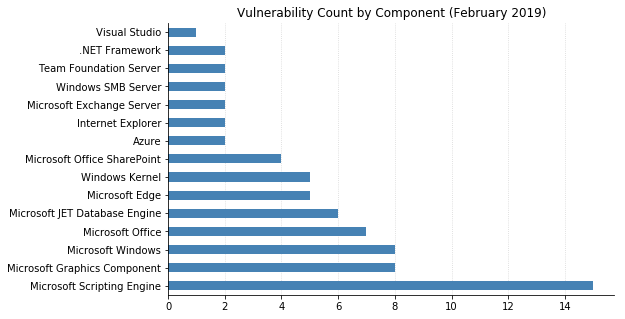
Microsoft got back in the swing of things today after a couple of relatively light months, with over 70 separate CVEs being addressed.
The usual suspects got patches, including Windows, Office, Browsers (including Adobe Flash), .NET Framework, SharePoint, Exchange, and another slew of JET Database Engine Remote Code Execution (RCE) vulns.
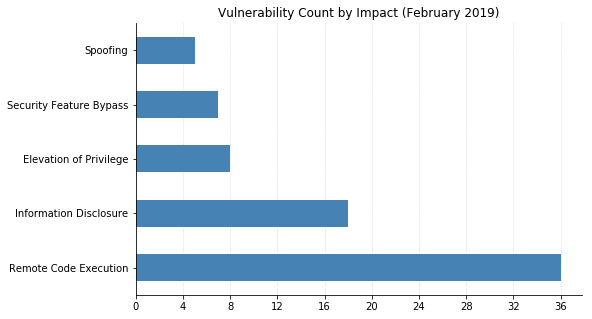
Most critical this month is CVE-2019-0626, an RCE in Windows DHCP Server that could allow an attacker to execute arbitrary code on an affected system.
CVE-2019-0662 and CVE-2019-0618 are also worrisome: RCEs in the Windows Graphic Device Interface that could allow a miscreant to take control of affected systems via web-based or file-sharing attacks.
Nothing else stands out as being particularly egregious, although CVE-2019-0630 and CVE-2019-0633 (RCEs in Windows SMBv2 server) are worth watching out for. An attacker would need to be authenticated to exploit them, but could then run arbitrary code on a vulnerable system.
One vulnerability has been seen exploited in the wild: CVE-2019-0676 is an information disclosure vulnerability in Internet Explorer that could allow an attacker to test for the presence of files on disk. They would first need to convince a user to go to a malicious website.
Two vulnerabilities were publicly disclosed prior to today's releases:
- CVE-2019-0686 is an elevation of privilege vuln in Exchange Server that has now properly been patched. Microsoft had outlined a mitigation in their ADV190007 advisory last week,
but is now encouraging administrators to apply the patch and remove the previous workaround. - CVE-2019-0636 is an information disclosure vulnerability in Windows that could allow a logged in user to view the contents of files on disk without authorization.
And let's not forget Adobe. In addition to their fix for a Flash vulnerability, they also released updates for Acrobat and Reader that patch 71 CVEs. Updates for ColdFusion and Creative Cloud Desktop were also released today.
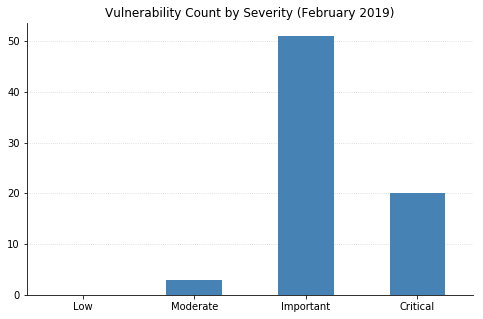
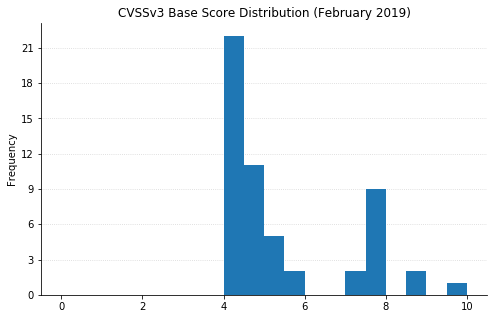
Note: not all CVEs had CVSSv3 data available at the time of writing