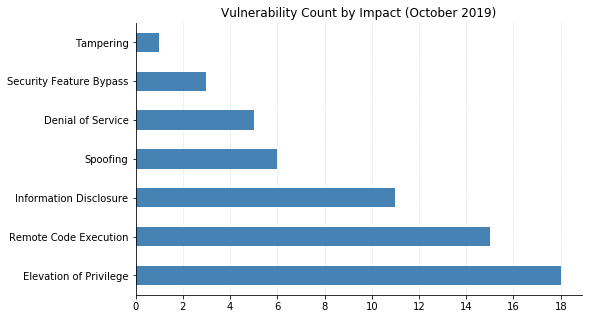
This month's Patch Tuesday is mainly notable in that there isn't a whole lot to note, which is a change of pace. No 0-days, no vulnerabilities that had been publicly disclosed already, and nothing that could allow worms to proliferate. And nothing from Adobe. Of course, that doesn't mean there's nothing to do: Microsoft still published 59 CVEs today. And in case you missed it, Microsoft released an out-of-band fix for Internet Explorer (IE) two weeks ago for a Remote Code Execution (RCE) vulnerability seen exploited in the wild (CVE-2019-1367).
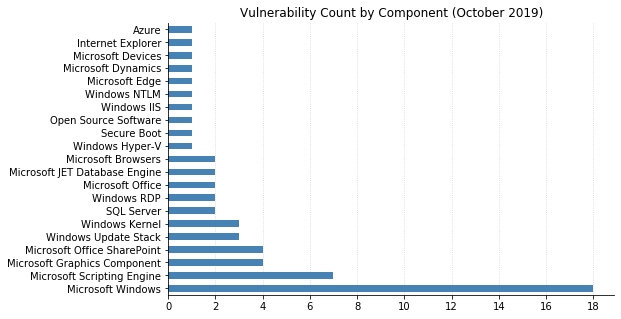
The majority of vulnerabilities patched by Microsoft this month affect their core Windows product, including two Remote Desktop Protocol (RDP) vulnerabilities. CVE-2019-1333 allows RCE against clients that can be convinced to connect to a malicious server, and CVE-2019-1326 is a denial of service vulnerability that could be used to cause an RDP server to stop responding. Both affect all supported versions of Windows.
As usual, there are also fixes for Microsoft's browsers. CVE-2019-1238 is an RCE vulnerability in the VBScript engine, which affects IE as well as any component that hosts the IE rendering engine – for example, an ActiveX control in an Office document. A couple of vulnerabilities in Excel were also patched: CVE-2019-1327 and CVE-2019-1331 could allow RCE if a user were to open a malicious file.
On the server side, a privilege elevation vulnerability in IIS was patched (CVE-2019-1365). This was due to the classic programming errors of failing to sanitize an incoming web request and not checking the length of a buffer before copying memory to it. SharePoint Server also got four fixes: cross-site scripting (CVE-2019-1070), spoofing (CVE-2019-1328), and two elevation of privilege vulnerabilities (CVE-2019-1329 and CVE-2019-1330). All were fixed by sanitizing incoming web requests.
Microsoft also acknowledged a security feature bypass on Windows 10 Mobile, but does not plan to release a fix. CVE-2019-1314 allows users to access files and folders through the locked screen when Cortana assistance is enabled. The workaround is to disable the Lock Screen option in the Cortana app settings.
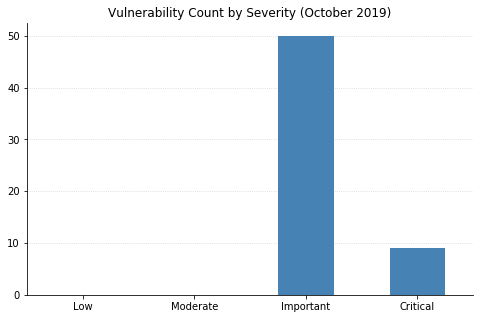
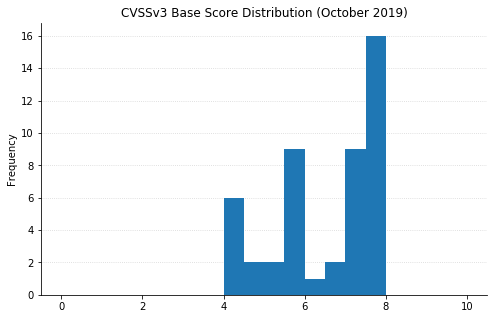
Note: not all CVEs had CVSSv3 data available at the time of writing