This post is the second in a series, 12 Days of HaXmas, where we take a look at some of more notable advancements and events in the Metasploit Framework over the course of 2014._
For today's HaXmas amusement, I have something fun to share with you all. So the other day I was watching this movie called The Knowing, an action-thriller starring Nicolas Cage. The story of this movie begins with a school teacher telling the students that as part of the school's opening day celebration, they should make drawings showing the future as each of them sees it, and placing them in a time capsule. 50 years later, the time capsule is finally opened. But in it, there's an unusual letter full of numbers, which is eventually solved by the one and only Nicolas Cage. The numbers actually link to chilling predictions that either have already occurred or about to, such as earthquakes, fires, tsunamis, etc. And then... well, you should just watch the rest :-)
While I was watching this movie, I was like "oh crap, almost forgot about this, but I got a time capsule too in one of my exploits!" My time capsule hasn't been buried for 50 years, but when I created this I was actually hoping someone would discover it, and then maybe have a laugh. But as far as I can tell, nobody did. So, today is the day I reveal that secret.
I created this time capsule in 2011 for my CVE-2010-3275 exploit, also known as "VLC AMV Dangling Pointer Vulnerability". I remember that while writing this exploit, I couldn't really find an AMV file, so I decided to grab my camera, recorded a short video, and then used a converter to convert the video format to AMV. The video has a message, but is kind of corrupt so you can't actually see it. You can hear something at least, which is meant to be a hint that there's something in the video. You will have to modify back, and I'm going to tell you how.
First off, grab a copy of msf/data/exploits/CVE-2010-3275.amv.
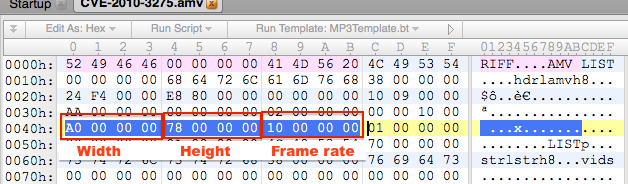
Second, you need a hex editor. My personal favorite is 010 Editor, but use whatever you want. Open the AMV file, and then at the 0x40th byte, you will see this DWORD 0xA0 0xA0 0x00 0x00. This is actually the resolution width of the video, which is the mangled portion that caused the vulnerability. Change the second 0xA0 back to 0x00, which translates to 160 in decimal, like the following screenshot:
Ok, now, go download VLC player. The latest isn't vulnerable anymore, so you're fine.
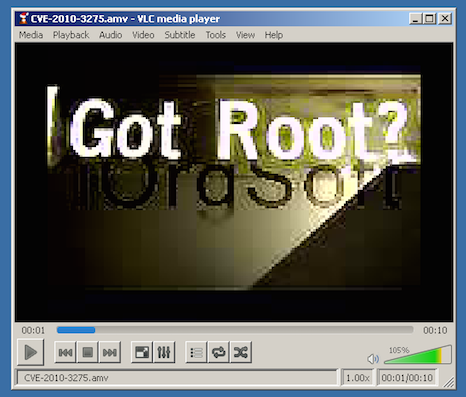
Finally, open the AMV file with your VLC Player, and you shall see the hidden message that's been buried for years:
In case you're wondering where I got that Got Root? sticker, I got it from Defcon, and you can buy yours from Jinx. And this is almost certainly the only Easter Egg left in Metasploit. You probably shouldn't bother looking for more.