ADCS - ESC Vulnerable certificate template finder
Our very own Grant Willcox has developed a new module which allows users to query a LDAP server for vulnerable Active Directory Certificate Services (AD CS) certificate templates. The module will print the detected certificate details, and the attack it is susceptible to. This module is capable of checking for ESC1, ESC2, and ESC3 vulnerable certificates.
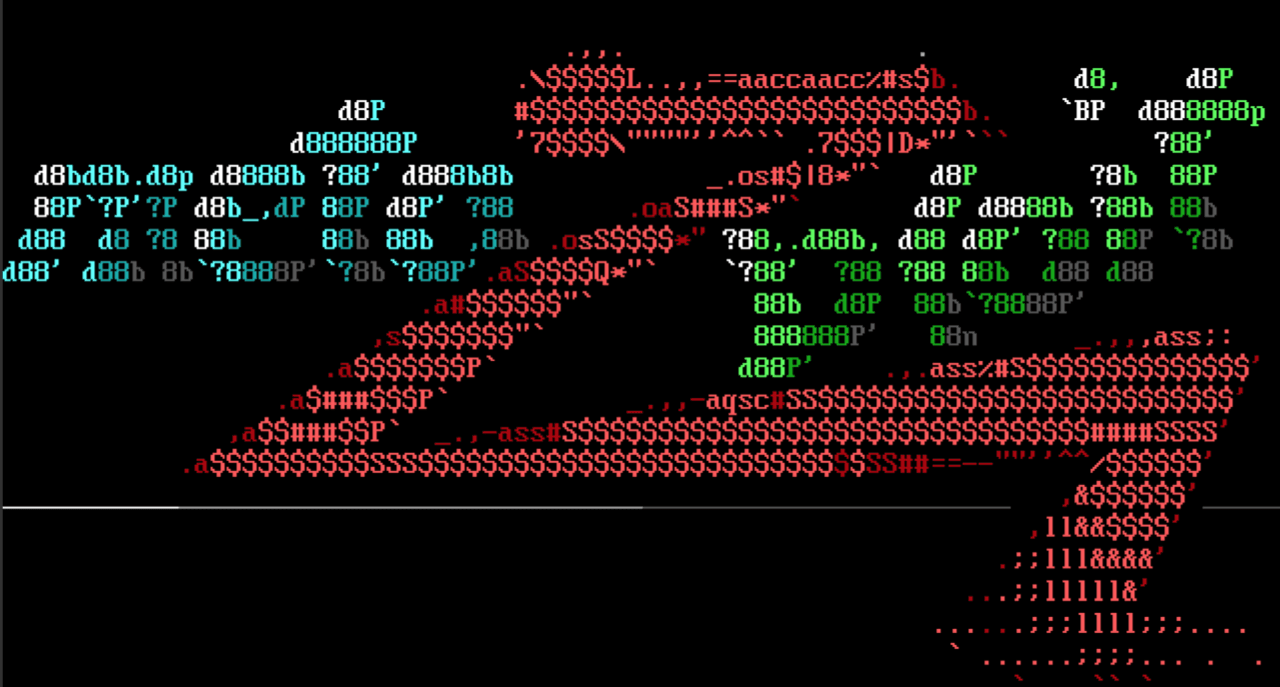
Example module output showing an identified vulnerable certificate template:
msf6 auxiliary(gather/ldap_esc_vulnerable_cert_finder) > run
[*] Running module against 172.26.104.157
[*] Discovering base DN automatically
[+] 172.26.104.157:389 Discovered base DN: DC=daforest,DC=com
[*] Template: SubCA
[*] Distinguished Name: CN=SubCA,CN=Certificate Templates,CN=Public Key Services,CN=Services,CN=Configuration,DC=daforest,DC=com
[*] Vulnerable to: ESC1, ESC2, ESC3_TEMPLATE_2
[*] Certificate Template Enrollment SIDs:
[*] * S-1-5-21-3290009963-1772292745-3260174523-512 (Domain Admins)
[*] * S-1-5-21-3290009963-1772292745-3260174523-519 (Enterprise Admins)
[*] Issuing CAs:
[*] * daforest-WIN-BR0CCBA815B-CA
[*] Server: WIN-BR0CCBA815B.daforest.com
[*] Enrollment SIDs:
[*] * S-1-5-11 (Authenticated Users)
... etc etc ...
SSL Scanner improvements
Community member h00die has made improvements to a new Metasploit’s SSL scanner modules, and combined the functionality of two existing modules auxiliary/scanner/http/ssl.rb auxiliary/scanner/http/ssl_version.rb into one new module auxiliary/scanner/ssl/ssl_version.rb. This new module has added checks for Deprecated protocols, expired/not valid certs, low key strength, Null cipher suites, certificates signed with MD5, DROWN, RC4 ciphers, exportable ciphers, LOGJAM, and BEAST.
Reduced Python payload sizes
Community member llamasoft has recently contributed improvements to our Python payloads, with the first change being a modification to the Python Meterpreter stage to calculate the necessary data for AES encryption at runtime - which helped reduce the stage size by about 6,000 bytes. This week’s Metasploit release includes compression support using zlib. This change reduces the size of the Python Meterpreter from 95kb to 24kb.
New module content (4)
- Misconfigured Certificate Template Finder by Grant Willcox - This adds a module that analyzes certificate templates to identify ones that are vulnerable to ESC1, ESC2 and ESC3. When a template is found to be vulnerable, the necessary information is printed for the user including the template name, the issuing CAs and the SIDs of the users that are able to issue them.
- SSL/TLS Version Detection by todb, Chris John Riley, Veit Hailperin, et, and h00die, which detects CVE-2022-3358 - A new module modules/auxiliary/scanner/ssl/ssl_version.rb has been released which replaces the old SSL scanners and offers improved features such as SSL cipher suite checking, improvements to CA Issuers logic, support for expired certs and depreciated protocols, and better error handling.
- Reverse Lookup IP Addresses by mubix and bcoles - Adds a new post/multi/recon/reverse_lookup module that reverse resolves an IP address or IP address range to hostnames. The old post/windows/gather/reverse_lookup and post/windows/recon/resolve_ip modules have been removed.
- Windows Gather Navicat Passwords by HyperSine and Kali-Team - This adds a post module that retrieves and decrypts passwords saved by Navicat.
Enhancements and features (6)
- #17211 from llamasoft - This compresses Python payloads using zlib to make them smaller.
- #17219 from jheysel-r7 - Update Zabbix login_scanner to work with version 6.2.4.
- #17223 from cgranleese-r7 - The reload_lib functionality has been updated so that its file change tracking logic better takes into account scenarios where files are modified. Previously if a breakpoint was inserted, removed, and then reload_lib -a was run, it would mistakenly use an old copy of the code.
- #17234 from cgranleese-r7 - Add references to info -d command in the options and info command outputs. This command allows you to generate a HTML document which you can use to view the full documentation of a module in your browser.
- #17235 from jmartin-r7 - Updates auxiliary/scanner/http/manageengine_desktop_central_login module to report the service name correctly as http or https.
- #17238 from zeroSteiner and NtAlexio2 - Adds the shutdown command to Window's Python Meterpreter.
Bugs fixed (3)
- #17177 from nzdjb - A bug has been fixed when searching for or attempting to use modules whereby trailing :'s were not handled appropriately as part of the input, and could lead to all modules in Metasploit being returned.
- #17221 from adfoster-r7 -A bug has been fixed that would cause crashes when generating payload sizes. Additionally, the code has been updated to ignore payload metadata for adaptor payloads when determining payload sizes.
- #17244 from zeroSteiner - A bug that could cause the hostname command to fail in Mettle versions of Meterpreter has been improved by adding increased validation to the hostname code.
- #17220 from adfoster-r7 - This fixes a crash in the peinject stage that would occur when the PE datastore option was not set.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).