If you're conducting security assessments on enterprise networks, chances are that you've run into SAP systems. In this blog post, I'd like to give you an introduction to SAP and ABAP to help you with your security audit.
The full SAP solution (ERP or SAP Business Suite) consists of several components. However, to manage the different areas of a large enterprise, probably one of the better known components or features of the SAP solution is the development system based on ABAP, the language used to build business applications on the SAP platform.
The traditional way to execute ABAP code is to use a transaction, for example, from any existing SAP client (which will be reviewed later):
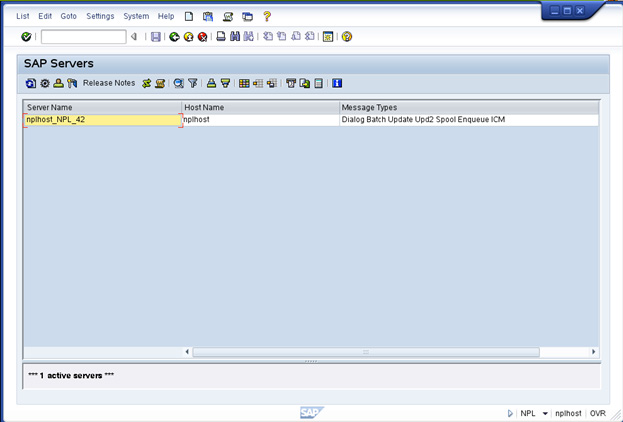
One way to simplify the concept of the SAP platform is to think of it as an application server. Most readers are probably familiar with Java-related application servers, so it's easy to think of SAP as an ABAP application server. In fact, SAP is capable of running ABAP applications as well as applications written in Java. The name of SAP's application server is SAP NetWeaver...
If you'd like to know more about this platform and how to pentest it with Metasploit, get your free research paper now "SAP Penetration Testing Using Metasploit - How to Protect Sensitive ERP Data."
If you'd like to join a live discussion on the topic, we're also hosting a tweet chat tomorrow, December 3, at noon ET under the hashtag #pwnSAP. Or you can register for our webcast on Thursday, December 6 at 2:00pm ET, "Become an SAP Pwn Star: Using Metasploit for ERP Security Assessments."
Article Tags
Related blog posts

Vulnerabilities and Exploits
CVE-2026-0826: How an Old Bug Can Feed AI-Powered Impersonation
Douglas McKee, Director, Vulnerability Intelligence

Vulnerabilities and Exploits
CVE-2026-0826: Critical unauthenticated stack buffer overflow in HP Poly VVX and Trio VoIP Phones (FIXED)
Stephen Fewer

Vulnerabilities and Exploits
Authenticated RCE via Argument Injection in Gogs (NOT FIXED)
Jonah Burgess

Threat Research
Q1 2026 Threat Landscape Report: Zero-clicks, geopolitical tensions, and some wins for law enforcement
Rapid7 Labs