Managed Detection and Response (MDR) services are still a relatively new concept in the security industry. Just recently, Gartner published their first Market Guide on Managed Detection & Response, which further defines the MDR Services market. MDR Services combines human expertise with tools to provide 24/7 monitoring and alerting, as well as remote incident investigation and response that can help you detect and remediate threats. We like to think of MDR services as an army of cyber guardians.
Do you want an army of cyber guardians? Who doesn't? The challenge is finding the right army, one that knows how to protect your unique organization. Unlike some vendor selections, this isn't a matter of just checking the boxes. It's important to ask a lot of questions, collect evidence, and do a thorough evaluation of the talent and technology that will be used to close the gaps in your incident detection and response practice.
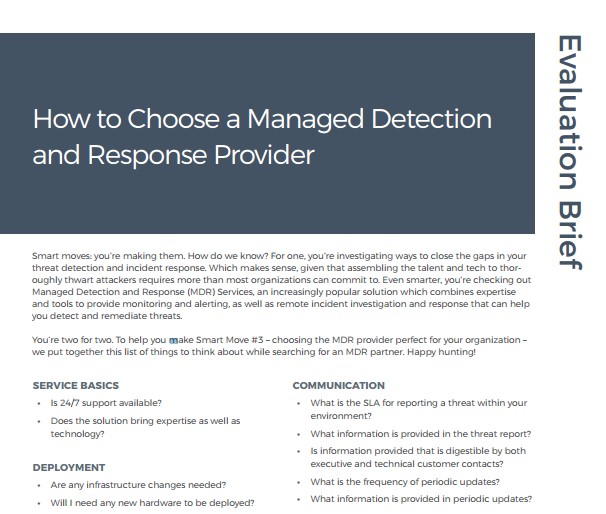
Don't worry. It can be done! To help you with your selection, our security experts put together a list of 38 vital questions you should ask each vendor during your search for the perfect partner.
These questions cover nine categories that are critical to detecting and responding to threats, including provider expertise, communication processes, how the deployment works, and how the service can be tailored. The list also covers the full attack chain with specific questions around threat detection, incident response, and remediation and mitigation.
I won't go into detail with the full list right here, but I've pulled some of my favorites:
- Does the solution propose to detect known and unknown threats by applying several threat detection methodologies? Which ones?
- Can the solution detect threats across multiple platforms? How?
- Does the solution propose to notify you about attacker campaigns against your industry? Request an example.
- Does the solution include endpoint technology for higher fidelity validation?
- What is the SLA for reporting a threat within your environment?
- Is information provided that is digestible by both executive and technical customer contacts?
- Does it include business-focused remediation recommendations and mitigation techniques?
- Is information provided that is digestible by both executive and technical customer contacts?
As you can see, the questions are pretty thorough. However, any potential partner that's worth your time should be able to answer these questions quickly and confidently. Be sure to trust your gut and avoid any answers that seem fishy (or phishy). The extra diligence now will go a long way in your organization's ongoing security health.
Additional reading
Related blog posts

Vulnerabilities and Exploits
Rapid7 Observed Exploitation of PAN-OS GlobalProtect Authentication Bypass Vulnerability (CVE-2026-0257)
Rapid7

Industry Trends
How Security Leaders Cut Through Complexity to Drive Better Outcomes
Emma Burdett
Detection and Response
MDR Selection is a Partnership Decision
Alan Simpson

Industry Trends
What CISOs Should Expect from AI Powered MDR in 2026, According to Rapid7 CEO Corey Thomas
Craig Adams
