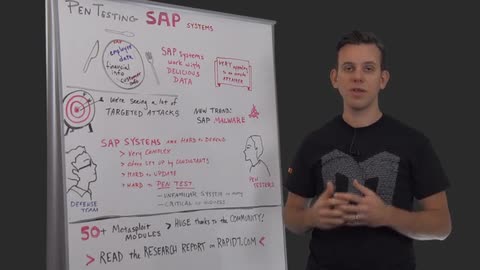
Today I'd like to talk about Pentesting SAP Systems. Now, why do I think that's important? Well, SAP Systems have a lot of juicy data. So we have got employee data, we have got financial info, customer info, production data, could be a credit card information in there. So quite a lot of information that attackers would love to get their hands on. So its very, very appealing to an outside attacker to get into these systems and get to that data.
We are seeing a lot of targeted attacks on SAP Systems. Some of those are actually sabotaging the data trying to fudge with the numbers, trying to fudge with the production systems and causing havoc that way. Some are using it for financial fraud say for example, getting credit card information or looking at the information and then betting on the stock exchange because they have the financials before the rest of the market.
We are also seeing some new trends with SAP malware. So this is interesting because that means it is going from targeted attacks more to like a broad based type attack. So the people who are in cyber crime and attacking systems across the internet not necessarily target on one company and now recognizing that SAP is actually quite a juicy target.
So why are SAP Systems so hard to defend? They are very complex, they have often been set up you know, decades ago and they have often been set up by outside consultant. So the expertise on how these systems are set up and how they are running and so on is not necessarily inside the organization.
Of course, people inside the organization will have some idea of how the systems work but often they are so complex and big and touching so many different areas of the company that it is very hard for one single person to understand the entire system and to see where a potential security issues might arise.
So also they are very hard to update because they are, again, because they are touching so many parts of the organization and because they are ingrained in every process in the company, making a change to that system, bringing it down for an update, for a patch and so on is very challenging. So all the change control involved here are very touchy area to do and its also hard for people to actually pentest the SAP Systems for many of those same reasons.
Often pentesters are very familiar with upgrading systems and webservers and routers and all of the good stuffs, web apps;but they are not necessarily familiar with how SAP works, what the architectures, what the different components are, what talks to what and so on. So that's a big challenge and also it's such a critical system to the business that many companies are simply very reluctant to have people pentest their SAP systems. So this is why there is a lot of attach surface here in the industry.
One of the reasons I'm talking about this today is to draw your attention to the fact that we actually have more than 50 Metasploit modules that are focused on pentesting SAP. So huge thanks to the community, to NMonkey and Bruno Morrison and Dave Harkey and all of the other guys out there who have helped us pull all of these resources together. A huge things, props to them.
And we've also, based on this stuff I've put together a research report which is available on Rapid7.com. It lists all the different modules and how to use them and it also gives you really good introduction on how SAP works and how to pentest it and how to attack it.
All right, that's all for today. Thank you very much and I will see you next week.