129 Vulnerabilities Patched in Microsoft's September 2020 Update Tuesday (2020-Sep Patch Tuesday)
Despite maintaining the continued high volume of vulnerabilities disclosed and patched this month, Microsoft's 129-Vulnerability September 2020 Update Tuesday is seemingly calm from an operations perspective -- at first glance.
While following standard procedures of scheduling the patching for Windows OSes up front immediately closes the door against 60%+ of the vulnerabilities being disclosed this month, there is a slight uptick in Critical Vulnerabilities (23 in September versus 17/18 in August/July respectively) which land on our Server friends Exchange Server and SharePoint.
Microsoft CVE-2020-16875: Microsoft Exchange Remote Code Execution Vulnerability
The first vulnerability to note comes from Microsoft Exchange Server. CVE-2020-16875 is a CVSS 8.4-scoring remote code execution vulnerability. In this scenario, Microsoft explains that the vulnerability occurs due to improper validation of cmdlet arguments.
However, there are limitations on this attack which reduces the attack surface a bit. In order for exploitation, the attack must be triggered off an authenticated user within a specific Exchange role. Under those conditions, a successful exploit could allow arbitrary code to run in the context of the System user.
Update (September 22, 2020): Updated description of CVE-2020-16875 as more information from Microsoft became available.
Microsoft SharePoint Remote Code Execution Vulnerability CVE-2020-1210, CVE-2020-1595 and more
A substantial portion of critical vulnerabilities marked by Microsoft came from SharePoint this month. Unfortunately, this set of seven remote code execution vulnerabilities (CVE-2020-1576, CVE-2020-1452, CVE-2020-1453, CVE-2020-1200, CVE-2020-1460, CVE-2020-1210, CVE-2020-1595) don't apply to all versions of SharePoint. Below is a summary of the various affect products and the associated CVEs within this set. Please make note of multiple patches required to cover this set of remote code execution vulnerabilities ranging from CVSS 8.5 to 9.9.
| Product | CVE-2020-1595 | CVE-2020-1200 | CVE-2020-1210 | CVE-2020-1576 | CVE-2020-1460 | CVE-2020-1453 | CVE-2020-1452 | Patches |
|---|---|---|---|---|---|---|---|---|
| Business Productivity Servers 2010 SP2 | x | KB3101523 | ||||||
| SharePoint Enterprise Server 2013 SP1 | x | x | x | x | x | x | KB4484515, KB4484480 | |
| SharePoint Enterprise Server 2016 | x | x | x | x | x | x | x | KB4484506, KB4484512 |
| SharePoint Foundation 2010 SP2 | x | x | x | x | x | KB4486667 | ||
| SharePoint Foundation 2013 SP1 | x | x | x | x | x | x | KB4484525, KB4484488 | |
| SharePoint Server 2010 SP2 | x | x | KB4486664 | |||||
| SharePoint Server 2019 | x | x | x | x | x | x | x | KB4484505 , KB4484504 |
The set of vulnerabilities can result in arbitrary code being run off in the context of the SharePoint Application Pool, the SharePoint server farm account or both. The two notable of this set of seven are CVE-2020-1210 stemming from a flaw in how SharePoint checks the source markup of application packages while CVE-2020-1595 triggers off specially-formatted input being sent to a susceptible API.
Microsoft CVE-2020-1440: Microsoft SharePoint Server Tampering Vulnerability
Continuing on the SharePoint train, we reach an odd one marked as Impact: Tampering. It's not often that we see Tampering used as an impact category. Fortunately, the description on this vulnerability does say prior authentication on an affected SharePoint Server is required, but with that in hand, an attacker can target specific users and alter the targets profile data.
Regardless of the attack vector, it makes sense to place priority on patching up affected SharePoint servers this month.
Additional Statistics
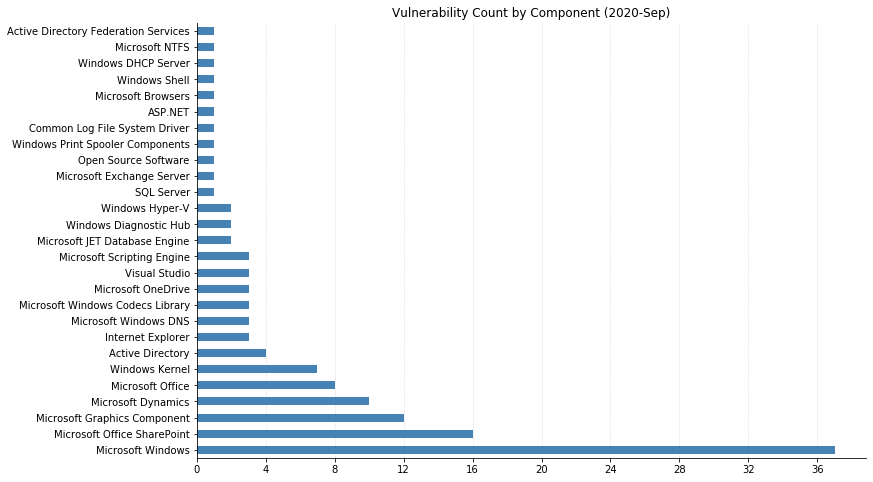
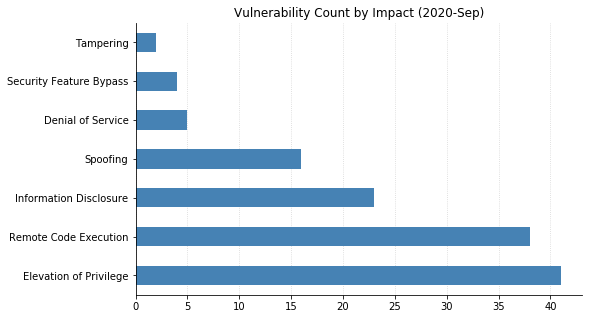
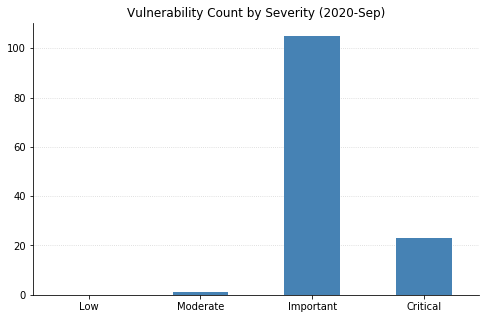
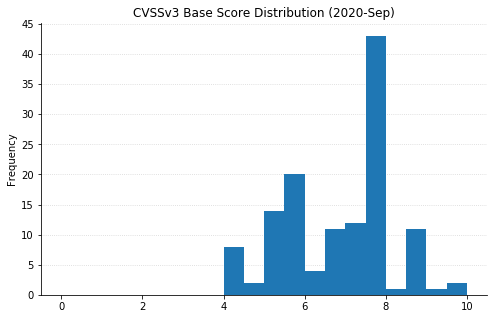
Note: Graph data is reflective of data presented by Microsoft's CVRF at the time of writing.
Related blog posts

Exposure Management
Patch Tuesday - May 2026
Adam Barnett

Artificial Intelligence
Project Glasswing and the Next Challenge for Defenders: Turning Faster Discovery into Faster Action
Craig Adams

Exposure Management
Patch Tuesday - April 2026
Adam Barnett

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen
