Unix, Evolved
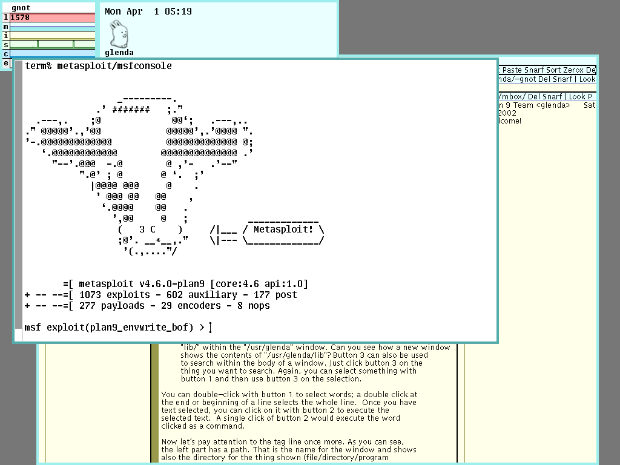
Today, we are delighted to announce the next phase of Metaploit's expanded support for more diverse host operating systems. On the heels of our integration work with Kali Linux, we've been heads-down on putting the finishing touches on our support for the future of Unix, Plan 9 from Bell Labs.
This renewed commitment to Plan 9 will come as a welcome relief for those of you who have, until now, been stuck on hobby operating systems such as Linux and FreeBSD -- academics and other researchers agree that Plan 9's rethinking of the file system mount points and distributed hardware models is ideal for today's networking environment. As we continue to blur the distinctions between the "extranet" and the "cloud," an operating system designed for distributed software and hardware is the most sensible choice for penetrations testers, exploit developers, and IT operations.
If you've been living under a rock for the last several years and have somehow avoided using Plan 9 so far, feel free to check the reference VMWare appliance. I'm sure you'll find the interface both intuitive and powerful. How could you not love an operating system that lets you mount a remote Ethernet interface as a local file system entity? Who needs clicking on hyperlinks when you can just mount the web site and use ls, grep, and find to navigate? Plan 9's utility as a pen-testing platform is apparent to anyone who's been brave enough to make the switch.
For those of you who have already made the switch, please feel free to comment below on your experiences with using Metasploit on this most excellent platform for security professionals. Readers are also encouraged to post here screenshots of Metasploit running on their own preferred operating system, be it a P9 derivative like 9Front or Inferno, or some other comparable OS such as NeXTSTEP, BeOS, SCO Open Desktop, or really any other device you're likely to use on an engagement.
