What Is Penetration Testing?
September 26, 2012
In this video, Chris Kirsch, Product Marketing Manager of Metasploit, explains exactly what penetration testing is- and what it isn't. In addition, he reviews how you can use penetration testing tools to validate security risks in your environment.
If you're interested in penetration testing for security risk validation, learn more about Metasploit and download for free today!
Video Transcript
Hello and welcome to Rapid 7's Whiteboard Wednesday. My name is Chris Kirsch. I'm the Product Marketing Manager at Rapid7 for Metasploit. Today, I'd like to talk about penetration testing because it's a topic that, especially people who are new to the industry, have a lot of questions about.
Show more Show lessLet me walk you through what a penetration test is and what it isn't, and I want to compare and contrast a little bit with other things. First of all, some people think a penetration test is the same as port scanning. It's not really the same thing. I'm going to take a little analogy here. Let's assume that your network is a house. Port scanning would be looking with some binoculars or something, at all the different doors and windows; all the entry points into the house; and looking at which ones are open and closed. This translates into, let's say, this is a computer, port 80 would be http, and you can scan which ports are open and that's port scanning. It tells you where the machine accepts connections.
The next thing is vulnerability management. That's really like sending a home inspector over to your house with a focus on security. This guy here comes up with a clipboard and he says, "Hey. This door looks a little old, it's a little run-down. It would be easy to kick it in" or "The lock is a really cheap lock. You should probably change that out because it's really easy to pick." He writes up that checklist and delivers a report to you. That's vulnerability scanning.
Penetration testing is actually when he sends this little ninja to your house to try to break in. So, it's really looking at the network and trying to break into the network with whatever means necessary. It might be smashing the window; it might be using a couple of lock picks to pick the lock on the door that the vulnerability scanner highlighted, and so on. That's really the difference.
Why would you conduct a pen test? There are many, many different reasons for that. The first one is to prevent a data breach. It's a very high- level goal. We all see a lot of data breaches in the headlines. That's the primary goal. That helps you identify where you have weaknesses on the network. Trying the same attack methods as malicious hackers on the Internet, to try and break in. Also, you can test your security controls. You have your firewalls, DLP, IPS, IDS, and so on and you want to see if they're working. With a penetration test, you can really simulate an attack on your network and then figure out, do your controls pick that up? Does your security team pick that up? Do you get a phone call? You might not even want to alert your security team that you're doing a pen test.
As you're rolling out a new system, before you put that live into production, you may want to conduct a pen test to make sure that the system is secure; that you're not exposing your data. Also, what I've seen a lot is, using pen tests to get a baseline. Let's say you're a CSO in a new organization and you're trying to figure out where to spend your security dollars. Where do I need to focus my efforts? Doing a penetration test, gives you that insight. It really tells you, "Hey. We were able to breach the network with x, y, and z methods. These systems are insecure." And, of course, one big reason for doing security measures is also compliance. If we think about PCI, PCI actually requires you to do regular pen tests.
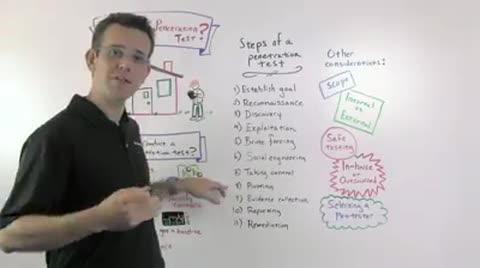
Let me move over to this part of the board. What are the steps of a penetration test? I think this really helps people better understand what a penetration test is and does. First of all, before you start, you need to establish your goal. Your goal may be to breach a credit card database. That might be the goal of the penetration test. So the penetration test is going to try and do everything it can to get to that database. Once the goal is set, you want to do some reconnaissance. That means you're going to research on the Internet, do lookups on what service belongs to the organization, you'll look up on LinkedIn, on Facebook; whatever you can find out about the organization on the Internet and everywhere else. You might also phone into the organization.
Then you start the network discovery. So you're actually scanning the network; this is, essentially, port scanning. You're scanning what servers are there, what hosts are there, what ports are they open on. Then you start the actual intrusion. So you start with exploitation. That means you're actually using little pieces of software to exploit vulnerabilities in the network and to take control over systems. There are also some other ways to get into the systems. For example, brute forcing. If people are using weak passwords or if these passwords are leaked anywhere, or if they're shared across trust zones, you can really use brute forcing.
Also, there is social engineering which, essentially, means trying to trick people into clicking on phishing emails. You might leave malicious files on a USB key in the bathroom or drop it in the parking lot outside the company that you're trying to pen test. That will get you control over their computer. Then, in the end, once you've completed these steps, then you actually have control over the machine. You can do all sorts of fun stuff. You could, for example, upload/download files. You can read out password files, password hashes and reuse those to get deeper into the network. You can take screenshots; you can even switch on the little webcam on the laptop and take video; you can listen to audio. Everything that you can do as a user on the machine, you can now do on that laptop or other computer.
Once you have access to that one machine, it might just have been a phishing email through social engineering; you have access to that one machine. You can then pivot to other machines on the network. So that, basically, means that you jump from one point that you got into the network, to the next machine, to the next machine, and so on. In the end, when you're done, before you do your report, you need to collect some evidence. You need to prove to the people, who entrusted you with the pen test, that you got in. So you collect all of the different things that I mentioned before when I talked about taking control, like downloading files, taking screen shots, collecting passwords. All of these count as evidence that you got into the machine. Then you create your report which is basically a write-up of all the things you tried, and all the things that were successful in conducting that penetration test. Deliver that report and, hopefully, there will be some remediation and mitigation to stop a real attacker from getting in, based on the things that you found.
There are also some other considerations. If you're thinking about conducting a pen test in your organization, I would first think about the scope. That's a little bit related to the goal, like what do you want to test, but also, what means do you want to allow people to test? For example, a lot of organizations say, "Hey, I want you to attack our servers, but I don't want you to use social engineering." That's a decision you can make; it's part of your decision so that would be part of the scope, for example. Or you're limited to certain networks or network segments, certain times maybe.
Do you want to do an internal or external pen test? That essentially means, do you assume that the attacker is coming from outside of the network, attacking your company over the Internet, or are they inside the network already? It could be a malicious insider; it could also be some consultant or somebody who's got physical access to your network, plugged in a box into the network and sniffed network traffic, and so on, and is going from there, from inside the organization. That's part of your scope and your starting decision of, "What's my attack vector that I'm trying to test and protect against?"
Of course, you want to test safely. Here, you really should plan out your steps very carefully. Especially, when you're testing a production network, you want to make sure that you use only reliable exploits. Tools like Metasploit allow you to do that by ranking the exploits. For example, exploits are ranked by reliability. Only excellent and great reliability should be used in production environments. That really helps you to not affect production. One consideration is, do you want to do the pen test in- house or do you want to outsource it? Typically, if you only have one pen test a year, you may want to outsource it because training up your internal resources may not be worth it for that time, or buying the tool. In that case, you may want to go with a consultant. If you want to test more, or you want to have a pre-test before an official audit, or do a regular pen test like, say, every month. So you have, not only a spot check every year but actually an ongoing view of the network security. Then you may want to do it in-house. Train somebody up; buy a tool and run the pen tests in- house. Those are some considerations.
Then, also, selecting your pen tester. If you're choosing somebody internally or externally, you should make sure that they're well trained as a penetration tester. For an internal resource, choose somebody, hire somebody who has already done pen testing, or if you want to use an existing in-house resource, then train them up, look for a good way to get them familiar with the tool and with the space.
That's it for today. Thank you very much for listening, and I'll hope to see you soon.