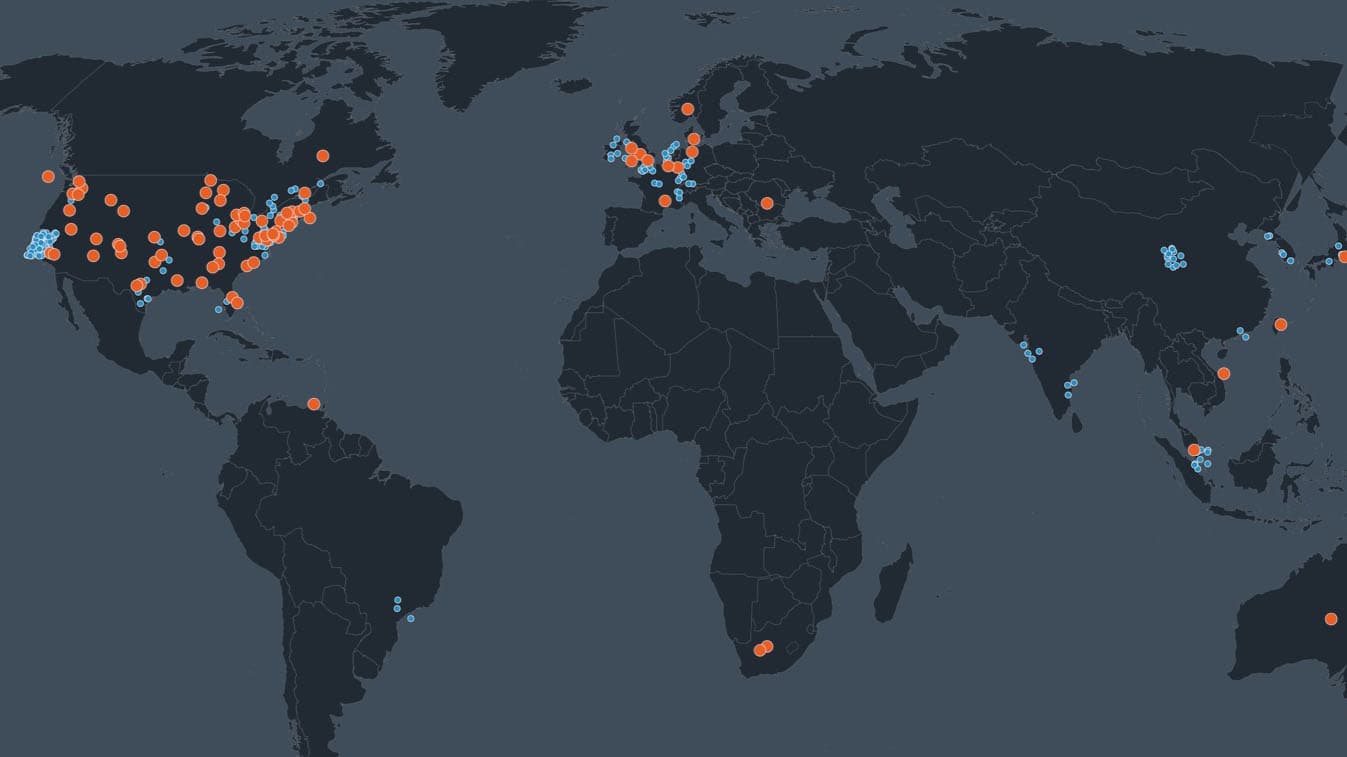
Rapid7 Quarterly Threat Report: 2018 Q1
Rebekah Brown

Detection and Response
Unifying Security Data: How to Streamline Endpoint Detection and Response
Christie Ott

Detection and Response
How to Detect Devices on Your Network Running Telnet Services
Rapid7
Detection and Response
Attacker Behavior Analytics: How SIEM Detects Unknown Threats
Eric Sun

Detection and Response
How to detect weak SSL/TLS encryption on your network
Rapid7

Detection and Response
How to detect new server ports in use on your network
Rapid7

Detection and Response
GDPR Preparation March and April: Course Correct
Sam Humphries

Detection and Response
How To Detect Unauthorized DNS Servers On Your Network
Rapid7

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 4)
Eric Sun