What we want to do today is take you through some of our best practices, but additionally highlight some other things. Those things might include the Oracle update, the Oracle patch that came out at the beginning of this month with 127 patches to it. 51 just for Java. Didn't spread it out at all for anybody.
Additionally, there were two huge patches from Microsoft that came out for an IE zero-day. Not just one but two of them. Everybody heard about the first one. The second one got a hotfix a couple of months back, but wasn't actually remediated within their program. They had to go and actually release an additional patch for it which created more work for you.
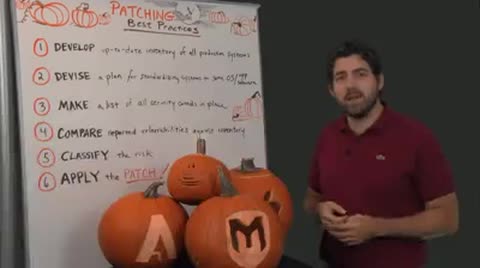
So, when you look at that and you just think about those two companies alone and the patches they released that's those are just two tools. They're a number of tools within your organization, within your security tool box. What we want to do today is kind of highlight some best practices to help you dig through that. Understand what's in there and how to get to it and ultimately apply the patch.
First and foremost, you need to develop an up to date inventory of all your production systems. What this means it's not the update that you produced last year or in January. You have to have something a little more up to date than that. Some folks do it quarterly. I know folks that do it on a monthly basis as well.
It's one way to actually really monitor what's going on in there and by this we mean, OS's, version types, IP addresses, where they sit geographically and who actually sits on that IP address or who's the owner of that IP address from the organization. That can be tricky for some organizations as some people are assigned multiple IP addresses, depending on your network setup.
If it's very dynamic that might apply. If it's static you might have a little more leeway with when you have to do that up to date inventory, but for most people the sooner you do that and the more often you do that, the better you're going to be. Second, you should be devising a plan for standardizing systems and OS's to the same version type. I know this is very hard to do and I know it's almost an impossible task for some organizations.
This doesn't mean to come down to one OS type and say, hey, this is it for the organization. This is it globally. It's probably not going to work that way, but what you want to do is get that down to a manageable number so when you do have 178 patches that come out from between two organizations of Oracle and Microsoft that you know where to target and you know how to hit these things to remediate as quickly as possible. Save yourselves some time and save your IT or remediation team the time as well.
All right, and that brings me to point number three. Make a list of all security controls that are in place within your organization. This is your firewalls. This is your anti-virus. This is also your vulnerability remediation system. So, stuff like Nexpose, everything else you've got. You want to know where that's sitting. You want to know what it's protecting. You want to know what it's monitoring. You want to know what IP's are associated to it.
Rapid7 just released a new product called Controls Insight that can help you do this. There's more details available on our website for that. As well as Nexpose. There's actually reports as well as just some visuals at an expo you're going to be able to get to say, hey, here's my risk today. If I can take these steps and prioritize it based off these vulnerabilities in my environment, this is what I can do.
That brings us down to number four. Okay? Number four is compare reported vulnerabilities against your inventory. All right? You can get these just generically off the you know the NIST website and understand what's actually out there, but using your vulnerability management tool is actually going to help you understand what's in place within your environment. Then obviously through using Nexpose it can show you what's very critical and what's high up on the list or any other tool out there. You can determine what is most important based off of the risk that you see within your environment.
That brings us down to number five which is classifying that risk. Okay? Everything is risky. If it's got a vulnerability that's active out in the free space out there then you're going to have a problem. Okay? It's a matter of clarifying and classifying that risk within your environment to understand how big of a problem that's really going to be. Okay? Just because I have an active vulnerability in my environment it could be fully protected by a firewall that nobody can get to or on top of that it might not be at all.
It could be something that's out in the wild that turns into an IE zero day out of nowhere. You want to make sure you're on top of that and then as soon as those patches are released by those vendors, applying them immediately to your organization. That's number six. Apply the patches.
Once you've kind of gone through the cadence here you're ready to click apply. This does not mean that you're necessarily done though. Might be done with that patch or that end point or that desktop, but you might exactly have to go right back up to number one, go through that inventory again and start all over. Okay? These things change on a daily, weekly basis. We're here to help you get through all that stuff and I'd like to thank you for joining us for another Whiteboard Wednesday here at Rapid7