Welcome to the latest installment in our cloud security “shift-left” blog series. In our last post, we covered the importance of integrating cloud infrastructure security assessments into DevOps tools and enabling Infrastructure as Code (IaC) developers. This time, we’re focusing on Rapid7’s recent partnership with HashiCorp, ongoing support for scanning Terraform plans with our IaC security feature, and the recently released integration with Terraform Cloud & Enterprise run tasks.
HashiCorp Terraform and InsightCloudSec are a powerful combination
There are countless reasons to adopt cloud infrastructure: hosting applications, compute workloads, data storage, virtual networking, governing identity and access control, and many other use-cases. We are spoiled for choice with the vast array of cloud resources and services designed to perform specific tasks, but each one requires specialized knowledge to configure it securely and interact with other resources. Additionally, resilient cloud applications typically leverage best-in-class features from multiple cloud service providers (CSPs) who compete with innovation, unique features and cost optimization. The more distributed your cloud resources are across providers, the more powerful it is to define them via IaC with a tool that can deploy to any provider.
HashiCorp Terraform is a widely-used open-source IaC tool, especially for supporting multi-cloud deployments. InsightCloudSec has the ability to scan Terraform plans destined for accounts in AWS, Azure or GCP. Rapid7 supports the key resource types for each of the three major cloud providers, and we are constantly expanding our coverage based on usage trends or as needed by our customers.
A major benefit of using InsightCloudSec for IaC security and compliance scans is that you can use the same Insight Compliance Pack for assessing runtime environments and IaC, rather than correlating policy definitions across different tools. This reduces the overhead of maintaining multiple policies and the associated rules across different tools and languages which can easily drift apart. We call this “One Policy”.
Terraform allows users to develop immutable cloud resource definitions as code in a common language for deployment to multiple cloud providers. When paired with InsightCloudSec, resource definitions can be assessed with a single set of security policies applied to both development and runtime environments—creating an optimized experience that delivers efficiency and convenience. To further power this union, Rapid7 has partnered with HashiCorp to develop a formal integration between Terraform Cloud and InsightCloudSec (ICS).
New integrations with HashiCorp Terraform Cloud and Terraform Enterprise run tasks
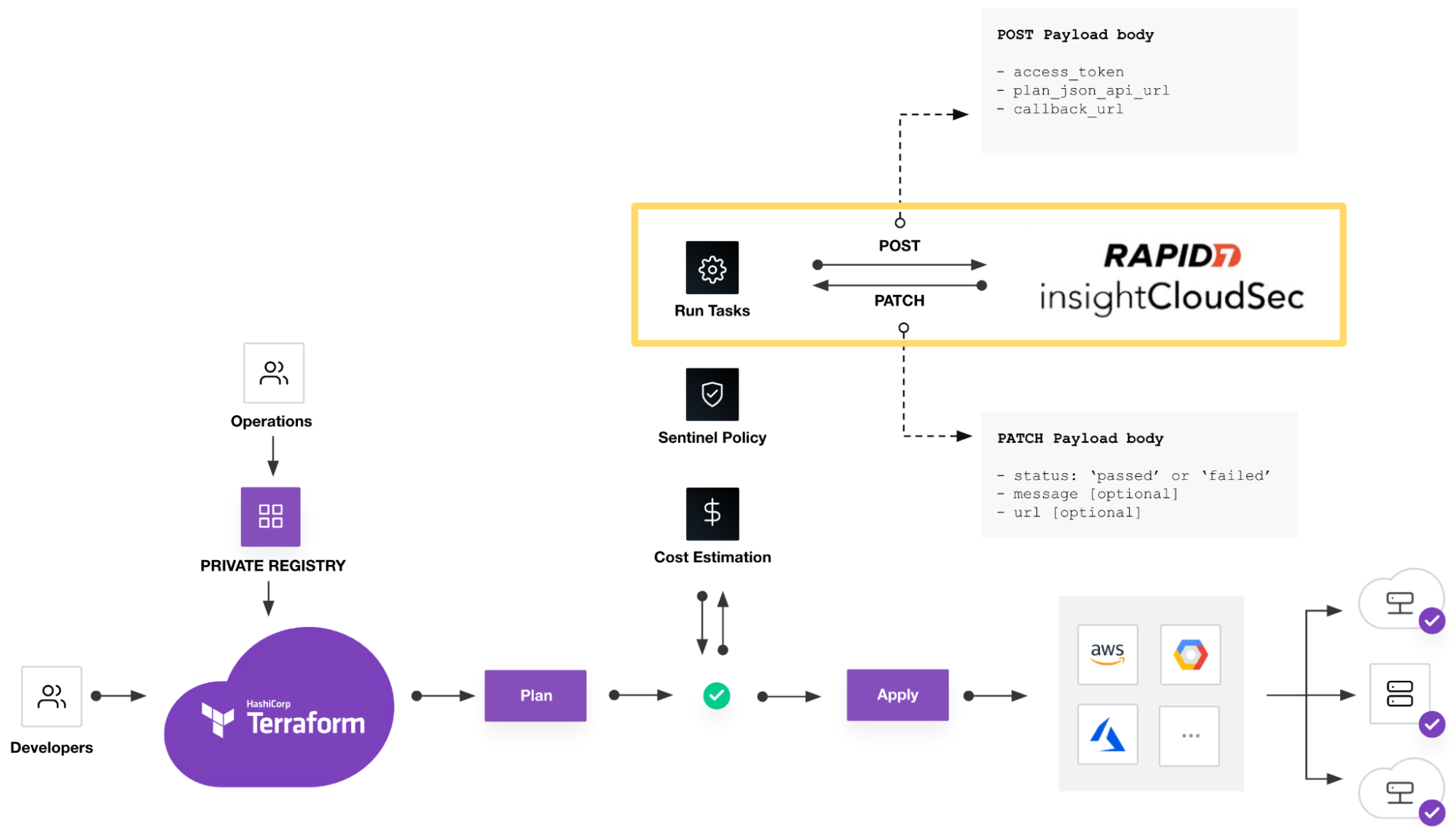
IaC developers create Terraform configurations using HashiCorp configuration language (HCL) and commit them to a source code repository such as Git. The Terraform configuration and the current infrastructure state are evaluated to generate a deployment plan—a preview of changes that will be made in the destination cloud account(s). By linking HCL configurations to collections of resources defined as workspaces in Terraform Cloud, deployment plans are generated and await approval to apply them. At this point, run tasks are used to invoke analysis of the plan, including security and compliance checks in external tools to inform or gate the approval step. This process can be managed through workflows on one of many supported CI/CD platforms; however, HashiCorp developed Terraform Cloud and Enterprise to govern, optimize and secure the process.
DevOps teams using Terraform Cloud to govern cloud infrastructure deployments can securely and reliably trigger a security and compliance assessment of a Terraform plan in ICS using a run task. We’ve worked with the team at HashiCorp to streamline the process of linking a run task to an IaC Configuration in ICS which defines the security policy (Insight Compliance Pack) that will be used to assess the Terraform plan.
This investment is the latest step in our strategy at Rapid7 to directly support DevOps teams to apply IaC security using the tool of their choice. Terraform Cloud was at the top of our list for a formal integration given its prevalent use in the cloud infrastructure and application development community.
Ready to get started?
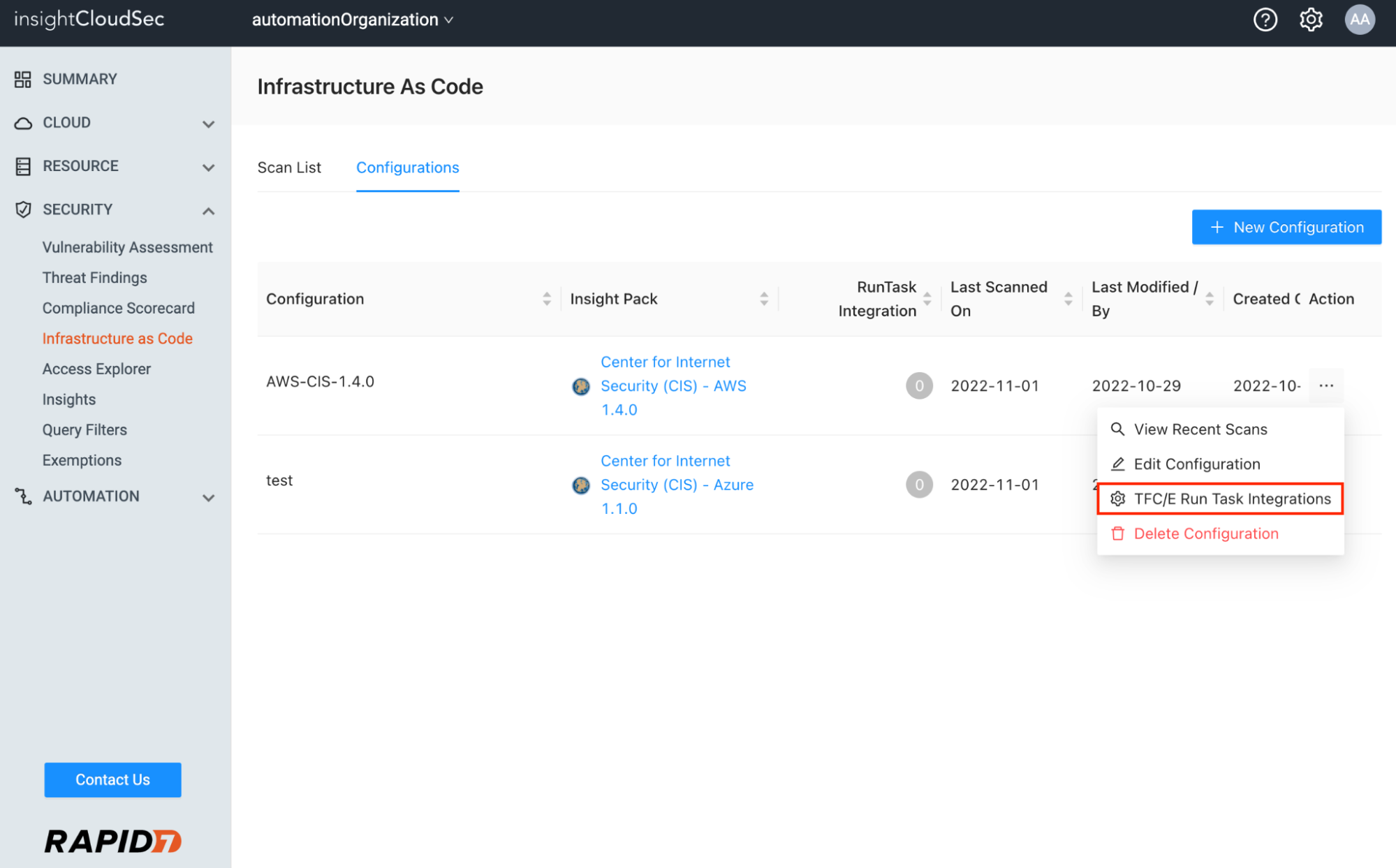
Configuring the new integrations with Terraform is a straightforward process, but let’s walk through it at a high level. Assuming you’ve configured your Terraform Cloud or Enterprise environment with workspaces to generate plans, we’ll show you how to link a Run Task to an IaC Configuration in ICS. Detailed instructions are available in the ICS Product Documentation.
Visit the Infrastructure as Code landing page and select the Configurations tab at the top. Any existing Configuration defined to support scanning Terraform plans can be linked to a run task. Click the Action menu and select the “TFC/E Run Task Integrations” option.
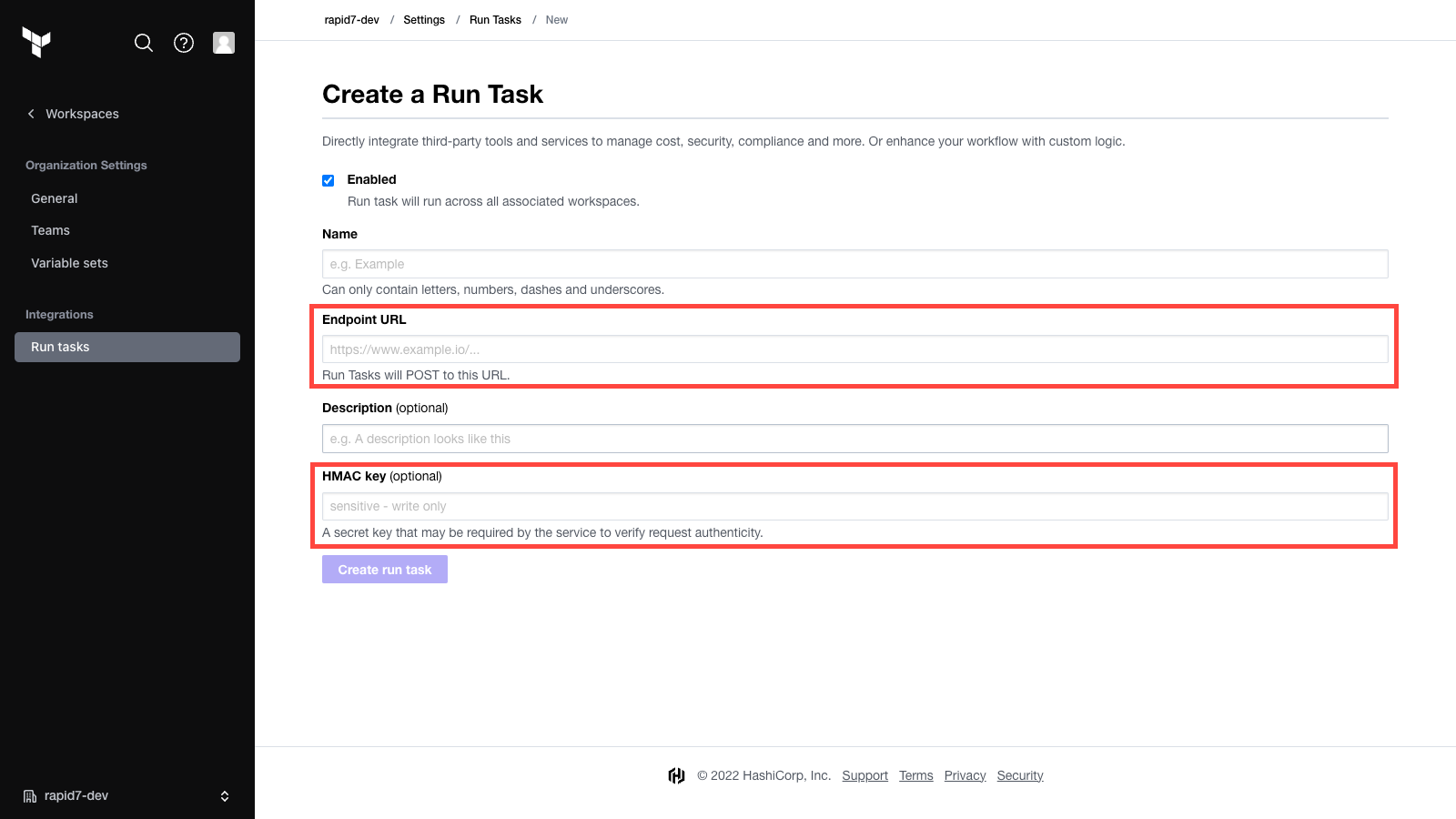
From there, you’ll generate an unique Endpoint URL and HMAC key used during the creation of the run task in Terraform Cloud to securely bind the two systems.
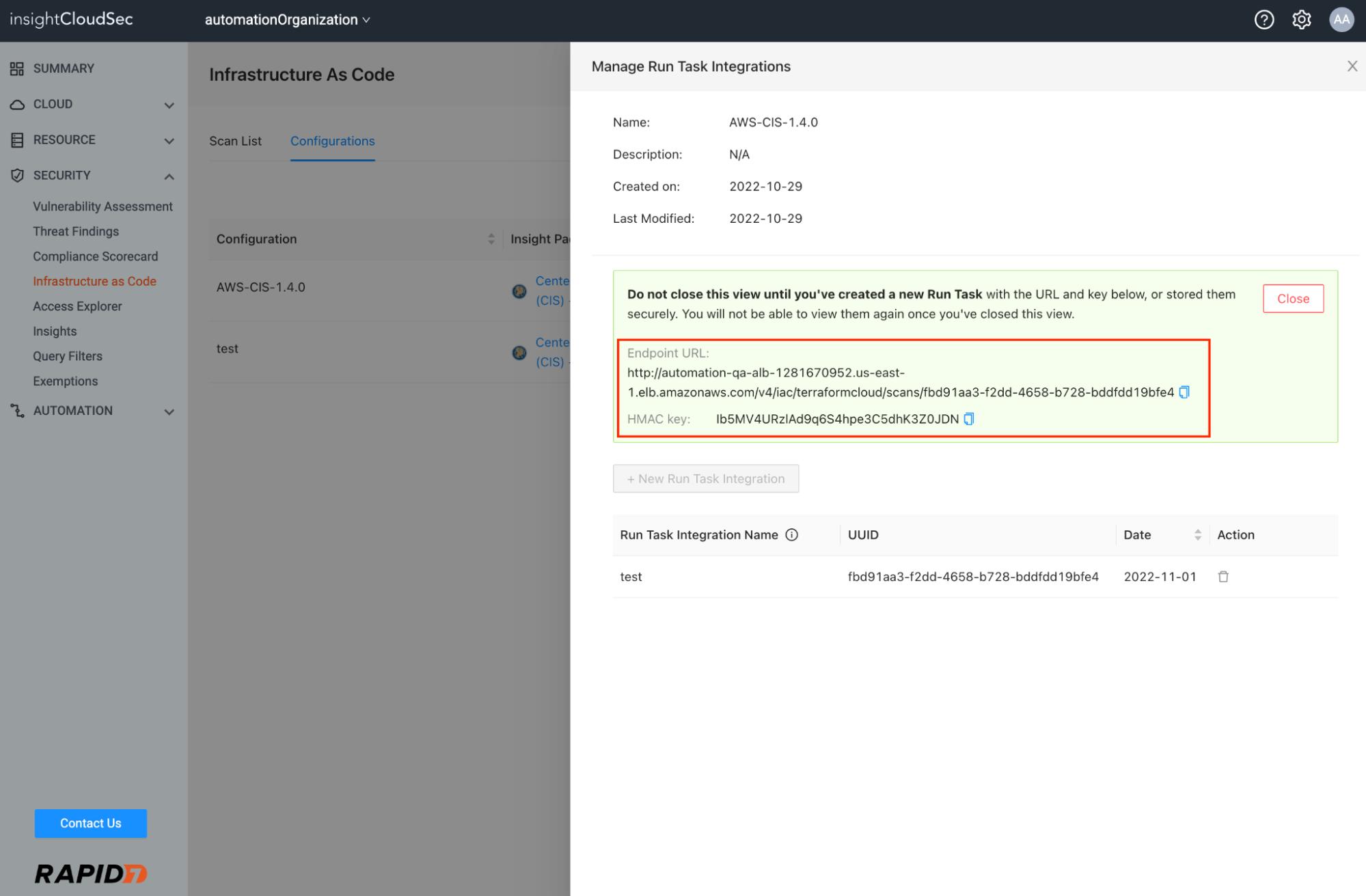
Next, switch to the Terraform Cloud / Enterprise organization settings interface and create a run task. Copy/paste the Endpoint URL and HMAC key provided to you in ICS.
After the run task is successfully created, you will need to associate it with a workspace before generating a plan and triggering it to test the end-to-end process.
During the run task execution, you’ll notice active communication between the two systems monitoring the state of the scan job in ICS and reporting back a final state as Passed, Failed, or Error (indicating the scan job didn’t successfully complete).
We’ve made this integration process simple and accessible to DevOps teams via ICS and Terraform Cloud without any custom API integration required. You can ensure IaC security and compliance scans in ICS are routinely applied to the approval step before Terraform plans are applied to a destination cloud environment.
Our DevOps-focused cloud security investment continues
Rapid7’s InsightCloudSec is proud to partner with HashiCorp to help fulfill the joint mission of making cloud infrastructure and application development and maintenance low cost, code-driven, repeatable, scalable and secure.
For more information , please visit HashiCorp’s partnership page.
Our next blog in the “shift-left” series will include an announcement and overview of a significant upgrade we’re making to our IaC scanning engine and the underlying technology we use to identify issues, pinpoint the location of the problem in code, and provide ‘Actionable Results’ to assist developers with remediation.
Related blog posts

Cloud and Devops Security
Rapid7 named a representative vendor in 2025 Gartner® Market Guide for Cloud-Native Application Protection Platforms (CNAPP)
Joel Alcon

Products and Tools
Proactively Securing Cloud Workloads in the CI/CD Pipeline with Rapid7 and Azure DevOps
Ray Cochrane

Products and Tools
Assessing Container Images Across Private Registries with InsightCloudSec
Josh O'Brien

Products and Tools
New Cloud Risk Dashboard: Identifying Toxic Combinations to Drive Faster Remediation
Pauline Logan
