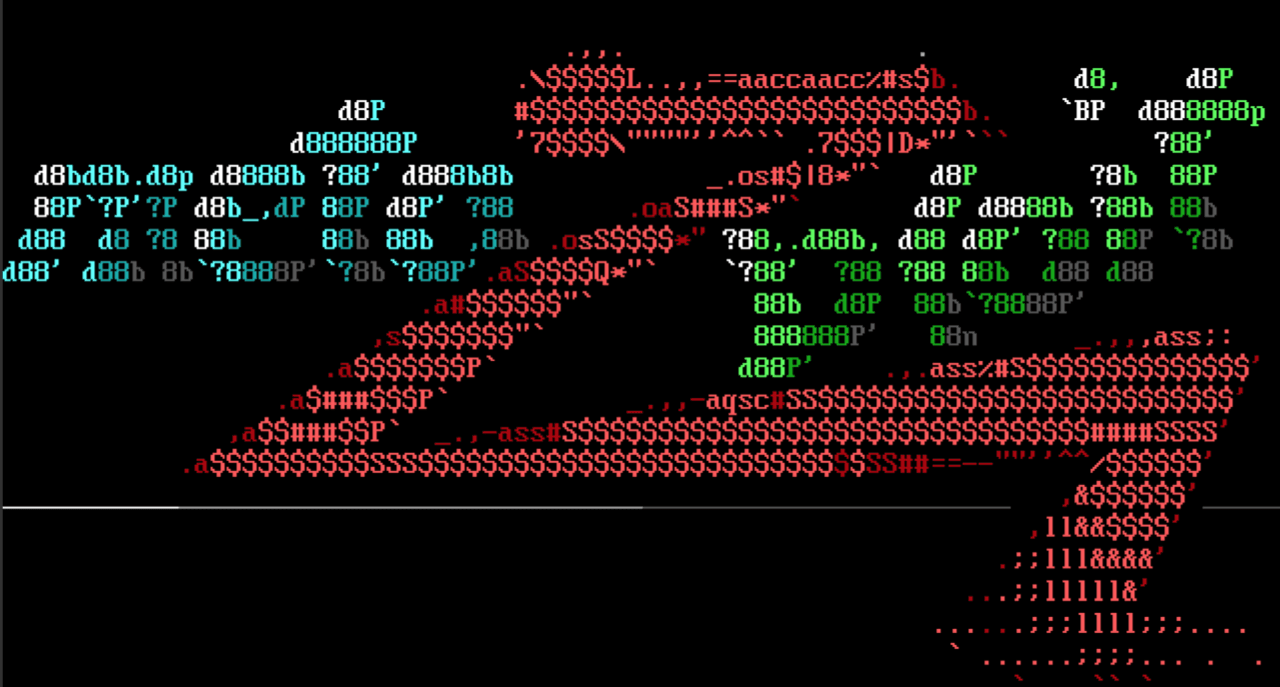
Cisco ‘Sploits
This week’s Metasploit Framework release brings two modules that target Cisco products.The first module, written by our very own jheysel-r7, targets an unauthenticated file upload vulnerability in Cisco HyperFlex HX Data Platform. Vulnerable versions of the Cisco HyperFlex software permit uploading of files through the /upload endpoint due to a missing authentication requirement. The exploit module uploads a jsp web shell and obtains code execution as the Tomcat user.
Community contributor Hakyac wrote the second module that targets Cisco Data Center Network Manager (DCNM). The module, auxiliary/admin/networking/cisco_dcnm_auth_bypass, leverages a static encryption key in the REST API of DCNM to generate a valid session token that is then used to create an administrative account with high privileges and access to sensitive data.
rConfig Authenticated File Upload RCE
Community contributor Hakyac wrote another exploit module that targets network management software. exploit/linux/http/rconfig_vendors_auth_file_upload_rce uses an authenticated file upload vulnerability to achieve remote code execution against vulnerable rConfig installations, specifically versions 3.9.6 and below. The vendor logo functionality in lib/crud/vendors.crud.php allows an authenticated user to upload images; however, there are no checks on the contents of the uploaded file. Because of this, an authenticated attacker can upload a php shell and trigger its execution via a request to the file’s name in the /images/vendor path.
New module content (3)
- Cisco DCNM auth bypass by mr_me and Yann Castel, which exploits CVE-2019-15975 - This adds a module that leverages CVE-2019-15975 which is an authentication bypass in Cisco's DCNM platform. The module will leverage the vulnerability to add a new administrative user account with known credentials that can be used to access the system.
- Cisco HyperFlex HX Data Platform unauthenticated file upload to RCE (CVE-2021-1499) by wvu, Mikhail Klyuchnikov, Nikita Abramov, and jheysel-r7, which exploits
CVE-2021-1499 - This adds an exploit module targeting a file upload vulnerability within the Cisco Hyperflex application that can be used to obtain unauthenticated remote code execution. - rConfig Vendors Auth File Upload RCE by Murat Şeker, Vishwaraj Bhattrai, and Yann Castel - This adds an exploit module for rConfig versions <= 3.9.6. An arbitrary file upload vulnerability exists in lib/crud/vendors.crud.php through the vendorLogo parameter. The functionality for uploading vendor logos does not validate the contents of uploaded files, so an authenticated user has the capability of uploading arbitrary php code. Once uploaded, code execution on the server can be achieved by requesting the uploaded php file in the images/vendor path.
Enhancements and features
- #15358 from zeroSteiner - This updates the exploit/multi/ssh/sshexec module to now account for cases where the target system does not have the python binary. Using the new binary_exists() class method in lib/msf/base/sessions/command_shell.rb, the module now checks for and uses the valid Python binary found on the target system despite not having a fully-established session.
Bugs fixed
- #15350 from pingport80 - Fixes a regression issue in the windows/manage/shellcode_inject module which crashed due to a missing mixin
- #15352 from adfoster-r7 - Fixes an issue where running msfdb init on an already initialised database would generate a new password instead of just starting the database
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).