Many security operations teams still struggle with managing vulnerabilities, especially in conjunction with vendor and third-party software. The vendor notification <-> triage <-> patch cycle often requires careful coordination to ensure that critical bugs get reviewed and patches applied quickly, while balancing the risk of downtime and other issues that can arise due to unstable patches or system incompatibilities.
Before Komand, monitoring and coordinating vendor vulnerability response was a manual process that a security operations team member had to coordinate, which involved:
- Monitoring a variety of vendor security advisory email list(s) and web pages
- Lookup the owner in the organization (in operations, development, security, or otherwise) responsible for managing the vendor software patches when a new advisory comes in
- Notifying the product owner with details of the advisory
- Monitoring the status over a 24-hour period for owner to indicate the appropriate response was in motion; and if not, escalate it to an appropriate person on the security team
This part of the process alone — not including the actual testing and application of the software updates— could mean 15-30 minutes of time per day for a team member to perform. And often during busy times and other distractions, critical vulnerabilities could fall through the cracks.
With Komand’s security orchestration and automation platform, a simple workflow can be built and customized to your organization’s needs, and all within minutes! We’ll use our RSS feed plugin to automatically monitor a security advisory list, assign the work using a ticketing system, and build a secondary SLA workflow to perform escalation as needed. We'll walk you through a detailed explanation.
STEP 1
Reacting to New Security Advisories Using the RSS Feed Trigger
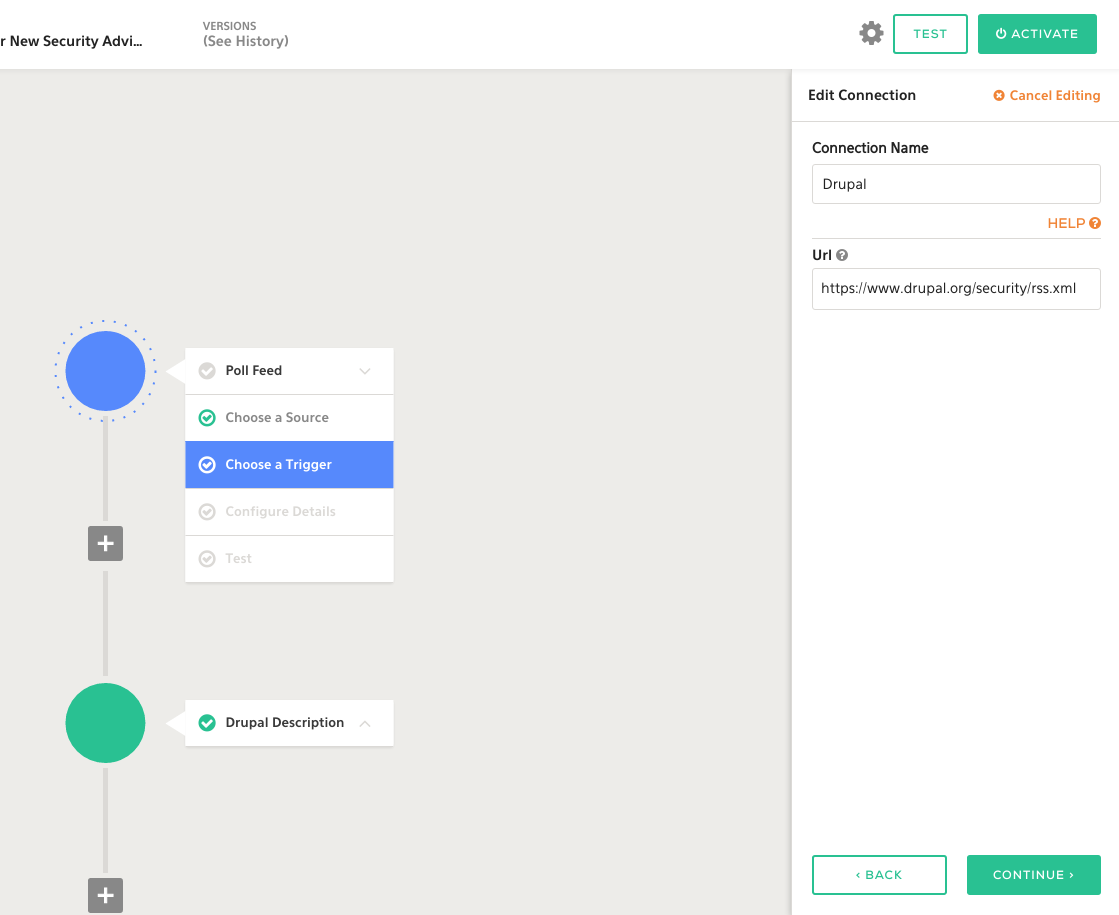
Using Komand’s RSS plugin, we connect our Poll Feed Trigger to the Drupal security team’s RSS feed. This will notify Komand whenever a new security advisory is published:
Afterward, we can use the Markdown plugin to turn the HTML from the RSS feed that contained the details of the CVE, the patch, versions affected, and other important security advisory details into a nicely formatted message that can be used for notification.
STEP 2
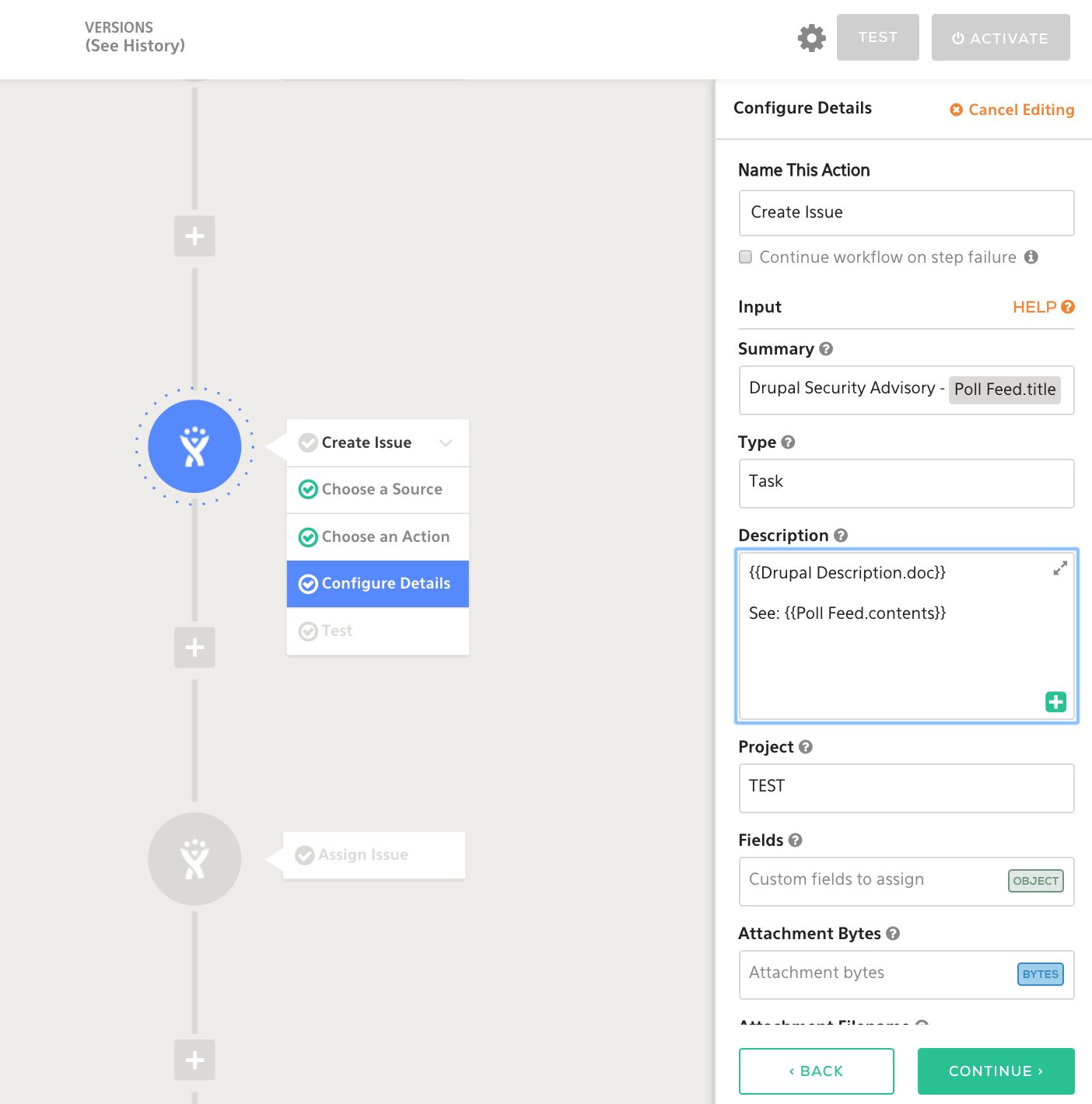
Creating a Ticket in JIRA
Using our JIRA plugin, we’ll perform the following actions:
- Create Issue to create the issue
- Assign Issue to assign to the right owner
- Label Issue to add helpful labels
STEP 3
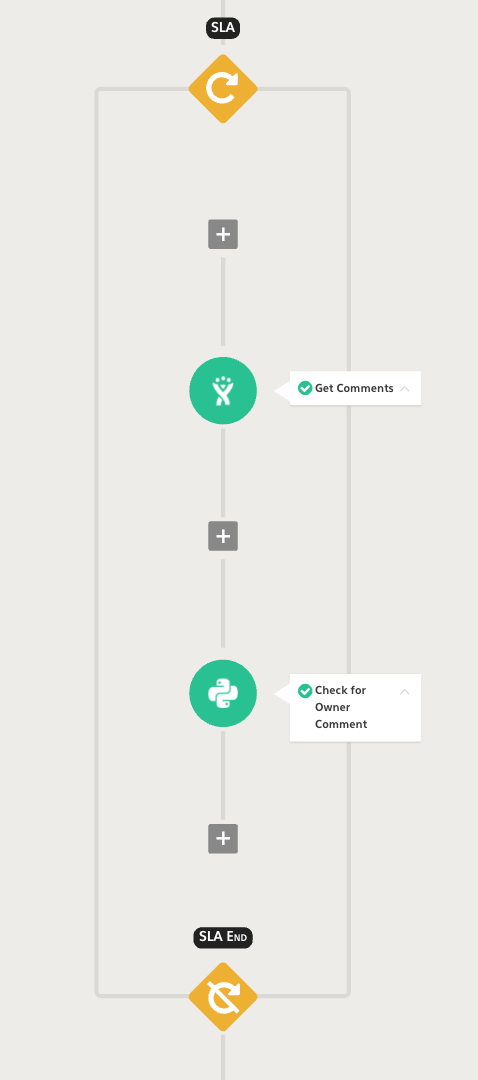
Building Our SLA Monitor
Now, let’s build a simple loop that’s going to monitor this ticket for acknowledgment by the owner we have assigned. Using Komand’s Loop Step, we can build a loop that will run for no longer than a day, looking for owner comments on the ticket using the JIRA Get Comments action (see right).
STEP 4
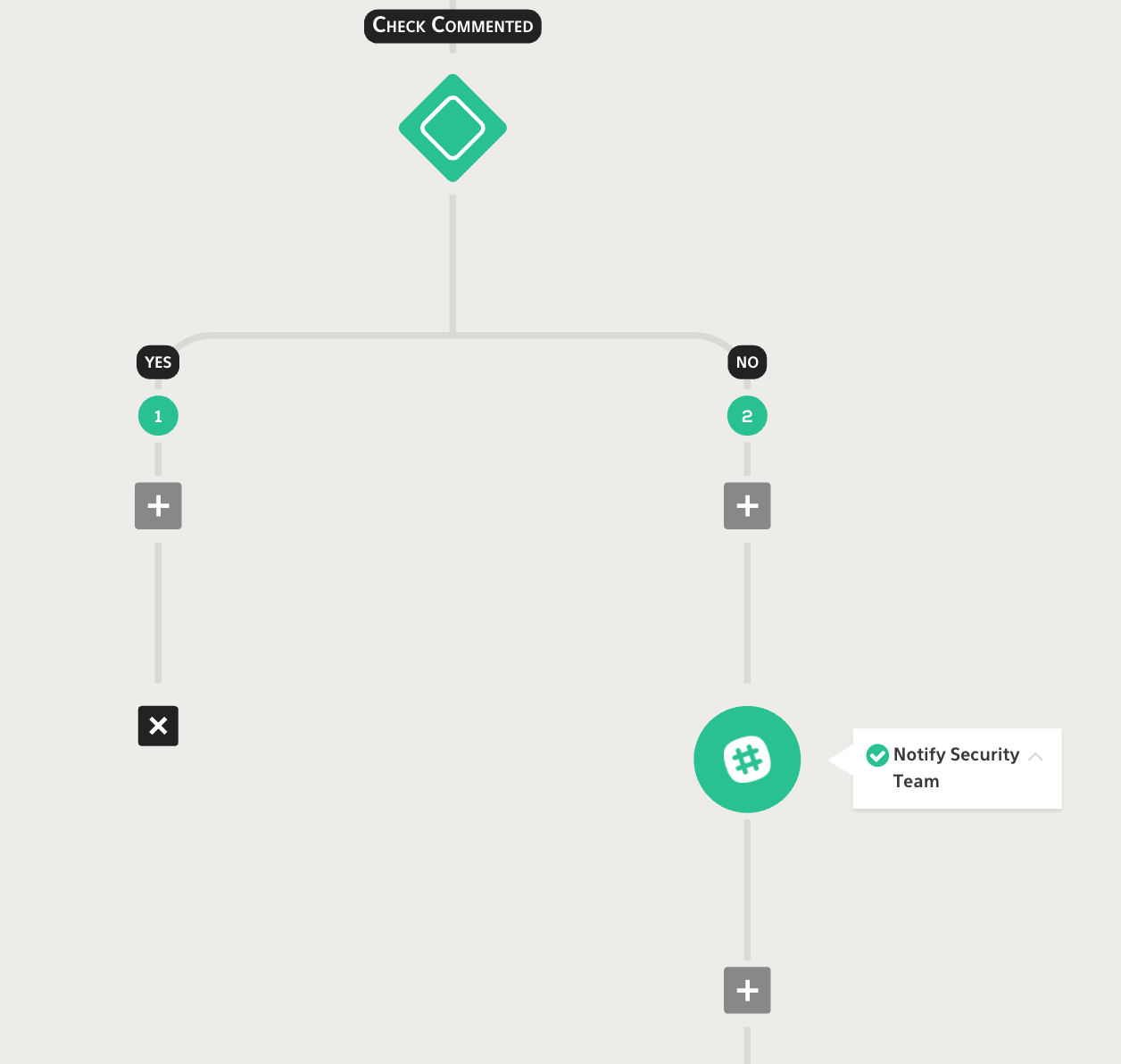
Checking for Comments, and Escalating if No Comments
After the loop has exited, we’ll set up an Automated Decision Step to check for comments. If our ticket owner never acknowledged the ticket, we’ll perform an escalation to the security team via our Slack Plugin. If the ticket owner did acknowledge the ticket, we'll simply end the workflow, as no action is needed.
Automating Effortlessly with Komand
By instrumenting existing tools with Komand’s simple workflow automation layer, you can take process execution time from hours to minutes, accelerating your team’s productivity, accuracy, and reliability. And you can connect your tools, and automate your vulnerability management processes all without writing a single line of code. Seriously.
If you'd like to see the power of Komand for yourself, you can view our recent demo webinar recording.
Related blog posts

Detection and Response
Do You Need Coding Resources on Your Security Team?
Jen Andre

Products and Tools
How Security Orchestration and Automation Will Unite Infosec
Jen Andre

Products and Tools
How to Securely Handle a Lost or Stolen Device: A Practical Workflow
Rapid7
Products and Tools
Security Career Paths: Common and Unique Roles
Rapid7
