“The more complex the system, the greater the risk of systemic breakdown, but also the greater the potential for opportunity” - Klaus Schwab Founder and Executive Chairman World Economic Forum.
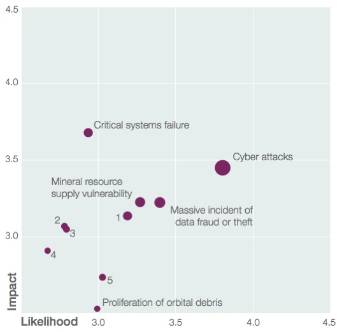
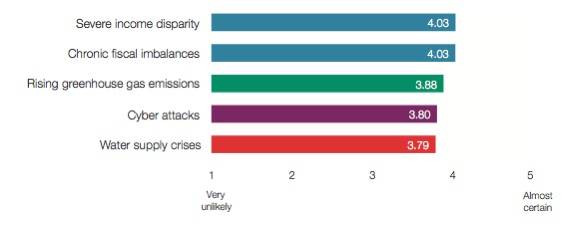
The World Economic Forum released their Global risks 2012 report, outlining the perceived impact, likelihood and interconnectedness of 50 prevalent global risks ranged in five risk categories: economic, environmental, geopolitical, societal and technological.
In this post I'm highlighting some key statements related to the technology category, addressing risks that are of greatest concern in the area of current and emerging technology.
New ways of operating bring new kinds of vulnerabilities. Today, there is a sense that we understand the benefits of the Internet more fully than we understand the risks. Terrorism, crime and war in the virtual world have, so far, been less deadly and disruptive than their equivalents in the physical world, but there is a growing fear that this could change.
Virtual world attacks can range from mundane petty crime and mischief making to shutting down critical systems, or even potentially triggering physical armed warfare.
Axioms
- There are no proven secure systems, only systems whose faults have not yet been discovered, so trying to overcome “hackability” may be as hopeless as denying gravity.
- Any device with software-defined behavior can be tricked into doing things its creators did not intend.
- Any device connected to a network of any sort, in any way, can be compromised by an external party.
- Cyber security is not a problem that any organization, private or public, can solve alone.
The 10 technology risks
The report lists 10 technological risks:
- Critical systems failure: single-point system vulnerabilities trigger cascading failure of critical information infrastructure and networks.
- Cyber attacks: state-sponsored, state-affiliated, criminal or terrorist cyber attacks.
- Failure of intellectual property regime: ineffective intellectual property protections undermine research and development, innovation and investment.
- Massive digital misinformation: deliberately provocative, misleading or incomplete information disseminates rapidly and extensively with dangerous consequences.
- Mineral resource supply vulnerability: growing dependence of industries on minerals that are not widely sourced with long extraction-to-market time-lag for new sources.
- Massive incident of data fraud/ theft: criminal or wrongful exploitation of private data on an unprecedented scale.
- Proliferation of orbital debris: Rapidly accumulating debris in high-traffic geocentric orbits jeopardizes critical satellite.
- Unintended consequences of climate change mitigation: Rapidly accumulating debris in high-traffic geocentric orbits jeopardizes critical satellite infrastructure. Attempts at geoengineering or renewable energy development result in new complex challenges.
- Unintended consequences of nanotechnology: The manipulation of matter on an atomic and molecular level raises concerns on nanomaterial toxicity.
- Unintended consequences of new life science technologies: Advances in genetics and synthetic biology produce unintended consequences, mishaps or are used as weapons.
Of the 10 risks above, critical systems failure was singled out as the one risk that has the most important influence and consequence and is therefore perceived as the greatest systemic importance in the technological category. The risk that a single vulnerability could trigger cascading failures of critical infrastructures and networks has been marked with a low likelihood but a high impact.
Cyber attacks
Cyber attacks risk, intimately connected to the risk of critical systems failure, is ranked within the top 5 risks among 50 in terms of probability. Cyber attacks have the highest likelihood and high impact.
Companies are increasingly aware of cyber threats but are not necessarily sure how to address them. While companies feel more informed about cybercrimes, they also feel less confident in their existing cyber security measures than ever before.
According to the report the objectives of a cyber attacks are: sabotage, espionnage and subversion.
Sabotage: Users may not realize when data has been maliciously, surreptitiously modified and make decisions based on the altered data. Successful acts of sabotage require the greatest resources and technical sophistication.
Espionnage: Sufficiently skilled hackers can steal vast quantities of information remotely, including highly sensitive corporate, political and military communications. Cyber espionage also involves a relatively high level of technical sophistication and is currently believed to be restricted to major corporations.
Subversion: The Internet can spread false information as easily as true. This can be achieved by hacking websites or by simply designing misinformation that spreads virally. Denial-of-service attacks can prevent people from accessing data, most commonly by using “botnets” to drown the target in requests for data, which leaves no spare capacity to respond to legitimate users. Experts believe that this kind of subversive attack currently represents the limits of skilled individuals bearing a grudge. However, barriers for committing more serious acts of espionage and sabotage are lowering all the time.
Trends
Individuals, businesses and nation states are depending more and more heavily on data and systems in the virtual world. Thirty-five per cent of the global population is online, up from 8% just 10 years ago. The way we connect is also changing: at the end of 2011, about 470 million smartphones had been sold worldwide, and the number is projected to double by 2015.
The more significant shift lies in the rapid growth in “the internet of things” – the high-speed communications network composed of electronic devices rather than people. Currently there are five billion devices or “things” connected and remotely accessible through the internet, from cars, kitchen ovens and office copiers, to electrical grids, hospital beds, agricultural irrigation systems and water station pumps. The number of devices connected on the internet is expected to reach 31 billion in 2020.
The downside is that, once an information link is created between a user's electricity meter and the grid, there is a theoretical risk of a user being able to hack into the grid via their meter and sabotage an area's electricity supply. Connectivity also allows for amplification; attacks that would have been isolated incidents in the physical world can achieve a cascading effect through connectivity.
There is a growing market for cyber risk insurance, covering risks ranging from computer security liability to business interruption, cybercrime and cyber extortion.
Reference: