Most people think of a piggyback attack as a form of wire tapping or physical attack vector in which a malicious actor follows a legitimate person through a door or a turnstile after a badge is swiped.
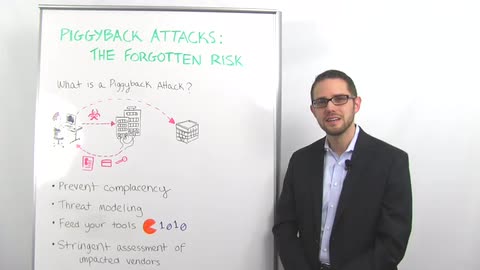
We're going to take a slightly different spin on it today. We're talking about when an attacker gains access to a trusted third party and uses that access to steal data or technology that they can use to leverage an attack against your organization. This could be a crime of opportunity or a crime of intent.
There's two very well-known examples of this. The first was a compromise several years ago of RSA in which state actors stole seed files which were critical to their ability to create a multi-factor authentication experience for their customers. And the attackers used this data to target defense contractors to steal classified or otherwise confidential information.
Another event that you probably recall happened a few years was when a security vendor known as Bit9 had their signing certificate stolen. Bit9 is a company that sells a white listing application. So the compromise of the signing certificate allowed attackers to sign malware so that malware could be installed on customer locations that thought they were protected from that type of an attack.
There is one attack mechanism that I think we're letting slip through the cracks. This is when an attacker can take data, so not necessarily technical components, but just data about your employees. A great example of this would be the recent Anthem compromise. And use that data to generate spear fishing campaigns or otherwise target your employees to gain their credentials or other information about your business.
So what does this mean for you? The first, and I think the hardest thing for all of us to do is prevent complacency. Again, talking about the Anthem attack, this data will be out there forever. Attackers could wait 18 or 24 months before using this data in a spear fishing campaign or other activity.
So what this means for us is we have to have a mechanism for cataloging when these events happen, and making sure that we're tracking that and monitoring that and we don't forget about it in six months.
Another more novel approach that you should all consider is threat modeling. Most of you probably do threat modeling in your application security programs. This is a slightly different spin but the same concept. You want to take every one of these trusted third-party compromises and figure out what data and technology they have and how that data could be used to attack your organization.
That would really help drive multiple things but especially drive your ability to feed your tools. We can't always rely on tooling but we can take novel approaches when it comes to detecting spear fishing attacks and paying attention to potentially malicious domains that are sending emails to your organization or otherwise deploy indicators of compromise to your tool sets.
The fourth and final point I want to make is you need to make sure that you're using this data to feed your recurring assessment schedule. If you have a vendor that's been compromised and you assess vendors every 12 or 18 months, you may want to make an exception for that vendor and reassess them on a quarterly or semi-annual basis.
So that's it for this week's Whiteboard Wednesday. Thank you for joining me