Below are some recommended resources on InsightVM. For a full list of InsightVM resources, click here.
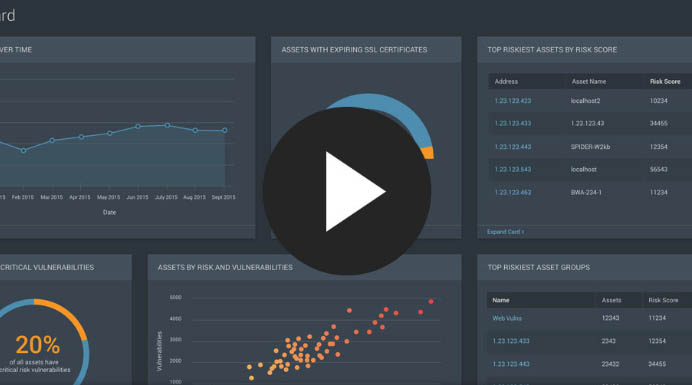
Product Demo: InsightVM
Rapid7 InsightVM is the vulnerability assessment tool built for the modern web. InsightVM combines complete ecosystem visibility, an unparalleled understanding of the attacker mindset, and the agility of SecOps so you can act before impact. Learn more about how this takes shape in InsightVM with this on-demand product demo.
Watch now
InsightVM Product Brief: Act at the Moment of Impact
It’s a race: You against the vulnerabilities living in your network. And this race happens in real-time, not just during a scanning window. Vulnerabilities pop up every day in various forms, so you need constant intelligence to discover them, locate them, prioritize them for your business, act at the moment of impact, and confirm your exposure has been reduced.
With InsightVM, you can feel confident each day that you have helped to protect your organization, customers, and co-workers.
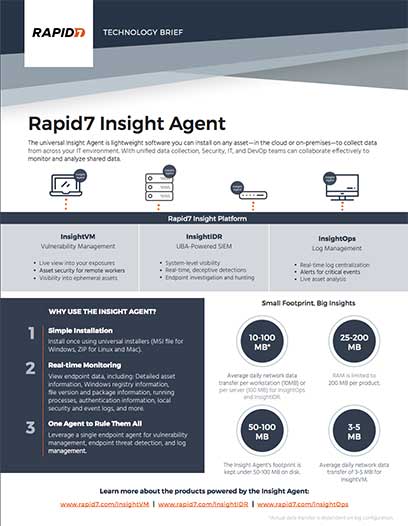
Technology Brief: Get Immediate Answers, Anywhere with the Insight Agent
Since the first antivirus software was introduced to businesses in the early ‘90s, IT ops and security teams have greeted software agents with mutual… disdain. Too hard to manage. No endpoint visibility. Systems slowdown. Not exactly four-star feedback. Keeping common complaints in mind, we developed the Rapid7 Insight Agent, a solution intended to serve customers’ needs where other data collection methods fall short.
Download the technology brief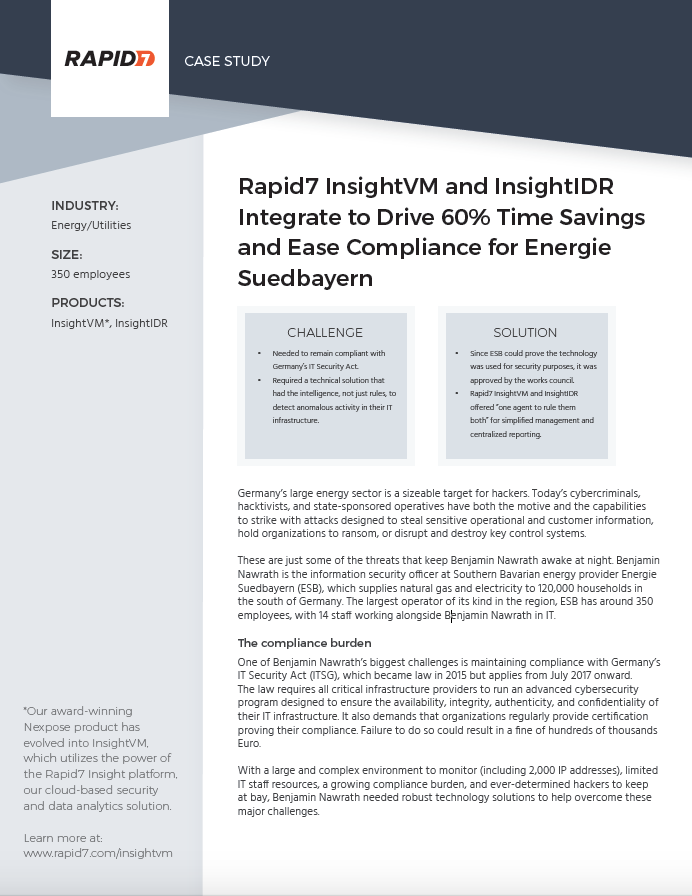
Rapid7 InsightVM and InsightIDR Integrate to Drive 60% Time Savings and Ease Compliance for Energie Suedbayern
Germany's energy sector is a sizable target for hackers. This energy provider needed to maintain compliance and have visibility into its complex environment (including 2,000 IP addresses).
Read the customer story