This attack is extremely old. You might be asking, "Its 15-year-old attack, why do I care about it?" Because it's still wreaking havoc on everybody's network, and not only is that happening, the amount of scripts that are coming out to exploit this is still getting higher and higher, which means that the point of entry is getting ridiculously lower than Script Kitty.
So I can go on your network, run one command, probably own half your network, end up being DA, and compromising all the things that you were scared about. In fact, Microsoft tried to patch this in 2008 with MS08-068. And essentially, what that stands for is Microsoft 2008, the 68th patch of that year. So that tells you how long this has been around.
So I'm going to give you an analogy before I break into the technical aspect of this. Essentially, what's going on with this attack is the classic guy at the club with his best friend who wants to talk to the girl. Two guys are at a club, maybe not even two guys, because he's an accurate attacker, right? So I'm at the club, and I meet this guy, and he's like, "Hey man, that girl is really pretty. Can you go talk to her for me?" I'm like, "Sure man. Got you buddy. No problem." Walk over to the girl and say, "Hey girl, how are you doing? You want to go out on a date?"
And she goes, "I only go out with dates with guys with BMWs." And I'm like, "Okay." So I walk over to the guy, and I go, "Hey do you have a BMW?" He's like, "Yeah, I've got a key right here." I'm like, "Cool. Let me borrow that for a second." I walk over to the girl. I go, "Click, click, click, here's my keys, girl." She's like, "All right. Let's go on a date." I walk back over to the guy, and I say, "Sorry, buddy. She wasn't interested." And that's how it happens, man in the middle attack.
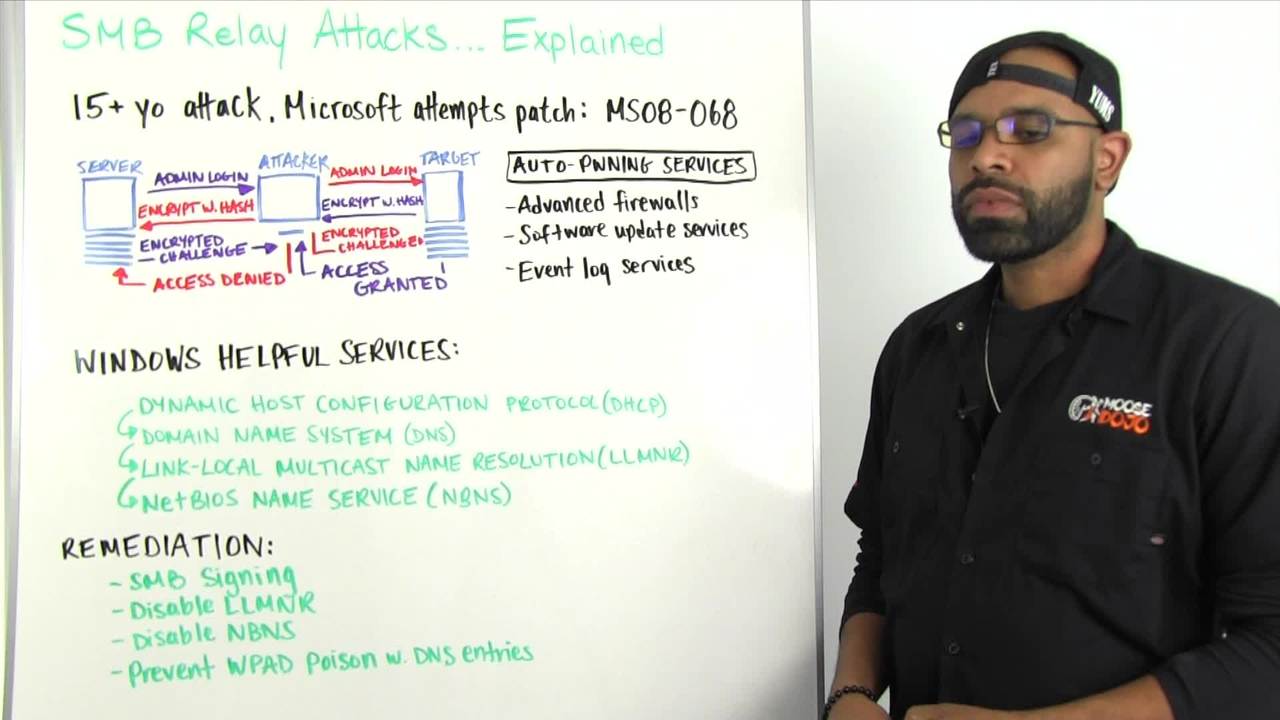
So, from a technical standpoint, what's happening, let's get into the technical. So a server wants to log in. It goes to the attacker, and it says, "Hey, I want to log in." The attacker goes, "Great. I love that idea. Let's do it." So he goes over to the server, and he's like, "Hey, server I'd like to log in."
And the target says, "Encrypt this with your password hash." I'm like, "I would love to do that. Let me go over to the guy." "Hey guy, can you encrypt this with your password hash?" He's like, "Sure buddy. No problem." He gives me the encrypted password. I pass it back to the target. The target says, "Great. Access granted. We're going on a date." And I tell the server, "Sorry buddy. She wasn't interested." Meanwhile, I'm logged in the target, and I'm doing all I want with all my hacker skills and all my pillaging.
So you might be asking, why would a server or a regular user try to log into a target? Well, there's a lot of reasons, auto pointing services. Some of these include advanced firewalls. I've been on networks where I log in, or I plug into the wall, and a firewall will try to log into my box to see if I have the privileges to get out of the proxy. When it logs into my box or attempts to log into my box, guess what's happening? It's trying to log in. And I'm like, "Hey, hold on one second." Let me walk over to this computer. And, "Hey, can I log into you?" And it's like, "Sure." And that whole process plays away.
Software update services. A lot of companies have automatic update software services in place. So, they try to log in to their Windows boxes that way. Event log services, something that tries to log into your Windows box and try to collect logs. But let's say you're not that guy. That's not my network. I have my network locked down. They don't try to log in to anybody I know. Every box is there. That's fine. That's great. Let's move over to here then.
Windows helping services. These are services that Windows do to try to help you out. So normally, one of the oldest attacks that people do try to do is WPAD. So what happens is, WPAD is a web proxy, so whenever Windows starts up or you launch Internet Explorer, it goes to the Internet and says, "Hey, I want to get to the Internet. Is there any WPAD proxies out there? Is there somewhere I should go specifically to get to the Internet?"
You can set your hostname or set your system to be a WPAD host, which means the service says, "I want to get to the Internet," and you go, "Hey, this is how you do it." And he goes, "Okay, thanks." Tries to log into me to collect this information. So what happens is, it logs in and starts that whole process, WPAD attack. Don't do it. It's bad business. That is through DHCP.
But let's say you have a user who wants to fat finger his network name, or let's say there's a share on Suzie's box. And Suzie's share is called Susan. But Susan happens to be gone for the day, and the share is only on her computer for some reason. I don't know why that's happening, but it happened for this scenario. And so Michael wants to log in to Susan's share, because she has a document. So he tries to log in and he goes to Susan's share, and DNS goes, "It's right. Wait, she's not here today." Oh, so DNS doesn't know where it's at. Let's find out.
It rolls down to LLMNR service, and it says, "Hey, network people, is Susan's share anywhere?" The attacker goes, "Hey, yeah, Susan's share is right here, buddy." And then what happens is the server tries to log in to the attacker's box. Again, the process plays out. If for some reason LLMNR doesn't work, it rolls down to NetBIOS. And this is the chain of events that happen. And both of these services are broadcast services, which means they just asked the network, "Hey, who is out there that will do this for me?" And, the attacker is always more than happy to do that for you.
So, at this point you're asking, "Well, how do I prevent this, Leon? This sounds horrible." I'm like, "You are absolutely right." So the first thing you want to do is probably SMB signing, because in 2008, Windows said, "Let's create SMB signing, which we'll just sign the packets so you can't do this attack, and it's great. It kills everything. Problem solved." True. That is the problem solver, but the problem with that is it creates overhead on your network. Sometimes SMB signing is not supported by Linux systems. So if you have Samba, or you have some type of reason why you're talking to Linux or you're using SMB through a printer, it's not going to work, which means it's going to break your network.
So most people don't implement it, and that's why this attack has still been around, because the solutions aren't all the best solutions. But that's the best to mitigate this attack, so you kind of have to weigh those options. Say for some reason you can't do that, maybe you want to look into network segmentation or something of that nature, but if that's not an option, disable LLMNR. So at the very least, you can disable both LLMNR and NetBIOS.
And then, the last thing you want to do is create DNS entries for WPAD. What will happen in that sequence of events is DHCP will say, "Hey, I want to get to the Internet" You'll say, "How's the Internet?" It'll go to the network and say, "Is there a WPAD?" If there's DNS entries for WPAD, it'll say, "Yes, they're right here. Go to the Internet." And, the attacker is like, "No, no, I'm here." And it's like, "No, no, straight to the Internet." So that solves a WPAD attack.
That also prevents it from getting down to the broadcast level. And it also, if you just disable the broadcast level, even if for some reason you don't have a WPAD entry, it goes down here, these services aren't working, it says, "Hey does anybody work? Does anybody know where this is at?" It won't ask those questions, so the attacker will be like, "Hey, I'm right here. I'm right here." And nobody will ever ask. So it'll never get to those procedures.
So those are some helpful ways to mitigate this attack. Nothing is a silver bullet in this particular instance, and that's why the attack has been around for so long, but that's how the attack plays out. And so now, you're a little bit more educated.
That's all we have for this week.