Posts tagged Penetration Testing

Products and Tools
The Face of Penetration Testing is Changing: Announcing Metasploit Pro 5.0.0
The Metasploit Team

Products and Tools
From Perimeter to Core: Vector Command Advanced Expands Red Team Coverage
Ed Montgomery

Security Operations
PenTales: Pentest Shows why Defense-in-Depth is Critical
Sam Moses

Vulnerabilities and Exploits
PenTales: Weak passwords, Weaker MFA Protocols, and One Absent-Minded Professor
Philip Giattino

Security Operations
PenTales: Exploiting an Internal Network, Loud and Proud
Brad Keil, Sam Moses

Security Operations
Being Fearless in Pentesting: Testing Sensitive Resources
Anna Katarina Quinn
Exposure Management
Under The Hoodie: The Pen Test Diaries
Emma Burdett

Exposure Management
Keys to the Kingdom - Gaining access to the Physical Facility through Internal Access
Anna Katarina Quinn
Exposure Management
Details Matter: Pentesting a single device to guarantee security
Ryan Smith

Exposure Management
Buying Stuff For Free From Shopping Websites
Marcus Chang

Vulnerabilities and Exploits
Metasploit Weekly Wrap-Up 7/19/2024
Christophe De La Fuente

Exposure Management
Metasploit Wrap-Up 12/8/2023
Brendan Watters

Exposure Management
PenTales: What It’s Like on the Red Team
Aaron Herndon

Exposure Management
Why Physical Social Engineering Engagements are an Important Part of Security
Bennett Gogarty

Exposure Management
PenTales: There Are Many Ways to Infiltrate the Cloud
Arvind Vishwakarma

Industry Trends
PenTales: Testing Security Health for a Healthcare Company
Aaron Tennison

Exposure Management
PenTales: Old Vulnerabilities, New Tricks
Austin Guidry

Exposure Management
PenTales: “User enumeration is not a vulnerability” – I beg to differ
Ben Leiden

Exposure Management
Fetch Payloads: A Shorter Path from Command Injection to Metasploit Session
Brendan Watters
Exposure Management
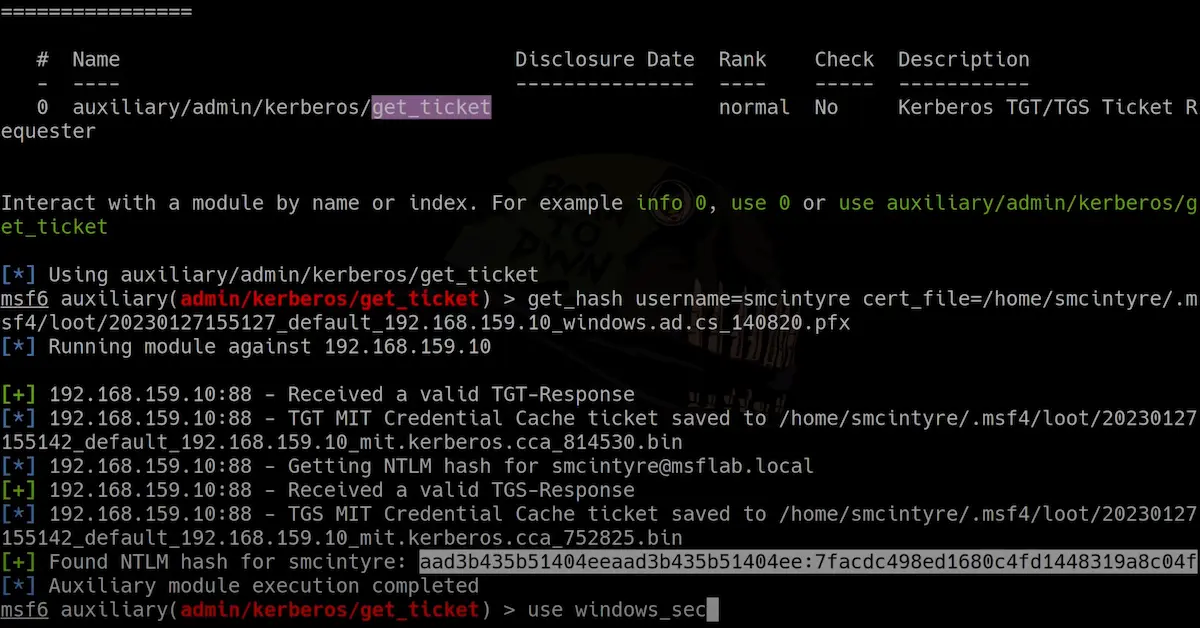
Metasploit Framework 6.3 Released
Alan David Foster
Exposure Management
2022 Annual Metasploit Wrap-Up
Spencer McIntyre