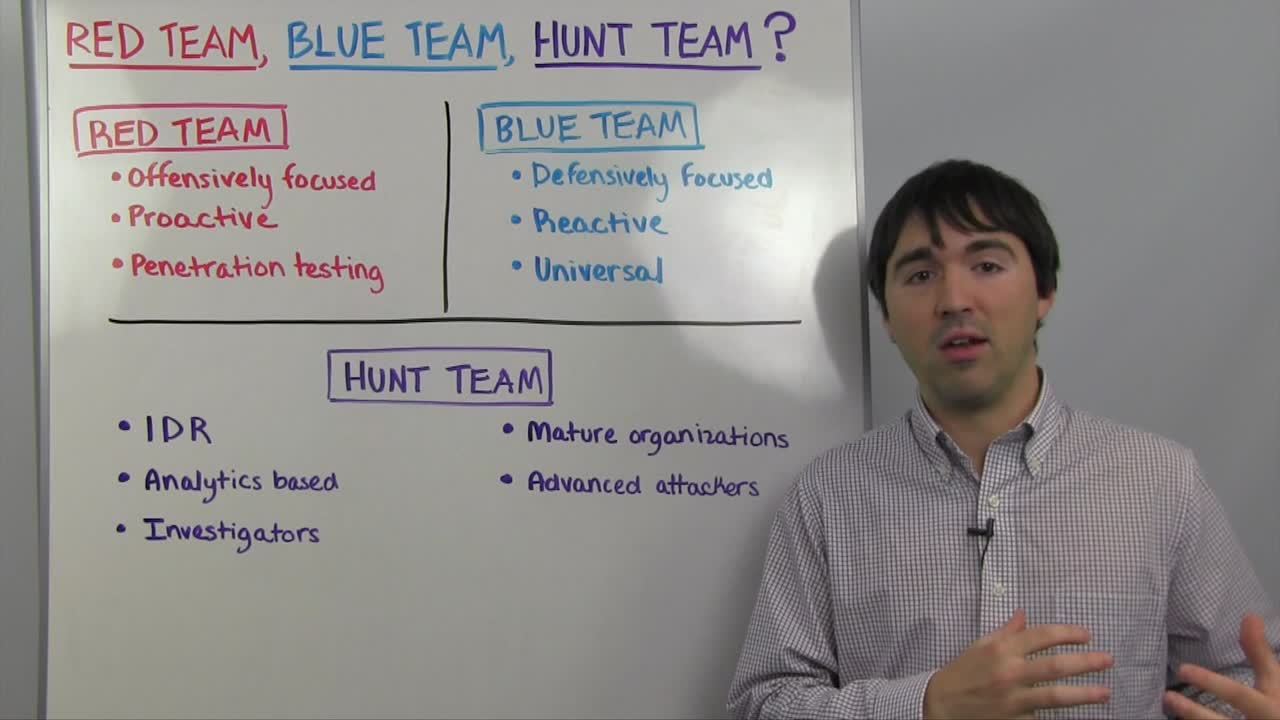
In this week’s Whiteboard Wednesday, Joe Busch, sales engineer for Rapid7, talks about red teams, blue teams, and the latest concept of “hunt teams.”
Many security professionals are familiar with the concept of red (attack) and blue (defense) teams, and participate in security scenario exercises to test existing defenses and improve security preparedness. Hunt teams, which tend to be more specialized and sophisticated, have come about more recently with the growing focus on incident detection and response.
Watch the video to get a full understanding of the details, strengths, and differences across each type of team, and how they might fit into your security program.
Video Transcript
Welcome to this week's Whiteboard Wednesday, my name is Joe Busch, I'm a senior security sales engineer here at Rapid7. This week we are going to be talking about Red teams, Blue teams and Hunt teams. What are they and what are the differences? There is a lot different terms floating around the security industry these days. I think most people have heard of some these but we are going to go through the differences and see where each sits. Before we dive into that, the concepts behind these different teams out there kind of originate with the military. Red Teams are the concept of doing a test exercise with a live fire exercise with different groups.
Show more
Show less
Blue Team would be the defending force and the Red Team would be the attacking force. The whole idea was to test concepts and poke holes on different misconceptions that organizations might have about how they are doing offense or defense. That has all been taken and subsumed by different industries and security industry is no different here. In the security industry world, we've taken the idea of a Red team to be an offensively based team.
These are folks doing offensive security, a proactive attacking of networks, infrastructure or code, depending on the part of environment that we are going after. This is a penetration testing role. We want to think of these as people with very specific skills on the offensive side of the house, and it's something that not every organization has the internal capability for. Organizations might be using different offensive software, catalytic distributions and things like that, or they might use consultants from the outside world to take care of these sort of thing for them. PCI for example requires penetration testing methodologies and organizations sometimes do it themselves, sometimes outsource that activity.
Blue teams I would say are much more generic roles. A Blue team is simply the network defenders. It's a defensively focused kind of organization and they tend to be reactive. It's a universal role, really. Organizations, everybody has a blue team, whether they know it or not, whether they acknowledge or not. Somebody inside the organization whether it's the network defenders, whether it's the IT folks, whether it's the help desk people, is dealing with cases coming in from different tools from users and then they are reacting to that and taking some sort of action. That's really is what a blue team is in a nutshell.
Some organizations have more sophisticated blue teams, but that's where the clock of where it starts. That's red teams and blue teams. A new concept that has been introduced lately is the concept of a hunt team. Hunt team is much more sophisticated team. They focus on the incident response space and they are very analytics-based, so it's a type of response team that uses big data within an organization. They are combing through logs and they have an investigation's focus. You want to think of it as almost Blue teamers that have some offensive capabilities but that are focused on hunting through logs and through computers and through different aspects of the organization looking for evil, looking for bad things happening, things that would be difficult or impossible for a regular blue team to detect. As I said these are mature organizations, you hardly find hunt teams as part of organizations that already have built up an advanced SOC. It's a rather sophisticated process and they're really focused on finding advanced attackers. Many of the tools that organizations deploy already are good at finding some of the low hanging fruits, viruses, you get the request to find different things, but a sophisticated attacker that knows how to get around those defenses is much more challenging to identify, and that's what a hunt team is designed to do. Hunt teams again got internal capabilities, some different services out there deploy something very much like a hunt team into an organization to help identify what is going on and really tap down on advanced attackers. To recap, the old school standards are the red teams and the blue teams, they're the offense and the defense, and sometimes they play together and sometimes they don't. Hunt teams fall into a newer category, focusing on advanced attackers, using big data and using a lot of analytics capability to try and track down unknown threats inside of an environment.
Thanks for watching, and we'll catch you next week.