Recog Release v3.0.3, which is available now, includes updated fingerprints for Zoho ManageEngine PAM360, Password Manager Pro, and Access Manager Plus; Atlassian Bitbucket Server; and Supervisord Supervisor. It also includes new fingerprints and a number of bug fixes, all of which are detailed below.
Recog is an open source recognition framework used to identify products, operating systems, and hardware through matching network probe data against its extensive fingerprint collection. Support for Recog is part of Rapid7’s ongoing commitment to open source initiatives.
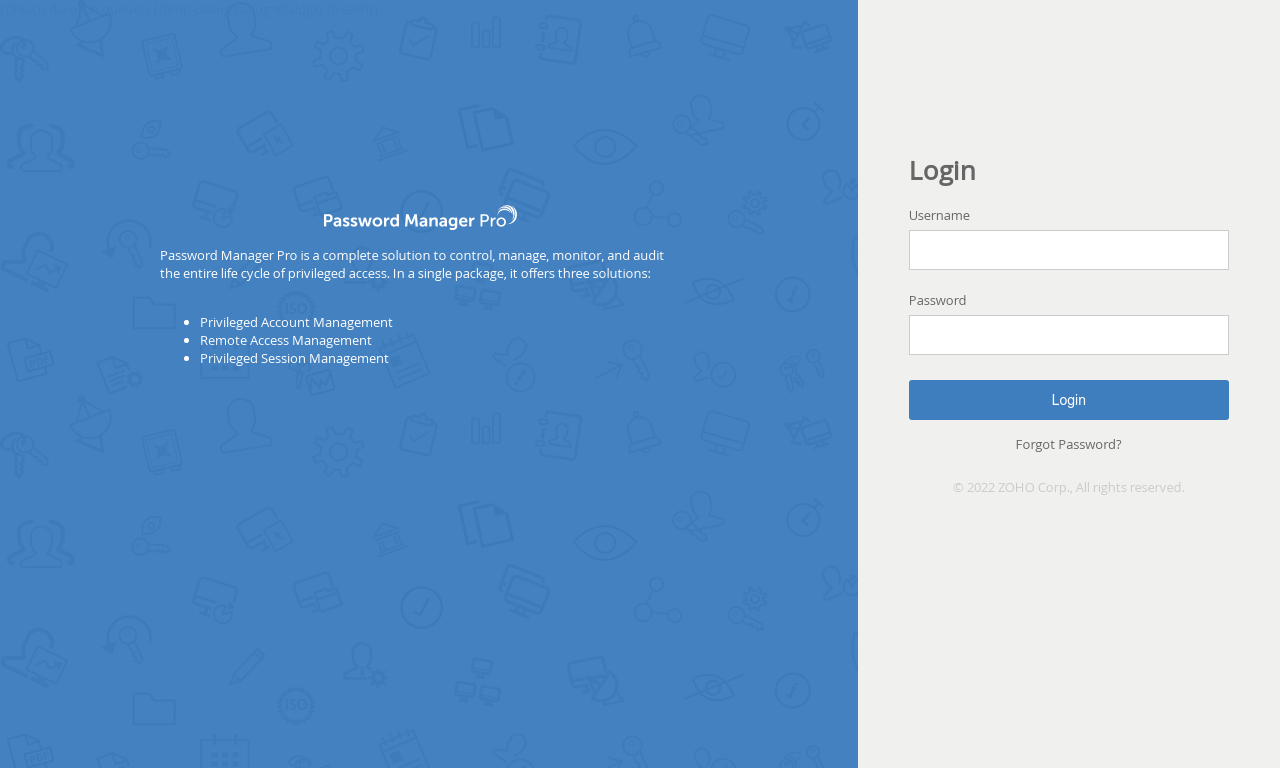
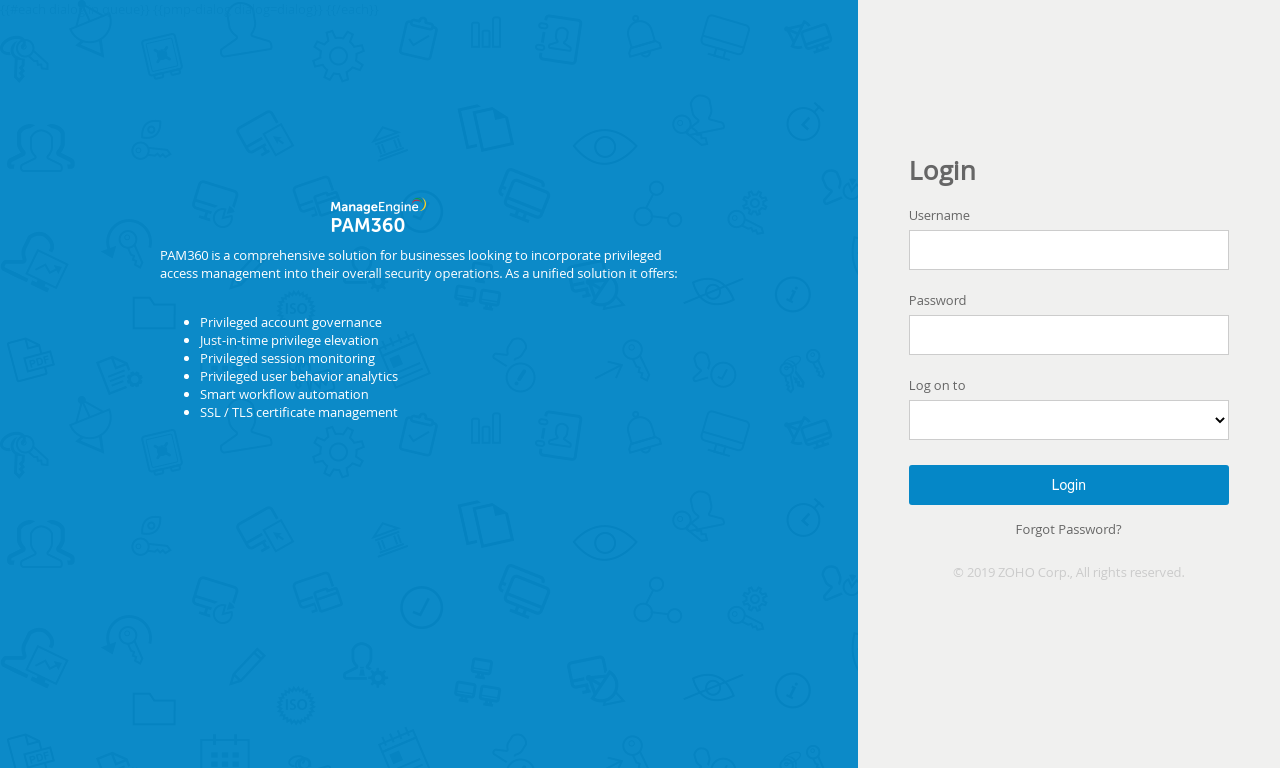
Zoho ManageEngine PAM360, Password Manager Pro, and Access Manager Plus
Fingerprints for these three Zoho ManageEngine products were added shortly after Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2022-35405 to their Known Exploited Vulnerabilities (KEV) catalog on September 22nd, 2022. Favicon, HTML title, and HTTP server fingerprints were created for both PAM360 and Password Manager Pro, and favicon and HTML title fingerprints were created for Access Manager Plus. PAM360 version 5500 (and older) and Password Manager Pro version 12100 (and older) are both vulnerable to an unauthenticated remote code execution (RCE) vulnerability, and Access Manager Plus version 4302 (and older) is vulnerable to an authenticated remote code execution (RCE) vulnerability. In addition, Grant Willcox contributed the Metasploit Zoho Password Manager Pro XML-RPC Java Deserialization exploit module which is capable of exploiting the unauthenticated vulnerability via the XML-RPC interface in Password Manager Pro and PAM360 and attaining RCE as the NT AUTHORITY\SYSTEM user.
More recently, on January 4th, 2023, Zoho released details of a SQL injection vulnerability (CVE-2022-47523) in PAM360 version 5800 (and older), Password Manager Pro version 12200 (and older) and Access Manager Plus version 4308 (and older). From a quick analysis of internet scan data there appears to be only about 76 Password Manager Pro and 21 PAM360 instances on the internet.
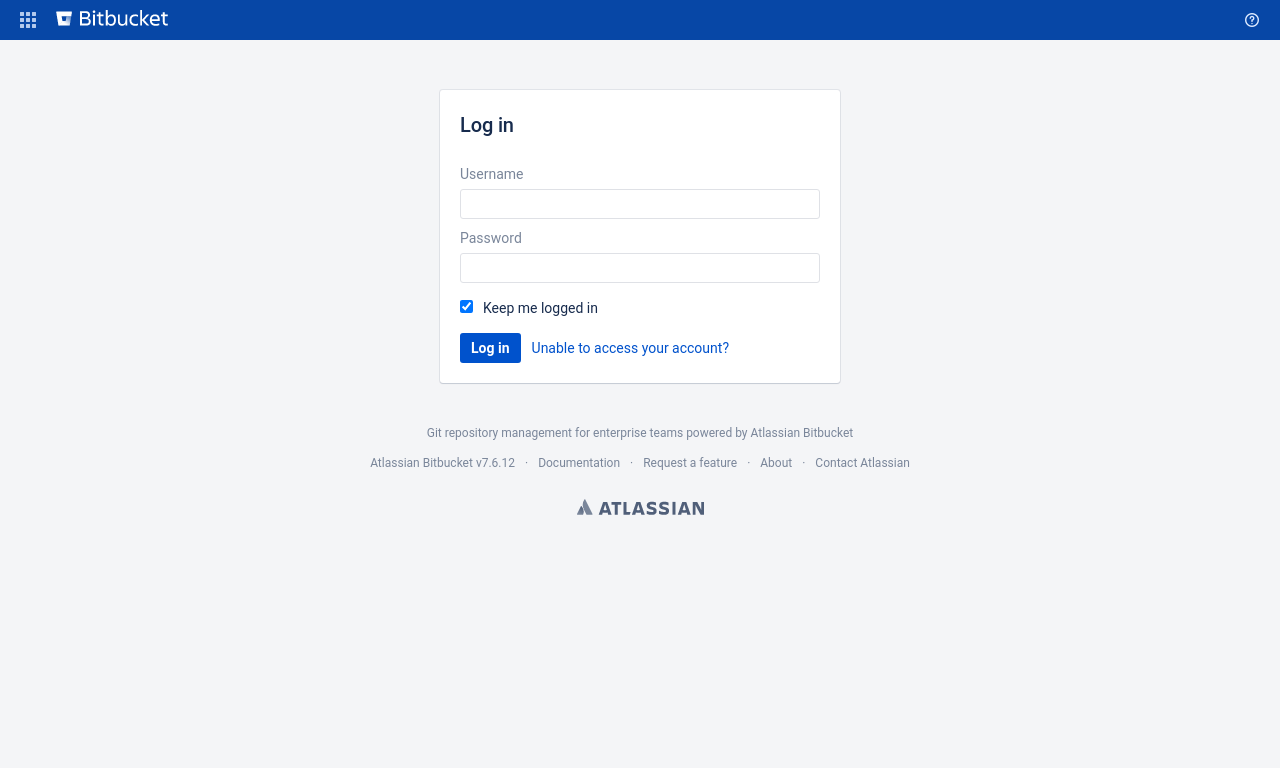
Atlassian Bitbucket Server
Favicon, HTML title and HTTP cookie fingerprints for the Atlassian Bitbucket server were added shortly after our Emergent Threat Response for CVE-2022-36804 was published on September 20th, 2022 in response to the command injection vulnerability in multiple API endpoints of both Bitbucket Server and Data Center. An adversary with access to either a public repository or read permissions on a private repository can perform remote code execution simply through a malicious HTTP request. Shelby Pace contributed the Metasploit Bitbucket Git Command Injection exploit module which is capable of exploiting the unauthenticated command injection. Bitbucket Server and Data Center versions 7.6 prior to 7.6.17, 7.17 prior to 7.17.10, 7.21 prior to 7.21.4, 8.0 prior to 8.0.3, 8.1 prior to 8.1.3, 8.2 prior to 8.2.2 and 8.3 prior to 8.3.1 are vulnerable. From a quick analysis of internet scan data there appears to be just under a thousand of these exposed on the internet.
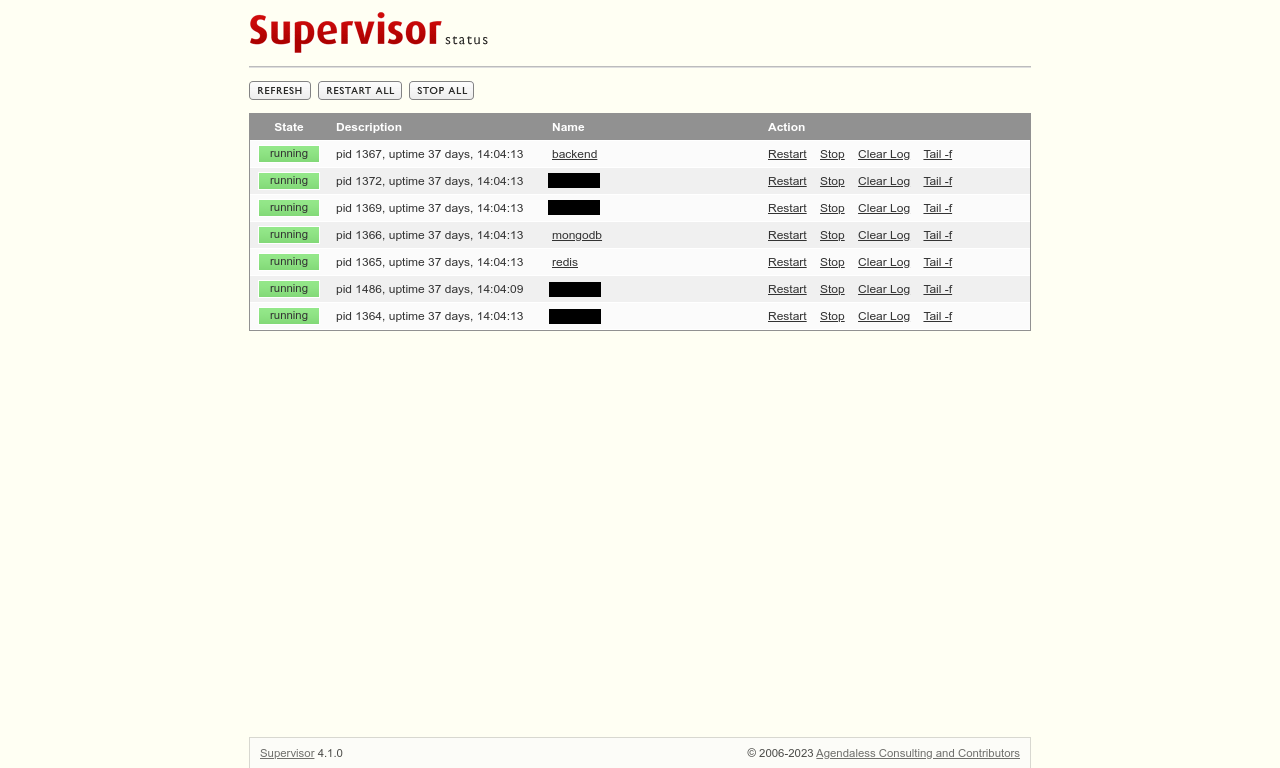
Supervisord Supervisor
Favicon and HTML title fingerprints were added for anyone interested in locating unsupervised Supervisor instances on their networks. The web interface for the process control system allows users to restart or stop processes under the software’s control, and even tail the standard output and error streams. There might be some interesting information in those streams! From a quick analysis of internet scan data there appears to be only about 165 instances on the internet.
New fingerprints (23)
- Add Python BaseHTTP fingerprint by @mkienow-r7 in #473
- More DHCP-based fingerprints by @dmoinescu-r7 in #476
- Add Talend Restlet Framework fingerprint by @mkienow-r7 in #475
- Add Gunicorn with no version fingerprint by @mkienow-r7 in #477
- Add Python WSGIServer fingerprint by @mkienow-r7 in #479
- Add OpenKM Document Management System fingerprint by @mkienow-r7 in #480
- Add Atlassian Bitbucket fingerprints by @mkienow-r7 in #482
- Add Mayan EDMS document management system fingerprint by @mkienow-r7 in #481
- Add SalesAgility SuiteCRM fingerprints by @mkienow-r7 in #483
- Add ManageEngine PAM360 fingerprints by @mkienow-r7 in #484
- Add ManageEngine Password Manager Pro fingerprints by @mkienow-r7 in #485
- Add ManageEngine Access Manager Plus fingerprints by @mkienow-r7 in #486
- Add Crow C++ framework for web services fingerprint by @mkienow-r7 in #487
- New dhcp vendor class fingerprints by @modoyle-r7 in #488
- Add Papermerge document management system fingerprints by @mkienow-r7 in #489
- Add Medusa extensible Internet server framework fingerprints by @mkienow-r7 in #490
- DHCP vendor_class Xerox Printer updates by @modoyle-r7 in #491
- Add Amazon OpenSearch fingerprints by @mkienow-r7 in #492
- Add Supervisord Supervisor web interface fingerprints by @mkienow-r7 in #494
- Add qdPM fingerprints by @mkienow-r7 in #495
- More fingerprints for the Polycom VVX family by @dmoinescu-r7 in #497
- DHCP fingerprints for Polycom SoundStation IP by @dmoinescu-r7 in #496
- DHCP fingerprint for Avaya device by @dmoinescu-r7 in #499
Bugs fixed (3)
- Temporary fix to restore rspec progress formatter by @mkienow-r7 in #474
- Restore non-capturing groups to fix anchored regex issue by @mkienow-r7 in #478
- Add missing IMAP CAPABILITY string by @mkienow-r7 in #498
Get the release
You can get the v3.0.3 Recog Ruby gem from RubyGems, the v3.0.3 Recog content archive from the Recog v3.0.3 release page, and you can get more details on the changes since the last release from GitHub:
Article Tags
Related blog posts

Artificial Intelligence
AI is Changing Vulnerability Discovery and your Software Supply Chain Strategy has to Change with it
Wade Woolwine

Detection and Response
Velociraptor 0.7.2 Release: Digging Deeper than Ever with EWF Support, Dynamic DNS and More
Rapid7

Detection and Response
Velociraptor 0.7.1 Release
Rapid7
Products and Tools
Velociraptor 0.7.0 Release: Dig Deeper With Enhanced Client Search, Server Improvements and Expanded VQL Library
Dr. Mike Cohen
