
Because AD literally holds the keys to the kingdom for domain-based networks and runtime environments, it’s usually a good idea to keep a close eye on those keys, how they’re being used and what kinds of attacks might be directed at them. Monitoring AD related event logs provides one great tool in exercising due security and integrity diligence. Alerting on specific high-impact events provides yet another.
For over two decades now, Microsoft’s Active Directory (AD) has provided a powerful set of access controls over network, server and user assets. Through judicious use of directory hierarchies, account group definitions and user account assignments, along with group policy objects and regimes, AD permits enterprises and organizations to recognize and protect their information assets. More importantly, AD enables organizations to manage and control how such information is accessed and used. Careful inspection of event log traces related to AD can provide all kinds of useful information about use and potential abuse of access rights and privileges. Such audit trails can also provide an important window into domain administrators’ activities to make sure that nothing untoward, unwanted, or unauthorized is going on.
Attention to AD logs also offers interesting opportunities to confirm that security policy is being enacted as it is intended to be. This is especially important where access controls (and their everyday use) are concerned. In particular, analysis of AD logs can help to address the issue sometimes known as “permission creep” or “over provisioning.” In such circumstances, certain users, either through permissions associated with their individual accounts or by virtue of the groups to which they are assigned, obtain and hold more permissions and higher levels of access than their current job roles or responsibilities actually warrant. This might happen if, for example, permissions are granted to access resources for a temporary work assignment of short duration, but are not subsequently disallowed when that work assignment comes to an end. Similarly, a change of job responsibilities could lead to an aggregation of privileges and permissions if the set associated with the previous job assignment isn’t revoked when those for a new job assignment are added. Careful inspection of who’s doing what, and how that compares to what security policy says they should be doing, can help get this straightened out. Such checks emerge naturally as part and parcel of AD audit or log data on exercise of privileges.
Perhaps even more important is to establish and enforce a blanket policy of auditing and monitoring all AD access, particularly actions involving additions, modifications and deletions to the AD database(s). If domain administrators know their work in the Active Directory environment is always under scrutiny, they will be less inclined to try anything to subvert security. This approach also helps to prevent inappropriate delegation of authority, grant of excessive rights and permissions, or outright abuses of the near-divine powers that AD administrators routinely exercise. If everyone understands admin access to Active Directory is an open book, there is far less temptation and little opportunity for abuses to occur, and every chance that errors and omissions will be caught and rectified in a timely fashion.
Finally, auditing of AD access can provide important clues about various forms of attack on the keys to the kingdom that Active Directory represents. Such things can range from brute force password attacks to sophisticated cracking based on harvesting and illicit use of security identifiers (SIDs) associated with specific, high-value accounts. Careful documentation of the AD environment is a vital start to any AD security effort, and must include the capture of administrative groups and accounts, delegations of authority, and a review of AD maintenance and backup/restore functions and job roles. Here again, log analysis can provide important insight as to how practice differs from policy. It can also help to better align practice to policy as they properly should be. Remember: if you don’t monitor an asset, you can’t manage it effectively, either. That’s why monitoring AD events, and even alerting on specific events (repeated password failures for AD domain admin accounts, for example) are so important to establishing and maintaining proper Active Directory security and integrity.
Article Tags
Related blog posts
Products and Tools
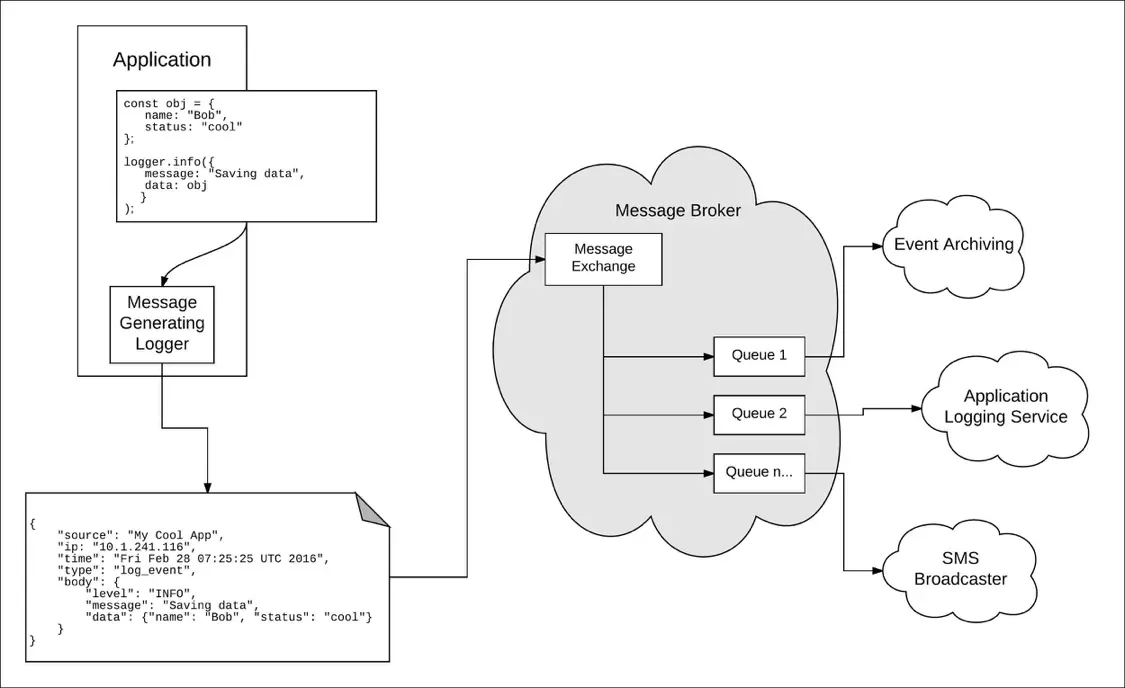
Taking a Message-Based Approach to Logging
Robert Reselman
Detection and Response
6 Best Practices for Effective IT Troubleshooting
Robert Reselman

Security Operations
3 Steps to Building an Effective Log Management Policy
Robert Reselman

Security Operations
3 Core Responsibilities for the Modern IT Operations Manager
Robert Reselman
