No Prob-ollama
This release brings some serious firepower with multiple new exploit modules and critical vulnerability support! The standout additions are the Ollama path traversal RCE (CVE-2024-37032), a sophisticated exploit chaining arbitrary file writes into unauthenticated root RCE, and the Grandstream GXP1600 stack overflow (CVE-2026-2329), which targets VoIP devices with accompanying credential harvesting and SIP interception post-modules.
The BeyondTrust PRA/RS module got upgraded with support for the new CVE-2026-1731 command injection vulnerability along with legacy CVE support. On the evasion front, there's fresh ARM64 RC4 encryption support with sleep-based detection bypass. Classic vulnerability modules like Unreal IRCd and vsftpd backdoors got quality-of-life improvements with proper check methods and multiple exploitation targets. Several auxiliary scanners (LDAP ESC, GraphQL introspection) also received critical bugfix updates eliminating false positives and crashes.
New module content (7)
Linux RC4 Packer with In-Memory Execution
Author: Massimo Bertocchi
Type: Evasion
Pull request: #20964 contributed by litemars
Path: linux/aarch64/rc4_packer
Description: First Linux evasion module for arm64, a packer using rc4 encryption, in memory execution of the elf binary, and sleep evasion.
BeyondTrust Privileged Remote Access (PRA) and Remote Support (RS) unauthenticated Remote Code Execution
Authors: Harsh Jaiswal and Jonah Burgess (CryptoCat)
Type: Exploit
Pull request: #20978 contributed by jburgess-r7
Path: linux/http/beyondtrust_pra_rs_command_injection
AttackerKB reference: CVE-2026-1731
Description: This adds a new module for unauthenticated command injection in BeyondTrust PRA/RS (CVE-2026-1731). This change also introduces a new library for BeyondTrust familiar helper functions; existing modules have been ported to use it.
GrandStream GXP1600 Unauthenticated Remote Code Execution
Author: sfewer-r7
Type: Exploit
Pull request: #20983 contributed by sfewer-r7
Path: linux/http/grandstream_gxp1600_unauth_rce
AttackerKB reference: CVE-2026-2329
Description: Adds three new modules: one exploit and two post modules, all targeting the Grandstream GXP1600 series of VoIP devices. The exploit module uses CVE-2026-2329 to gain a root session, and the post modules leverage that access to perform credential stealing and packet capture.
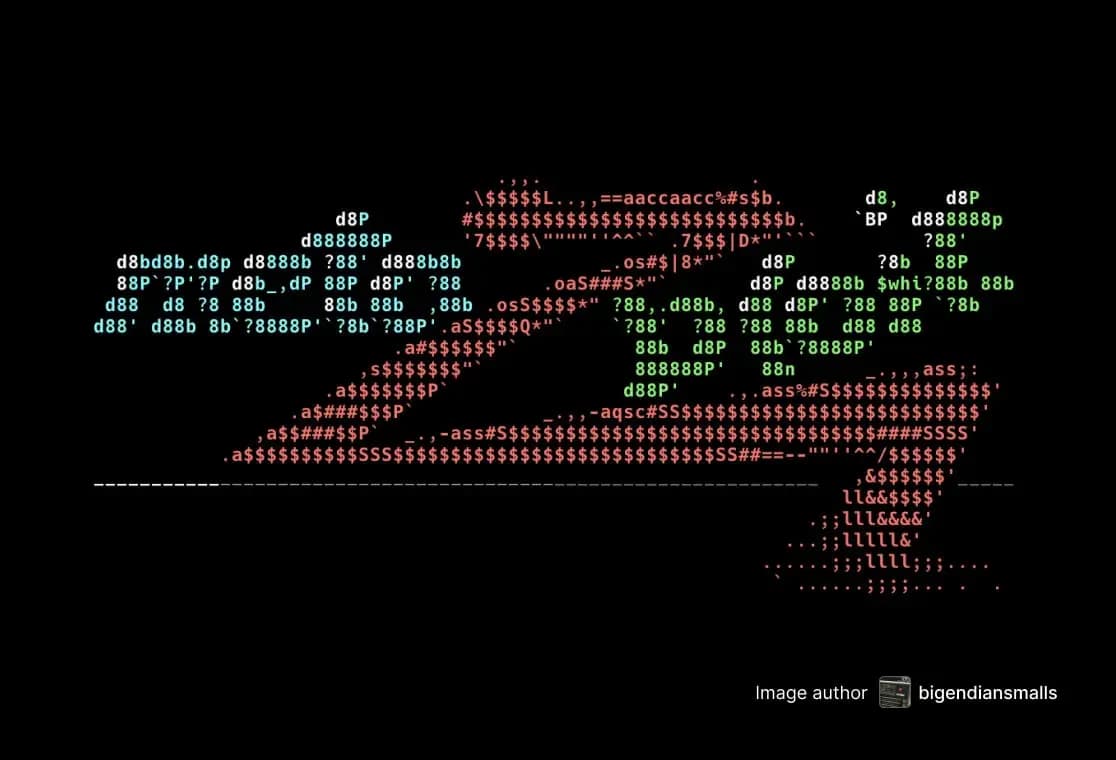
Ollama Model Registry Path Traversal RCE
Authors: Sagi Tzadik [email protected] and Valentin Lobstein [email protected]
Type: Exploit
Pull request: #21006 contributed by Chocapikk
Path: linux/http/ollama_rce_cve_2024_37032
AttackerKB reference: CVE-2024-37032
Description: This adds a new exploit module for Ollama (CVE-2024-37032). Ollama's pull mechanism accepts arbitrary path traversal sequences, allowing an attacker to load a rogue OCI registry and write arbitrary files. The exploit does this by writing .so files into the target, then forcing Ollama to spawn a new process where the malicious library is loaded.
Linux WSL via Startup Folder Persistence
Author: h00die
Type: Exploit
Pull request: #20819 contributed by h00die
Path: linux/persistence/wsl/startup_folder
Description: This adds a new persistence module for WSL that writes a payload to the user's startup folder. The module creates a persistence for Windows; however, the initial access needs to be in Linux.
Windows Registry Active Setup Persistence
Author: h00die
Type: Exploit
Pull request: #20841 contributed by h00die
Path: windows/persistence/registry_active_setup
Description: This adds new persistence for Windows, which uses the Windows feature Active Setup. The module abuse is used to launch our payload, with 2 caveats. 1) You downgrade from admin to user permissions, 2) it only launches the payload once per user.
GrandStream GXP1600 proxy SIP traffic
Author: sfewer-r7
Type: Post
Pull request: #20983 contributed by sfewer-r7
Path: linux/capture/grandstream_gxp1600_sip
Description: Adds three new modules: one exploit and two post modules, all targeting the Grandstream GXP1600 series of VoIP devices. The exploit module uses CVE-2026-2329 to gain a root session, and the post modules leverage that access to perform credential stealing and packet capture.
Enhancements and features (9)
#20859 from dledda-r7 - Splits the exe.rb into separate, more consistent files. Each file responds to a combination of platform and architecture, offering a better granular approach.
#20938 from Chocapikk - Improves the check method in the beyondtrust_pra_rs_unauth_rrce to properly detect older versions that are also vulnerable but report the version in a different way.
#20950 from g0tmi1k - Updates the vsftp_234_backdoor module to add shell and Meterpreter payloads, improves vulnerability detection, and improves the output for better troubleshooting.
#20951 from g0tmi1k - Moves default payload into DefaultOptions in Remote for Mac module. This makes it more consistent with other existing modules.
#20952 from g0tmi1k - Enhances the unix/irc/unreal_ircd_3281_backdoor module to increase payload options, including adding a native Meterpreter session, adds debugging logic inside the module, and more verbose output.
#20988 from adfoster-r7 - Improved SolarWinds exploit module to automatically pick the correct SRVHOST value.
#20992 from adfoster-r7 - Adds a check method to the ms17-010 scanner module to improve the metadata associated with automation workflows.
#21010 from Nayeraneru - This adds reporting for GitLab services.
#21014 from adfoster-r7 - Fixes a crash when running the ldap esc vulnerable cert finder against a target when LDAP binding fails.
Bugs fixed (1)
#21012 from adfoster-r7 - Improves the GraphQL Introspection Scanner module to correctly handle invalid responses and false positives.
Documentation added (3)
#20832 from DataExplorerX - Adds comprehensive documentation for the linux/samba/chain_reply module targeting CVE-2010-2063.
#20990 from jheysel-r7 - This adds and an AI Usage Policy to GSoC Ideas Page as requested by GSoC.
#21005 from h00die - This adds example of GNU inetutils auth bypass module against a Synology NAS to existing documentation.
You can always find more documentation on our docsite at docs.metasploit.com.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest. To install fresh without using git, you can use the open-source-only Nightly Installers or the commercial edition Metasploit Pro