By guest blogger Shane Rudy, Information Security Manager, AOScloud, C|EH | E|CSA | L|PT | CPT | CEPT
A few weeks ago I was excited when Rapid7, asked me to participate in their 2014 Tech Preview Program for Metasploit Pro version 4.9 I have always enjoyed the interaction I have had with the talented crew over at Rapid7 and I have been a big fan of Metasploit Framework since its inception years ago.
Rapid7 has done an excellent job of interacting and allowing its users to participate within their community and they are a humble group of cool, fun people. This was only made more apparent during this year's tech review program for the release of Metasploit Pro 4.9. The team was all about our feedback. Good or bad they wanted to hear it and they were open and honest and listened.
Metasploit Pro 4.9 has some great new features that we were all briefed on when the preview got under way and you can read more about them on your own time as you explore the product. For the purpose of this post I'll talk about what I was the most excited about testing: Dynamic Payload Generation to avoid possible detection from anti-virus solutions.
As a penetration tester and especially for those who are starting out, bypassing AV is essential to a successful compromise of an organization. You do not want to experience a moment where you find a box you have a pretty good chance of owning and blowing the process by having your payload discovered by the organization's defenses or having your payload detected during phishing or social engineering campaigns. You also don't want a company to get a false sense of security because they detected and stopped your attacks. Years ago I was on a rather large penetration test for a company who trusted their AV a little too much. So much so that they would blow off patching their systems to a degree. So exploitation was pretty easy, however all my payloads got detected and I was reminded by their admin just how awesome their AV was. So what did I do? I researched their version of AV, its detection mechanisms and developed a payload to bypass their defenses. They were not happy about it when I showed them, but at least they knew they were not immune, that they needed to patch their systems and deploy additional countermeasures. Unfortunately the downside was that developing this took time away from the initial testing.
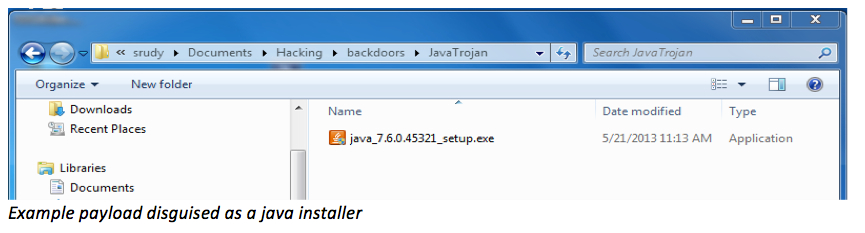
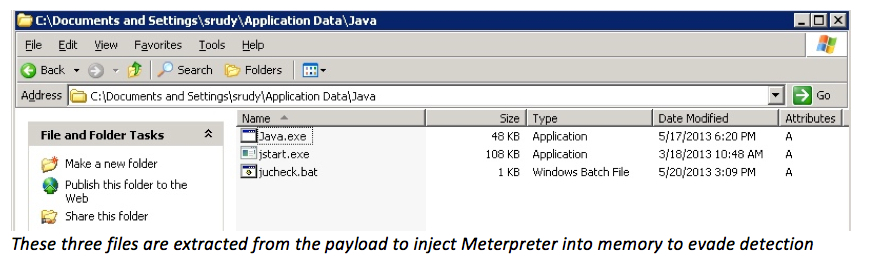
To avoid AV in the past I read many articles, tried many methods only to discover that most of the AV vendors had already caught up with these methods. I did have success re-coding and recompiling the source code of tools that typically would be detected such as injector programs and then using them in my payloads that I would drop onto a box (shown below) to get a Meterpreter shell and go unnoticed. It's not pretty, I know, but it was quick and successful most of time. Since most AV solutions use signatures and heuristics to identify malware and have issues with in-memory detection my success rate was pretty good, but in certain situations it became inconvenient.
To aid in helping users of Metasploit Pro bypass AV, Dynamic Payload Generation has gotten an overhaul in the recent version 4.9 release. Rapid7 tells us with Dynamic Payloads, you'll have these advantages:
• Evade all leading anti-virus vendors: Dynamic Payloads evade the top 10 AV solutions in more than 90% of cases. No AV vendor detects all MSP payload options!
• More stable sessions: Dynamic Payloads use error corrections to make sessions more stable than regular MSF sessions
• IPS Evasion through stage encoding: Stager will encode the traffic when downloading the payload, which can help evade IPS
In version 4.9 Dynamic Payload Generation has been incorporated into the user interface as shown:
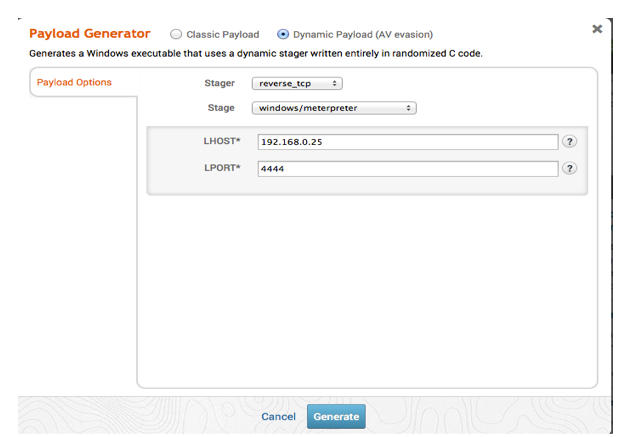
Just Select the Dynamic Payload (AV evasion) radio dialog, choose your stager and stage, fill in the local host (LHOST) and local port (LPORT) click Generate and you'll be off and running.
For die-hard console guys like myself, dynamic stager generation has been incorporated into exploit modules that have EXE based payloads. For example if you look at the following exploit:
exploit/windows/fileformat/ms12_005 you will see a new DynamicStager option as shown:
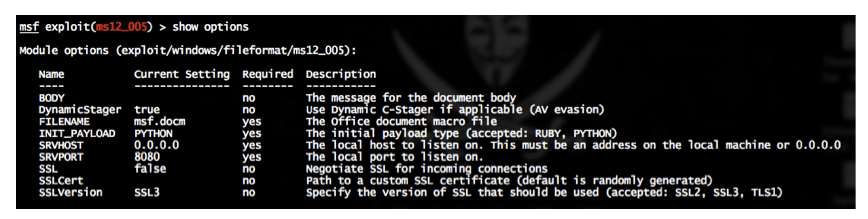
Notice the description: Use Dynamic C-Stager if applicable (AV evasion). These stagers are available automatically in the pro console in any exploit that uses EXE payloads. I will mention that the old standalone /exploit/pro/windows/dynamic_exe that was available in past msfpro consoles has been removed. The Metasploit team is aware of this and will be looking to bring this back in the next update. It will be replaced with auxiliary/pro/generate_dynamic_stager. I just thought I would mention that for those of you who have used this feature in the past.
In my testing during the tech preview all Dynamic Payloads that I generated from Metasploit were not detected when ran against several major ant-virus vendors. I did briefly test the new feature against IPS and was able to slip through the cracks. My sessions never crashed during the testing.
My conclusion at this point is that Metasploit Pro is a pretty excellent product that can save you time trying to evade defenses and improve your success rate of conducting successful testing. The team of developers and product managers are a great group of people who desire to hear the feedback of their users. My experience with the team has always been that if you have a fix or a good idea that will improve or enhance Metasploit Framework they want to hear it.
I hope you found this blog post informative and stay tuned for more from me in the future. Until then Happy Hackin…