As we kick off 2021 here at Rapid7, we wanted to take a minute to reflect on 2020, highlight some key InsightIDR product investments we don’t want you to miss, and take a look ahead at where our team sees detection and response going this year.
Rapid7 detection and response 2020 highlights
Whenever we engage with customers or industry professionals, one theme that we hear on repeat is complexity. It can often feel like the cards are stacked against security teams as environments sprawl and security needs outpace the number of experienced professionals we have to address them. This dynamic was further amplified by the pandemic over the past year. Our focus over the past 12 months has been on enabling teams to work smarter, get the most out of our software and services, and accelerate their security maturity as efficiently as possible. Here are some highlights from our journey over 2020:
A more efficient and customizable Log Search
In 2020, we made continuous enhancements to our Log Search feature to make it more efficient and customizable to customers’ needs. Now, you can:
- See a more detailed view into your log data with one single query with LEQL Multi-groupby.
- Easily define what to parse from logs to extract the log data that is most relevant to your organization with the Custom Pasing Tool. Learn more in our blog post.
- Analyze security data faster with Visual Search in InsightIDR.
For a look at the most up-to-date list of Log Search capabilities, check out our help documentation here.
Greater visibility across the attack surface with Network Traffic Analysis
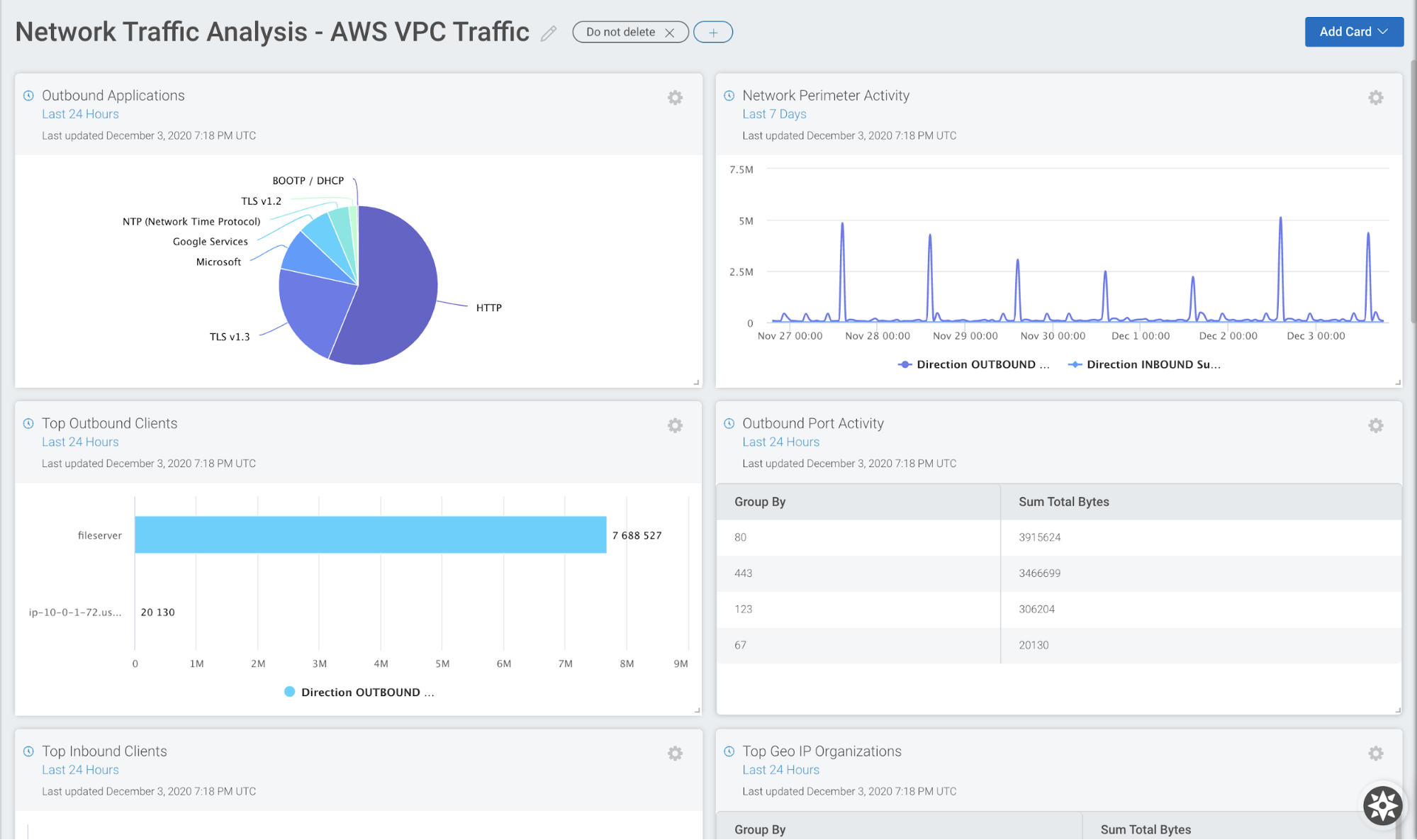
With Rapid7’s lightweight Insight Network Sensor, customers can monitor, capture, and assess end-to-end network traffic across their physical and virtual environments (including AWS environments) with curated IDS alerts, plus DNS and DHCP data. For maximum visibility, customers can add on the network flow data module to further investigations, deepen forensic activities, and enable custom rule creation.
The real-time visibility provided by InsightIDR’s Network Traffic Analysis has been especially helpful for organizations working remotely over the past year. Many customers are building custom InsightIDR dashboards to improve real-time monitoring of activity within their networks and at the edge to maintain optimal security as teams work from home.
Learn about how to leverage NTA and more by checking out our top Network Traffic blogs of 2020:
- The Importance of Network Visibility With a Remote Workforce
- How Rapid7 Customers Are Using Network Traffic Analysis in Detection and Response
- Top 5 Ways to Get a Network Traffic Source on Your Network
Complete endpoint visibility with Enhanced Endpoint Telemetry
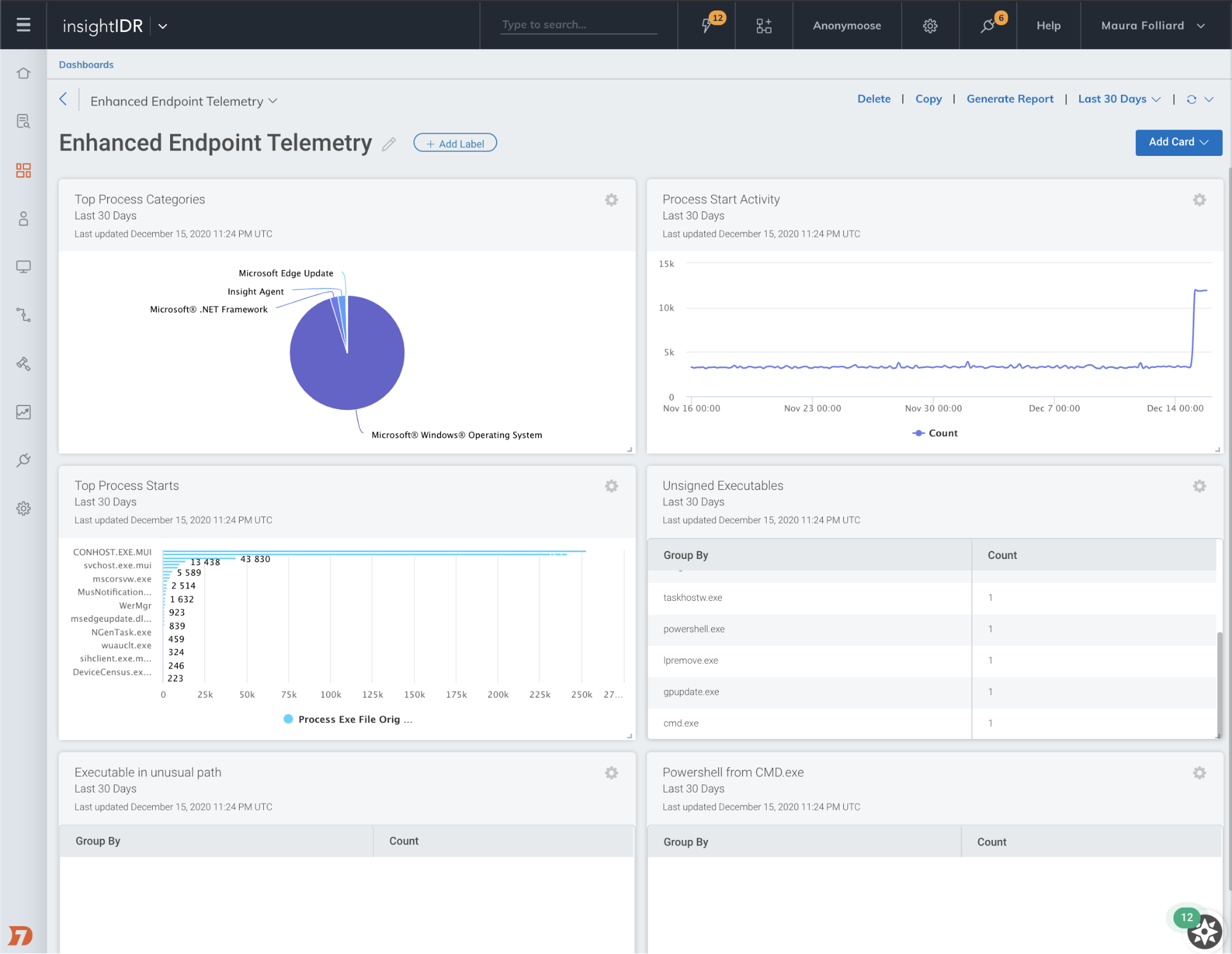
InsightIDR’s latest add-on module, enhanced endpoint telemetry (EET), brings the enhanced endpoint data that’s currently used by Rapid7’s Managed Detection and Response (MDR) Services team in almost all of their investigations into InsightIDR.
Get a full picture of endpoint activity, create custom detections, and see the full scope of an attack with EET’s process start activity data in Log Search. These logs give visibility into all endpoint activity to tell a story around what triggered a particular detection and to help inform remediation efforts. As remote working has increased for many organizations, so has the number of remote endpoints security teams have to monitor—the level of detail provided by EET helps teams detect and proactively hunt for custom threats across their expanding environments.
Learn more about the benefits of EET in our blog post and how to get started in our help documentation.
SOC automation with InsightIDR and InsightConnect
Automation is critical for accelerating and streamlining incident response, especially as the threat landscape continues to evolve in 2021 and beyond. This is why we have built-in automation powered by InsightConnect, Rapid7’s Security Orchestration Automation and Response (SOAR) tool, at the heart of InsightIDR. SOC automation with InsightIDR and InsightConnect allows customers to auto-enrich alerts, customize alerting and escalation pathways, and auto-contain threats.
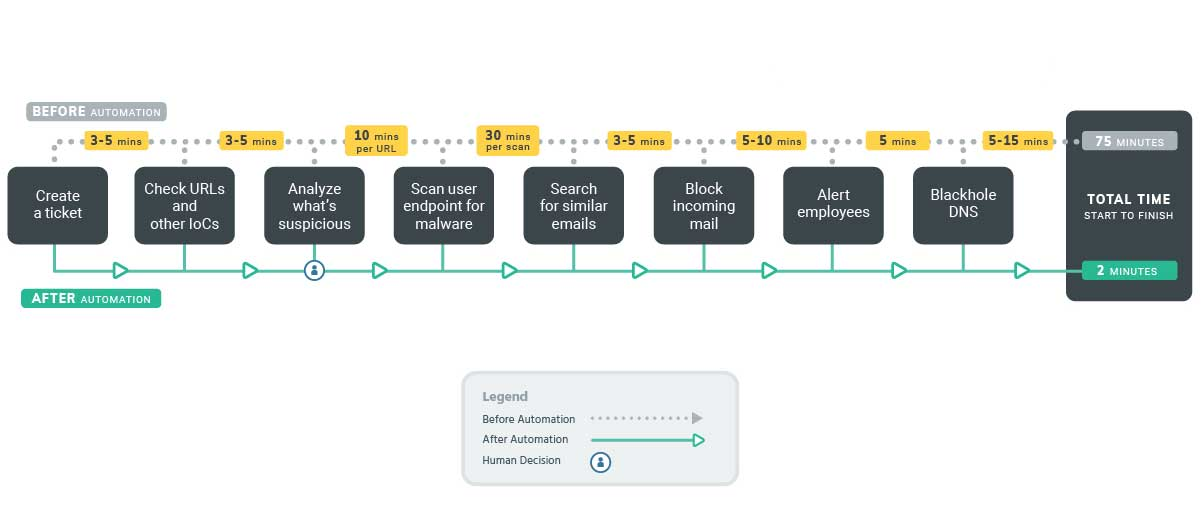
In 2020, we furthered the integration between InsightIDR and InsightConnect—in addition to kicking off workflows from User Behavior Analytics (UBA) alerts, joint customers can now trigger custom workflows to automatically initiate predefined actions each time a Custom Alert is triggered in InsightIDR.
Learn more about the benefits of leveraging SIEM and SOAR by checking out the blogs below:
- 2021 Detection and Response Planning: Why 2021 Is the Year for SOC Automation
- Accelerating Threat Detection and Response with SIEM and SOAR
MDR Elite “Active Response” for end-to-end detection and response
Only Rapid7 MDR with Active Response can reduce attacker dwell time and save your team time and money with unrivaled response capabilities on both endpoint and user threats. Whether it’s a suspicious authentication while you’re buried in other security initiatives or an attacker executing malicious documents at 3 a.m., you can be confident that Rapid7 MDR is watching and responding to attacks in your environment.
With MDR Elite with Active Response, our team of SOC experts provide 24x7 end-to-end detection and response to immediately limit an attacker’s ability to execute, giving you and your team peace of mind that Rapid7 will take action to protect your business and return the time normally spent investigating and responding to threats back to your analysts.
2020 Rapid7 detection and response achievements
At Rapid7, we're grateful to have received multiple recognitions from analysts and customers alike for our Detection and Response portfolio throughout 2020, including:
- Named a Leader in 2020 Gartner Magic Quadrant for Security Information and Event Management
- Named a 2020 Gartner Peer Insights Customers’ Choice for Security Information Event Management
- Named a Leader in The Forrester Wave™: Midsize Managed Security Services Providers, Q3 2020
- Recognized as a Strong Performer in The Forrester Wave™: Security Analytics Platforms, Q4 2020.
We’re so thankful to our customers for your continued partnership and feedback throughout the years. As we move into 2021, we’re excited to continue to invest in driving effective and efficient detection and response for teams.
What’s ahead in 2021
As we move forward in 2021, it’s clear that things aren’t going to jump back to “normal” anytime soon. Many companies continue to work remotely, increasing the already present need for security tools that can keep teams safe and secure.
In 2020, a big theme for InsightIDR was giving teams advanced visibility into their environments. What’s ahead in 2021? More capabilities that help security teams do their jobs faster and more effectively.
Sam Adams, VP of Engineering for Detection and Response at Rapid7 reflected, "In 2020, InsightIDR added a breadth of new ways to detect attacks in your environment, from endpoint to network to cloud. In 2021, we want to add depth to all of these capabilities, by allowing our customers fine-grained tuning and customization of our analytics engine and an even more robust set of tools to investigate alerts faster than ever before.”
When speaking about the detection and response landscape overall, Jeffrey Gardner, a former healthcare company Information Security Officer and recently appointed Practice Advisor for Detection and Response at Rapid7, said, “I think the broader detection industry is at this place where there’s an overabundance of data—security professionals have this feeling of ‘I need these log sources and I want this telemetry collected,’ but most solutions don’t make it easy to pull actionable intelligence from this data. I call out ‘actionable’ because most of the products provide a lot of intel but really leave the ‘what should I do next?’ completely up to the end user without guidance.”
InsightIDR targets this specific issue by providing teams with visibility across their entire environment while simultaneously enabling action from within the solution with curated built-in expertise through out-of-the-box detections, pre-built automation, and high-context investigation and response tools.
When speaking about projected 2021 cybersecurity trends, Bob Rudis, Chief Data Scientist at Rapid7, noted, “We can be fairly certain ransomware tactics and techniques will continue to be commoditized and industrialized, and criminals will continue to exploit organizations that are strapped for resources and distracted by attempting to survive in these chaotic times.”
To stay ahead of these new attacker tactics and techniques, visibility into logs, network traffic, and endpoint data will be crucial. These data sources contain the strongest and earliest indicators of potential compromise (as well as form the three pillars of Gartner’s SOC Visibility Triad). Having all of this critical data in a single solution like InsightIDR will help teams work more efficiently and effectively, as well as stay on top of potential new threats and tactics.
Related blog posts

Products and Tools
InsightIDR AI Alert Triage Automatically Classifies Alerts with 99.93% Benign Alert Accuracy
Chris Wraight

Detection and Response
New IDR Log Search Enhancements: Accelerate, Streamline, and Simplify Investigations
Rapid7

Products and Tools
What’s New in Rapid7 Products & Services: Q3 2024 in Review
Margaret Wei

Detection and Response
Rapid7 Named a Leader in IDC MarketScape: Worldwide SIEM for SMB and Enterprise
Meaghan Buchanan

