After four days of competition and a whole lot of “trying harder,” we have the winners of this year's Metasploit community CTF. We've included some high-level stats from the game below; check out the scoreboard here. If you played the CTF and want to let the Metasploit team know which challenges you found exhilarating, interesting, or infuriating (in a good way, of course), we have a feedback survey up here:
https://forms.gle/fnsuCeGxmELiqcMg7
Congratulations to everyone who teamed up with community members, learned something new, or captured flags. The collaboration we saw on Slack and Twitter was awesome as always!
I would say that we apologize for the constant reminder that the flags are IN the computer, but...I’d be lying. Please forgive us; we have to amuse ourselves somehow.
Winners
| Standing | Team |
|---|---|
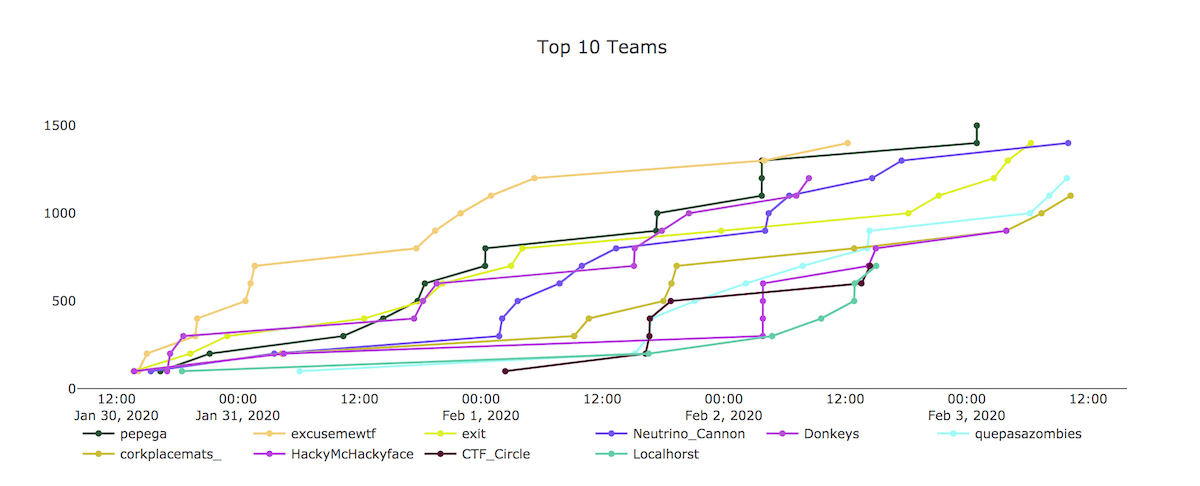
| First place | pepega |
| Second place | excusemewtf |
| Third place | exit |
We'll be in touch with winners shortly to arrange prize delivery. Big thanks to CTFd for providing technology that helped power the game, and thanks to our friends at Hack The Box for chipping in cool prizes!
Stats!
- 521 teams logged in and played over the course of the game. While this nets out to thousands of people working together to play, we know there were many more folks who wanted to register but couldn’t. Next time around, we’ll consider nixing pre-registration altogether and having sign-up concurrent with game play so we can ensure as close to 100% participation as possible.
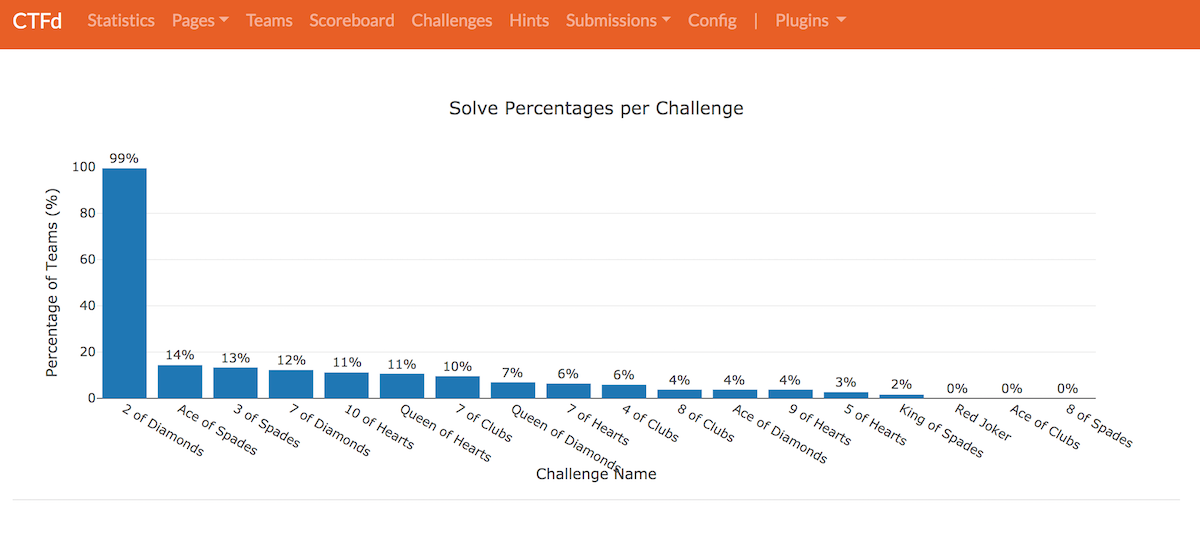
- This was the first CTF where nobody captured all the flags. Don’t feel bad, though: it was also the game with the highest-yet flag count, with 18 challenges in total. The top team captured 15 of ‘em, with a few others coming in at 12 and 14. Only seven teams got more than 10 flags. Congrats to everyone on persevering and learning.
- 188 teams made it onto the scoreboard. Congrats to all of you who captured your first-ever flag in this year's game!
- Our emeritus challenge 2 of Diamonds had the highest number of solves (187), followed by Ace of Spades (27).
- Red Joker, Ace of Clubs, and 8 of Spades had no solves at all. We’ll probably cycle these into the next game, whenever that turns out to be!
- 386 correct MD5 hashes were submitted. We got 1984 incorrect submissions (how apt?).
As in previous years, it's possible that the hacker community will come out with detailed write-ups on how they solved some or all of this year's challenges. We'll do our best to list a few of those here as they roll in. You can also check out #metasploit-ctf and #write-up-links in Slack for solution discussions.
Cheers to everyone who made the competition a fun and educational experience, not least of all our diabolical yet lovable gamemakers: zeroSteiner, wvu, space, tychos_moose, n00tmeg, juggernot, erinbleiweiss, pebarry, Dean, Op3n4m3, hairy_mongrel, Adam C., and the inimitable busterb. May your shells be merry and bright.