Rapid7 is pleased to announce that we have released new Cloud Configuration Assessment capabilities in our InsightVM vulnerability management solution. Security teams can now access a security-focused, centralized view of AWS resources and misconfiguration risks within the same tool they already use to manage vulnerabilities across their on-premises and cloud environments. This new functionality empowers lean security teams to secure their business infrastructure far more quickly and comprehensively than ever before.
Securing the cloud: A complex challenge
Security teams face multiple challenges in managing potential cloud configuration vulnerabilities. Without the necessary visibility into cloud resources that DevOps and other teams in the company may quickly spin up or down depending on rapidly shifting business priorities, security organizations are hard pressed to properly evaluate the risk in their cloud environments before those threats become serious.
Since cloud resources are often abstracted and can appear complex, security professionals may have difficulty understanding how best to manage and assess cloud configurations unless they have received specialized training. As a result, security teams often spend too much time trying to uncover risk and not enough time actually remediating the most urgent issues facing the company—especially if they are relying on a combination of point solutions that sap team productivity and lead to console fatigue.
Unfortunately, the productivity obstacles experienced by security teams can create damaging consequences for the business. Cloud misconfiguration is a leading cause of data breaches, whether via data leaks or other means. Until now, companies running on hybrid infrastructure as well as businesses hoping to move into the cloud have faced unnecessarily burdensome challenges when attempting to secure their cloud environments.
Achieve better cloud security through complete visibility
Cloud Configuration Assessment capabilities, now available in InsightVM, alleviate these pain points, helping security teams identify and remediate cloud vulnerabilities with far greater speed. This functionality automatically prepares and organizes a comprehensive list of AWS account settings, providing security teams with a full view of their company’s existing AWS configurations across multiple accounts and regions.
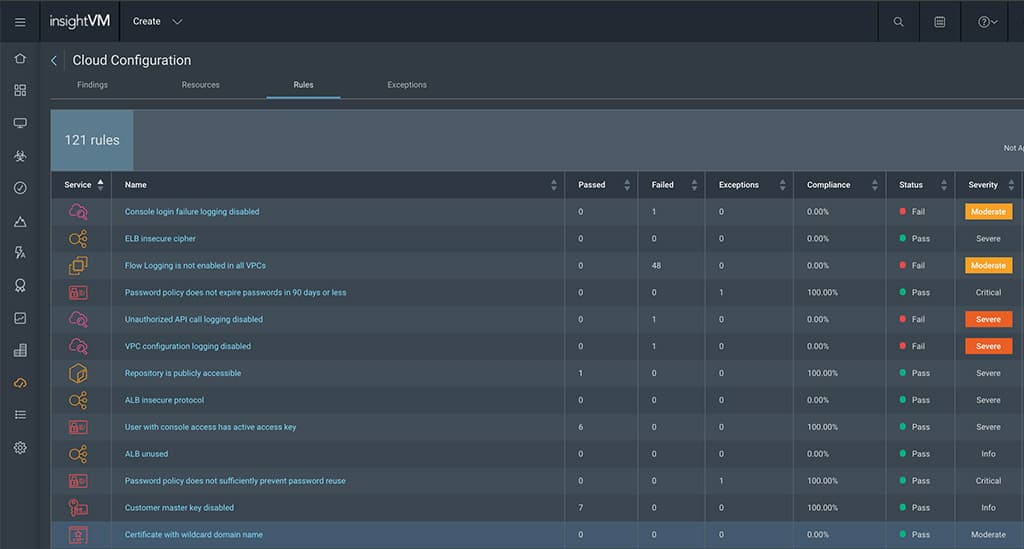
Equipped with these insights, security professionals can now evaluate AWS security configuration settings on a range of resources including EC2 instances, S3 buckets, relational database shares (RDSes), and virtual private clouds (VPCs). These configuration settings are then compared against the industry-standard benchmark, CIS AWS Foundations Benchmark. Results can be searched and filtered as needed. Security teams can view lists of failed rules against the CIS Benchmark, access findings by severity, spot compliance gaps, and even evaluate compliance with subsets of the benchmark. Security professionals can also view which accounts have the highest level of potential risk based on failed rules.
By clicking into any of these areas, security professionals can view greater detail on specific AWS findings if desired. A proof for each vulnerability is provided along with recommendations for remediation. With this detailed guidance in hand, security professionals can more effectively remediate vulnerabilities in collaboration with their DevOps and CloudOps colleagues.
Businesses can view AWS cloud configuration settings from within InsightVM regardless of how their AWS accounts were originally set up. Security teams can create individual connections for various AWS accounts in use at the company or create a single IAM role that has access to all the AWS resources. From there, it is easy to add new connections or manage existing ones.
Securely advance your business in the cloud
With visibility into AWS cloud configurations, security teams can manage a fuller scope of risk in their environment across on-premises and cloud settings using the familiar InsightVM tools they already have in place. Freed from unnecessary uncertainty about how to manage cloud vulnerabilities and equipped with powerful insights that leverage best practices, resource-constrained security teams can quickly and effectively secure AWS cloud resources.
Watch this 5-minute demo to Cloud Configuration Assessment in action:
With these new Cloud Configuration Assessment Capabilities now available in InsightVM, organizations can better understand and manage risks associated with their cloud infrastructure while still capitalizing on the business benefits found in the cloud.
Not an InsightVM customer? Scan for vulnerabilities and cloud misconfigurations today with our free trial
Get StartedRelated blog posts

Vulnerabilities and Exploits
CVE-2026-0265: Authentication Bypass in Palo Alto Networks PAN-OS
Rapid7

Vulnerabilities and Exploits
Critical Buffer Overflow in Palo Alto Networks PAN-OS User-ID Authentication Portal (CVE-2026-0300)
Jonah Burgess

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen

Vulnerabilities and Exploits
CVE-2025-20333, CVE-2025-20362, CVE-2025-20363 - Multiple critical vulnerabilities affecting Cisco products
Ryan Emmons