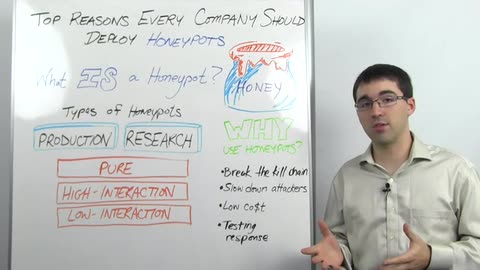
So let's start with, what is a honeypot? A honeypot is a trap computer inside of your network that's designed to attract the attention of attackers or to give you some sort of insight of attacker activity on your network that you would not otherwise have. Now, there can be a couple of types of honeypots. There are production honeypots and research honeypots.
A production honeypot is a honeypot that sits in with the rest of your production servers. It's running services that would normally be running in your environment. It has maybe some interesting data in your environment, and the idea is that it's going to be used everyday by the enterprise security team to keep an eye on what's going on in your environment. It's meant to be used inside the enterprise.
Research honeypots, on the other hand, tend to be more complex. They are storing more types of data, and what they're doing is they're looking at attacker behavior inside the environment or maybe out in the wider world. The idea of a research honeypot is researchers want to understand how attackers operate, what their goals are, and what tendencies they have, so that they can employ new and interesting defense mechanisms against them.
Now, within production and research honeypots, there are three sub-types of honeypots. There's pure honeypots. A pure honeypot is a full-scale completely production mimic system. It's running a ton of different servers. It has interesting data, user information, maybe some fake financial information, and it's got sensors deployed all throughout it, so that you know when certain information is accessed, when the box itself is accessed, and when information is moving around your network from that device. They're very complex, they're very hard to maintain, but they provide a lot of information.
The second type is a high-interaction honeypot. This is similar to a pure honeypot in that a high-interaction honeypot is going to be running a lot of services, but it tends to be lower complexity. There's not going to be as much data on it as you would on a pure honeypot. It's not meant to mimic a full-scale production system.
The third type is a low-interaction honeypot. These are probably the most commonly-deployed honeypots in a production environment. A low-interaction honeypot is going to be running a handful of services. It's really there as an instant-response mechanism more than anything else to know if somebody has accessed that honeypot.
So why should a company deploy a honeypot? There are a couple of great reasons. The first is to break the attacker kill chain. Now, we talked about the attacker kill chain. This is the process by which an attacker moves throughout your environment. First, they're going to recon your environment. Then, they're going to find a way in, and once they're into your environment, the first thing they're going to do is scan your network. When they're scanning your network, they're going to hit all of your devices looking for open ports. Now, a honeypot in your environment should never have any legitimate reason to be accessed. So as soon as they go scanning your environment, you'll know when they hit that honeypot because it's going to send an alert off saying, "Hey, someone's accessing us." Now, you know that you're being attacked. You know something nefarious is going on inside your network, and you can begin to take action at that part of the kill chain before the attacker has begun to exfiltrate data.
The second reason is to slow down attackers. Not only can you use this as an instant-response mechanism, but depending on the complexity that you're willing to put in for your honeypot, you can have it be a distracting point for the attackers. They can go after data, they can attack services, and they can spend significant amount of time working on the honeypot instead of going after parts of your network that have real data. The idea is to drive attacker cost up.
Speaking of cost, the third reason to deploy a honeypot, they're very cheap. In user insight, for example, we have a honeypot O.V.A. that can easily be downloaded and deployed into multiple portions in your environment. Many other honeypot applications are similar. They go out, they're designed never to be accessed, and when they are, they send an instant notification saying, "Hey, you're under attack. Take action."
Then, the fourth reason is testing your instant response infrastructure. It can be used as part of a security maturity type role, so you can run your own scans in your network to test to see if anybody knows what to do for an instant response. Does anyone know what these alerts mean? Is anybody taking action and what's the appropriate next step to take? It's a wonderful way to increase your security maturity at a very low cost.
So to recap, honeypots are trap boxes inside your network. They come in a variety of complexities depending on your organization's need. They drive up attacker cost. They provide insight into your own attack infrastructure, and they're pretty cheap to deploy.
This has been Whiteboard Wednesday. Thanks for watching, and we hope to see you next week