Posts tagged Detection and Response

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 2)
Eric Sun

Detection and Response
Prepare for Battle: Let’s Build an Incident Response Plan (Part 1)
Eric Sun

Detection and Response
Firewall Reporting Excessive SYN Packets? Check Rate of Connections
Rapid7

Detection and Response
Changing the Corporate Network Attacker’s Risk-Reward Paradigm
Justin Houk

Detection and Response
SIEM Market Evolution And The Future of SIEM Tools
Matt Hathaway

Detection and Response
How to Detect BitTorrent Traffic on your Network
Rapid7

Detection and Response
The Legal Perspective of a Data Breach
Rapid7

Detection and Response
Web Shells 101: Detection and Prevention
Oliver Keyes

Detection and Response
How to Troubleshoot Slow Network Issues With Network Traffic Analysis
Rapid7

Detection and Response
Introspective Intelligence: Understanding Detection Techniques
Mike Scutt
Detection and Response
Displace SIEM "Rules" Built for Machines with Custom Alerts Built For Humans
Matt Hathaway

Detection and Response
Warning: This Blog Post Contains Multiple Hoorays! #sorrynotsorry
Sam Humphries

Detection and Response
5 Methods For Detecting Ransomware Activity
Darragh Delaney

Detection and Response
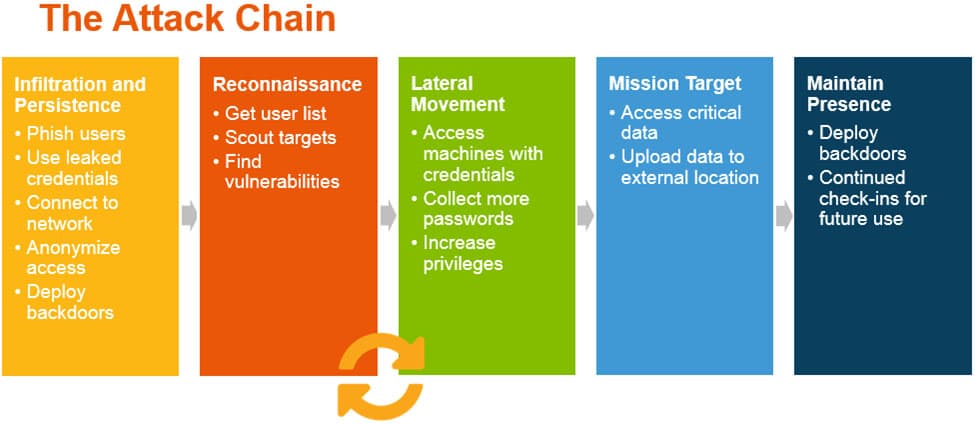
You Need To Understand Lateral Movement To Detect More Attacks
Matt Hathaway

Detection and Response
What Makes SIEMs So Challenging?
Spencer Engleson

Detection and Response
SANS Review of Rapid7 UserInsight (now InsightUBA) for User Behavior Analytics and Incident Response
Christian Kirsch

Detection and Response
Calling Your Bluff: Behavior Analytics in Poker and Incident Detection
Eric Sun
Detection and Response
What is Incident Detection and Response?
Katherine A. Hayes

Detection and Response
Top 5 Alternatives For SPAN or Mirror Ports
Darragh Delaney

Detection and Response
Let's talk about metrics...
Wim Remes
Detection and Response
Tracking Web Activity by MAC Address
Darragh Delaney