The warm weather is starting to roll in, the birds are chirping, and Spring... well, Spring4Shell is making a timely entrance. If you’re still recovering from Log4Shell, we’re here to tell you you're not alone. While discovery and research of CVE-2022-22965 is evolving, Rapid7 is committed to providing our customers updates and guidance. In this blog, we wanted to share some recent product enhancements across our application security portfolio to help our customers with easy ways to test and secure their apps against Spring4Shell.
What is Spring4Shell?
Before we jump into how we can help you with our products, let's give a quick overview of Spring4Shell. CVE-2022-22965 affects Spring MVC and Spring WebFlux applications running JDK versions 9 and later. A new feature was introduced in JDK version 9 that allows access to the ClassLoader from a Class. This vulnerability can be exploited for remote code execution (RCE). If you’re looking for more detailed information on Spring4Shell, check out our overview blog here.
Updated: RCE Attack Module for Spring4Shell
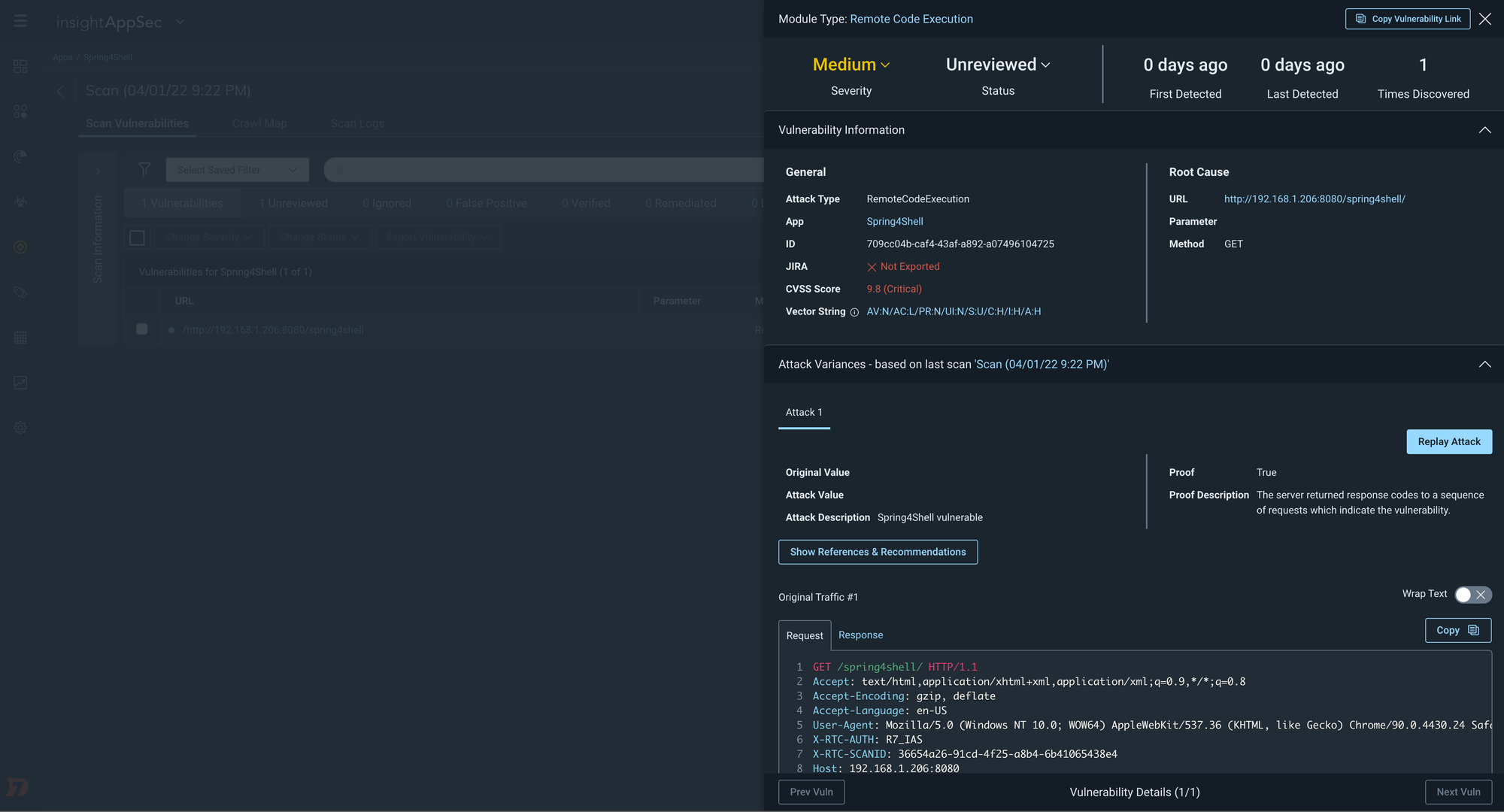
Customers leveraging InsightAppSec, our dynamic application security testing (DAST) tool, can regularly assess the risk of their applications. InsightAppSec allows you to configure 100+ types of attacks to simulate real-world exploitation attempts. While it may be April 1st, we’re not foolin’ around when it comes to our excitement in sharing this update to our RCE Attack Module that we’ve included in the default All Modules Attack Template – specifically testing for Spring4Shell.
Cloud customers who already have the All Modules Attack Template enabled will automatically benefit from this new RCE attack as part of their regular scan cadence. As of April 4th, customers with on-prem scan engines can also benefit from this updated RCE attack module. For those customers with on-premises engines, make sure to have auto-upgrades turned on to automatically benefit from this updated Attack Module, or update manually to the latest scan engine.
NEW: Block against Spring4Shell attacks
In addition to assessing your applications for attacks with InsightAppSec, we’ve also got you covered when it comes to protecting your in-production applications. With tCell, customers can both detect and block anomalous activity, such as Spring4Shell exploit attempts. Check out the GIF below on how to enable the recently added Spring RCE block rule in tCell.
NEW: Identify vulnerable packages (such as CVE-2022-22965)
A key component of Spring4Shell is detecting whether or not you have any vulnerable packages. tCell customers leveraging the Java agent can determine if they have any vulnerable packages, including CVE-2022-22965, in their runtime environment.
Simply navigate to tCell on the Insight Platform, select your application, and navigate to the Packages and Vulns tab. Here you can view any vulnerable packages that were detected at runtime, and follow the specified remediation guidance.
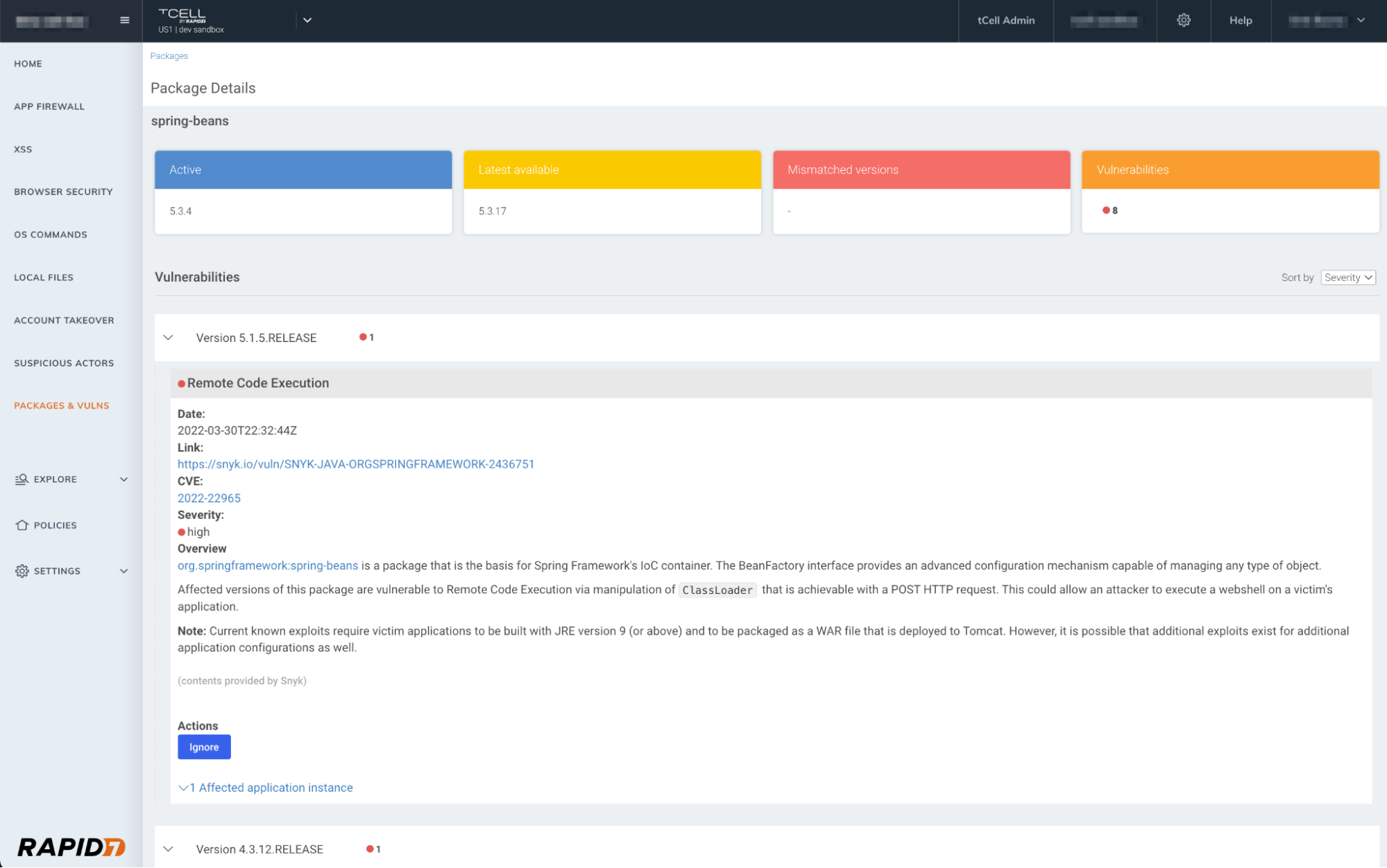
Currently, the recommended mitigation guidance is for Spring Framework users to update to the fixed versions. Further information on the vulnerability and ongoing guidance are being provided in Spring’s blog here.
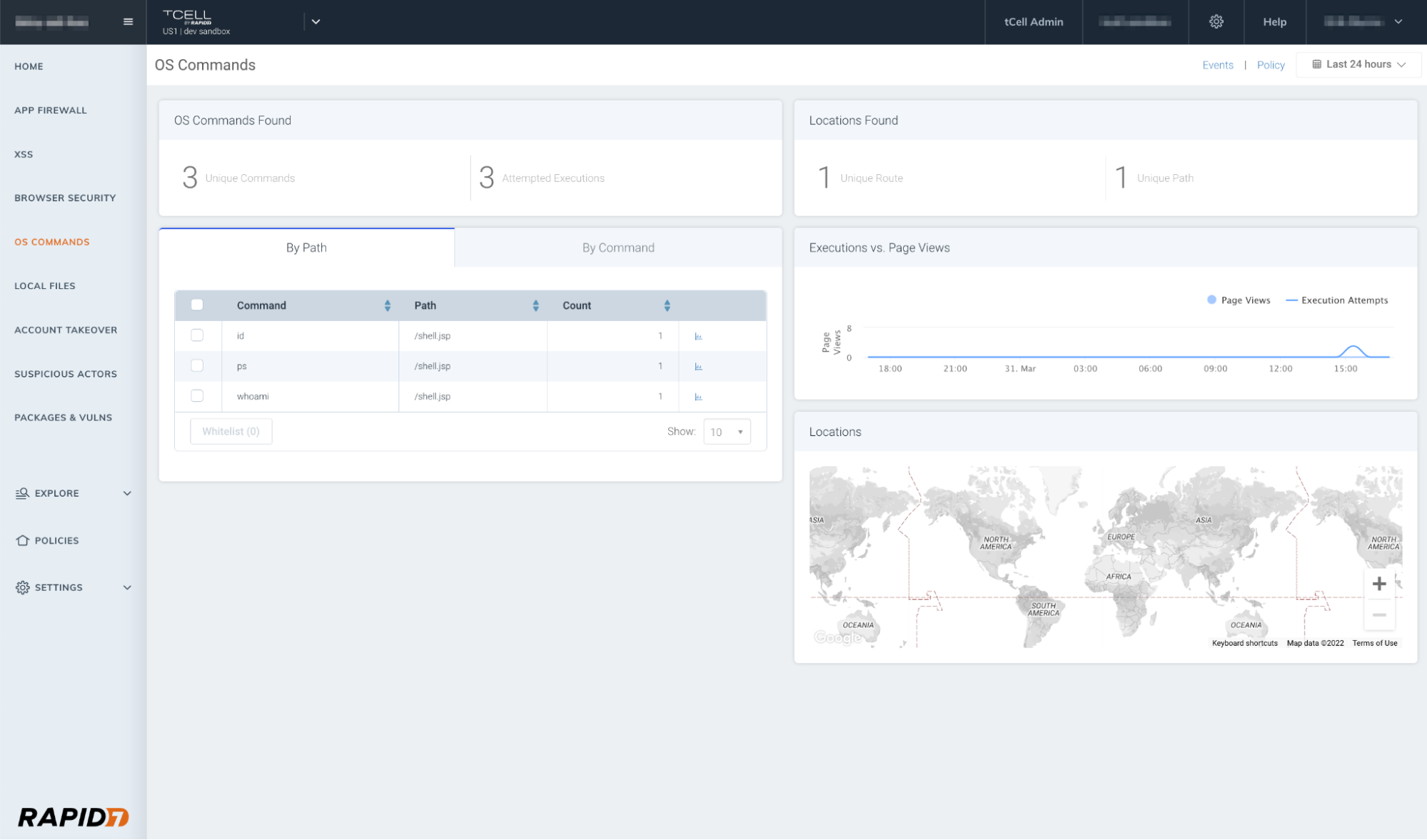
Utilize OS commands
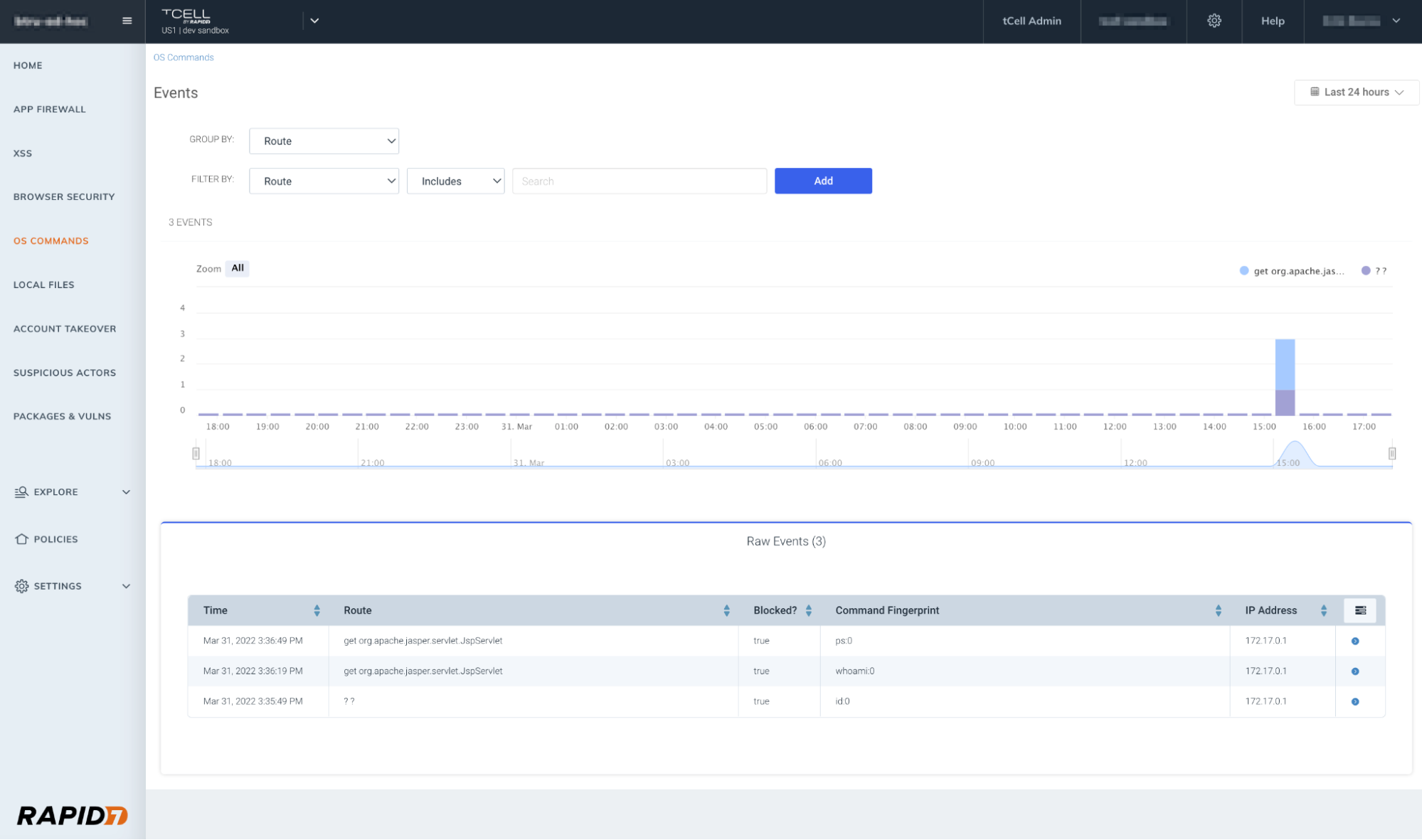
One of the benefits of using tCell’s app server agents is the fact that you can enable blocking (after confirming you’re not blocking any legitimate commands) for OS commands. This will prevent a wide range of exploits including Shell commands. Below you will see an example of our OS Commands dashboard highlighting the execution attempts, and in the second graphic, you’ll see the successfully blocked OS command events.
What’s next?
We recommend following Spring’s latest guidance on remediation to reduce risk in your applications. If you’re looking for more information at any time, we will continue to update both this blog. Additionally, you can always reach out to your customer success manager, support resources, or anyone on your Rapid7 account team. Happy April – and here’s to hoping the only shells you deal with in the future are those found on the beach!
Related blog posts

Exposure Management
Patch Tuesday - May 2026
Adam Barnett

Artificial Intelligence
Project Glasswing and the Next Challenge for Defenders: Turning Faster Discovery into Faster Action
Craig Adams

Exposure Management
Patch Tuesday - April 2026
Adam Barnett

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen
