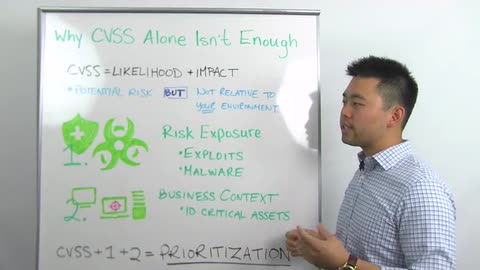
CVSS is the industry standard when it comes to prioritizing and identifying the risk of a vulnerability. However, because the environment is constantly changing, new vulnerabilities are coming up, popping here and there. What that can cause is a lot of anxiety. It can definitely overwhelm the end users or the system administrators, because they have to take these reports, these long reports. They essentially decipher or try to prioritize what they're going to fix first and when.
We're definitely in a day and age where if we look at different vulnerability management programs, you don't want to take the approach for mediating every single vulnerability that you identify. That's just impossible, logically just not feasible. Rather, instead of focusing on that, we want to look at the vulnerabilities that have the most risk of being attacked or exploited, because obviously the easy way ins are the way the attackers are going to go and utilize.
Now, when we look at different proactive organizations today, a lot of them are actually utilizing the strategy already. You know, they use their CVSS as their main metric for assessing their risk, but they'll use other solutions in conjunction to help them in regards to prioritizing, shedding down the number of vulnerabilities, focusing on the more critical ones. However, because it's still manual, it takes time. Which leads me to my topic of when you are looking for a vulnerability management solution today, I would strongly consider looking at these two criteria when you look at the different features and functionalities.
The first is malware kit and exploit modules, or risk exposures as I have up here. If you take a step back, take a look at vulnerabilities, and you're probably asking yourself, why should I be looking at these two items when I have the CVSS to essentially help me prioritize? Well, let's say you have two vulnerabilities and let's say for example, vulnerability A has no exploit associated or malware for that matter, but they have a CVSS of 10. And you have another vulnerability, vulnerability B, that has a lower CVSS, but it does have exploits or malware kits associated. Now, if you just look at CVSS, it makes sense, you want to remediate Vulnerability A first. But if you look at the ease of attacking that vulnerability, because there are already exploit modules and/or malware kits associated with vulnerability B that poses more of a risk on your environment. So that's one of the benefits of having this correlation in regards to having that vulnerability data prioritized for you.
If you look at the end user, the people actually utilizing the vulnerability management solution, that really allows for those guys or those administrators to really help prioritize and make those reports easy to read and more easy to digest when it comes to remediating. Like I said, some organizations are already doing this today, but because it's more of a manual process, they'll go ahead and have that CVSS score and then go ahead and correlate with their own research and with their own time to prioritize that report to their environment.
Now, when you look at the second criteria, we like to look at critical assets. One thing that we focus here is business context, and the reason why this is important is because not every asset is the same in your environment. Now if you look at different environments or different industries, right, you have the retail industry, you have the health industry. So those are two prime examples when it comes to critical assets. We'll take the retail for example. Obviously you have somewhere that you have that credit card data stored. So just by looking at that, if you have the credit card server and you have, let's say your mail server, your credit card server will definitely be more critical, and you definitely want to have that higher on your list of things to fix first. So in regards to having that business context aligned with your reports and what to fix first, that really helps you be more impactful.
CVSS again, that'll help you in terms of prioritizing the vulnerabilities, but that doesn't necessarily mean that it'll have your credit card data or the credit card server at the top of the list of things to fix. So if we come full circle here, combining both the risk exposures and the business context, when you are looking for a vulnerability management solution that really helps the system administrators or the actual security guys on your team to really utilize the solution that'll take care of that work for them, making that whole process streamlined and having those reports that are not only easier to read, but it really makes them more impactful by attacking those easily exploitable or those easily attackable vulnerabilities. This way when you look at the vulnerability management program in a whole, it really makes you become more strategic and more tactical in your approach.
That's it for this week's Whiteboard Wednesday. See you next week.