
As you move more of your critical assets to Amazon Web Services (AWS), you'll need to ensure that only authorized users have access. Three out of four breaches use compromised credentials, yet many companies struggle to detect their use. UserInsight enables organizations to detect compromised credentials, from the endpoint to the cloud. Through its AWS integration, Rapid7 UserInsight monitors all administrator access to Amazon Web Services, so you can detect compromised credentials before they turn into a data breach.
Specifically, UserInsight helps you detect these security incidents:
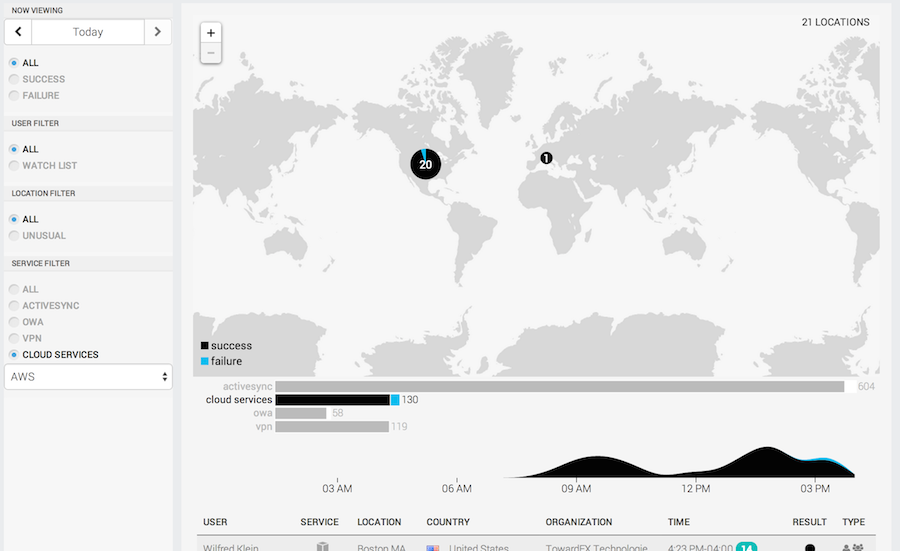
Geolocating AWS authentications with other user authentications to detect compromised credentials
UserInsight tracks from where in the world your AWS administrators are logging in, even when they are outside the corporate network. You will be alerted when a user is logging in from two locations in a short period of time, indicating a compromised account. This even works when only one of the authentications is to AWS. For example, it will tell you if Maria logs into Amazon Web Services from Beijing within only 20 minutes of logging onto the VPN from New York.
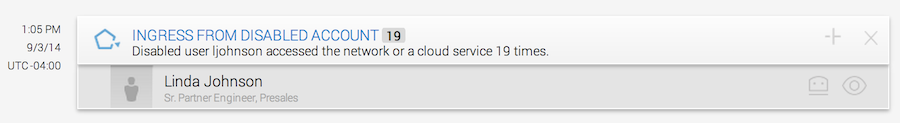
Alerting on AWS access by users whose corporate accounts have been disabled
Most companies have great processes for deprovisioning Windows accounts if a user leaves the organization, but cloud accounts are often overlooked. UserInsight alerts you if a user whose LDAP account has been disabled still logs into Amazon Web Services, even if the AWS account is accessed from outside your corporate network.
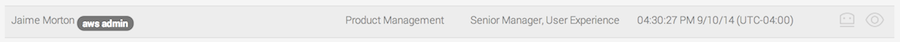
Visbility into users with administrative privileges, whether on-premise or in the cloud
Keeping track on which employees have administrative privileges can be a challenge. UserInsight keeps a running list of any user who has administrative privileges. If users log into AWS, they are automatically added to the administrators' list, giving you full visibility.
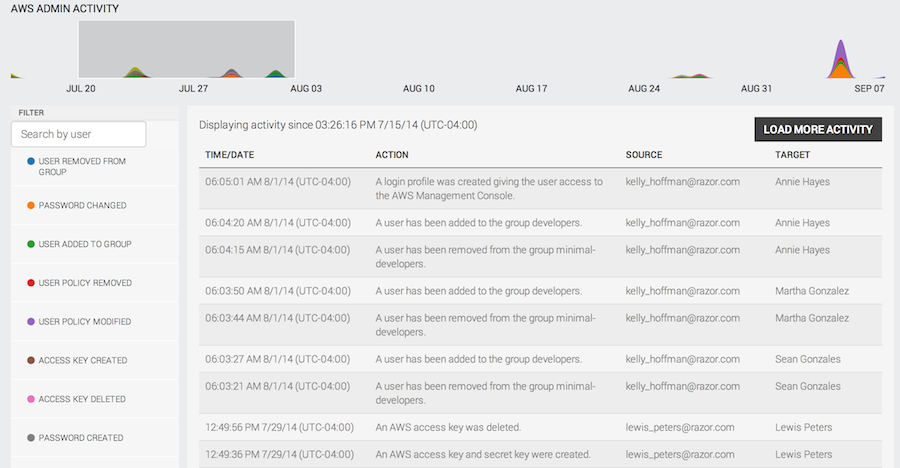
Full logging of all AWS administrative activity
UserInsight monitors all administrative access changes to your AWS account, including adding or removing a user from a group, creating or changing passwords, modifying or removing a user policy, and deleting access keys. You can correlate this activity on a graph and zoom into periods that show suspicious activities.
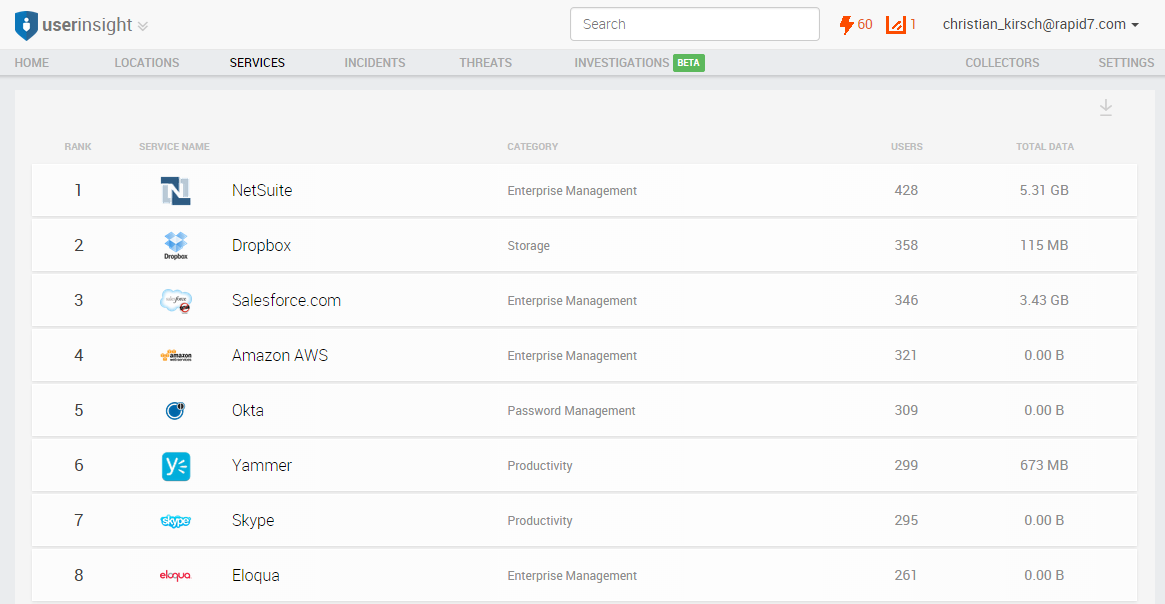
Detecting which employees use AWS accounts not provisioned by IT
Keeping track of shadow IT is tough. UserInsight gives you instant visibility into which users use which web service, including AWS accounts. This enables you to quickly and easily identify non-sanctioned accounts, helping you to consolidate AWS activities. This not only helps your security posture but also enables you to get volume pricing instead of paying list prices for smaller pockets across the organization.
Amazon Web Services is only one of more than a hundred cloud applications for which UserInsight detects compromises. If you'd like to hear more about how Rapid7 UserInsight can detect incidents from the endpoint to the cloud, visit us at Amazon re:invent in Vegas, Booth #637 in
Related blog posts

Detection and Response
Top Challenges for Security Analytics and Operations, and How a Cloud-Based SIEM Can Help
Margaret Wei
![[Q&A] Why Every Threat Detection Strategy Needs User Behavior Analytics](/_next/image/?url=%2Fblog-post-image-placeholder.webp&w=1920&q=75)
Detection and Response
[Q&A] Why Every Threat Detection Strategy Needs User Behavior Analytics
Christie Ott

Detection and Response
Universal Event Formats in InsightIDR: A Step-by-Step NXLog Guide
Teresa Copple

Detection and Response
Universal Event Formats Q&A: Apply User Behavior Analytics to More of Your Data
Alex Teng