In October, Rapid7 researchers uncovered a significant vulnerability in the Nine mobile application for Android. Baldly stated, this app leaks Microsoft Exchange user credentials, plus mail envelopes and attachments, mailbox synchronization data, caleandar entries and tasks to attackers. It has been identified with a Common Vulnerabilities and Exposures (CVE) ID – namely, CVE-2016-6533 – though no formal corresponding entry is currently available in the CVE database. At present, the Nine app (also known as NineFolders) is available through the Google Play store and has been installed somewhere between half-a-million and one million times.
What’s the Danger?
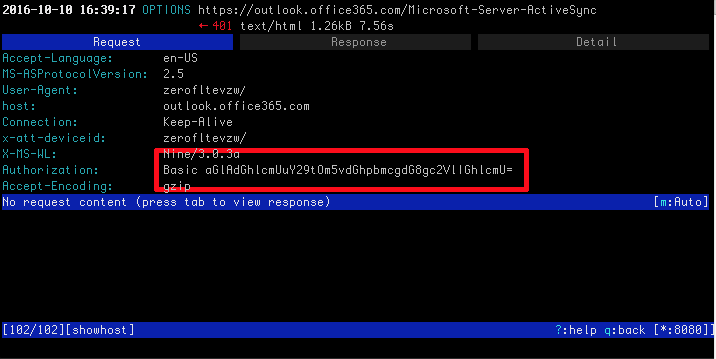
The biggest risk from this vulnerability comes from a man-in-the middle attack, which could be foisted by an attacker with privileges on the same network as the mobile device running the Nine app. Potentially, traffic from the Android device to an Exchange server, or to outlook.office365.com, for organizations using Outlook365 corporate email, could be sniffed. According to the researchers, attacks may easily be launched in open wireless environments, or by enticing Nine users to access the Internet using a rogue wireless access point (WAP) under their direction and control. This might mean, for example, that an attacker could set up a mobile WAP using an innocuous-seeming yet attractive SSID like “Starbucks” or “MacDonalds” that was bridged to a 3G/4G mobile data connection. Then, the attacker could funnel secure HTTP (HTTPS) traffic to a proxy that serves self-signed certificates from any certificate authority. In this kind of situation, the attacker need merely wait for a Nine user to come within range of the rogue WAP. Because communication between the Nine app and a remote Exchange ActiveSync service often happens when the victim opens his or her phone, when an email is received (and push enabled), or when the phone polls the remote service, exposure of credentials is highly likely. All communications packets include those credentials in an HTTP basic authentication header, and Nine does not perform certificate validation to make sure the certificate is valid and current (not revoked). Likewise, DNS queries for the Exchange server are vulnerable in the same way from the Nine app.
This decrypted capture of traffic sniffed using mitmproxy, an open source hacking tool, shows that account credentials appear in Base64 encoded form:
Plugging the Leak!
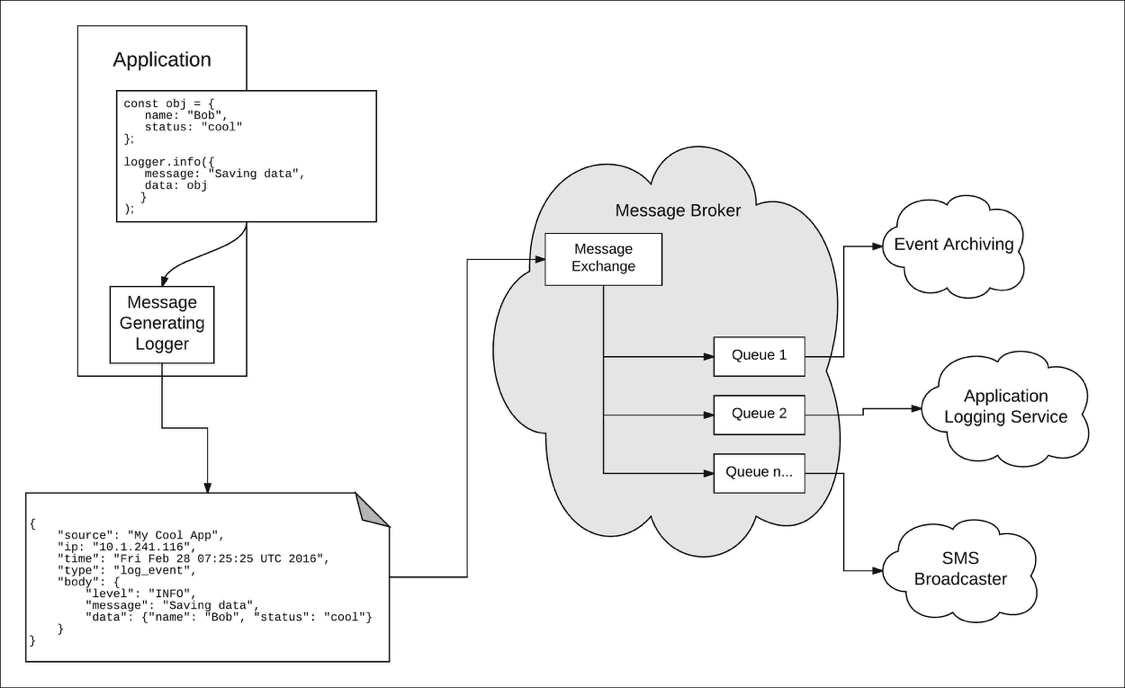
Fortunately, there is a definitive fix for this vulnerability. Users can disable push synchronization in Nine and synchronize manually, one when they’re on a trusted network (never on a public wifi of any kind), or using a VPN connection into a trusted network. Relying entirely on users is never a good idea, so IT administrators should look for MUA strings that begin with “Nine-“ to flag the app’s use in the ActiveSync logs. Then, they can determine what those users who are currently using the NineFolders app to access organization data should do. Organizations with access to Rapid7’s Logentries can identify such clients simply by searching for where(/Nine-/i) in the query bar. They can then email those users with detailed instructions on how to disable push, and under what circumstances manual synchronization is allowed. Given that organizations do not want blanket disclosure of client credentials for Exchange they should consider implementing a forced password change as part of the notification process as well.
Ready to improve the performance and security of your systems? Search your logs for this and other vulnerabilities, centralize logs from your servers and infrastructure in one place, and alert on key events in your environment with a Logentries account. Start a Logentries free 30-day trial.