As UserInsight grows and we look to add value to more incident response teams that have already chosen the solution that serves as their "single pane of glass", this series will update you on the integrations we build to share valuable context with those solutions.
The Solution
The Integration
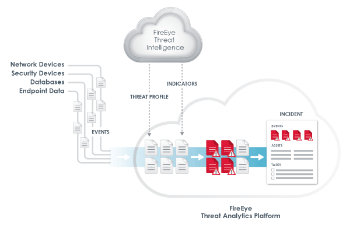
The first version of the integration was released at the beginning of August to rave reviews and a great deal of tweets during Black Hat USA. In this integration, you can configure a Data Exporter on the UserInsight collector to send IP-to-user mapping to TAP. If your immediate response is "that's all?", I will forgive you, but the fact is this context is the very basis necessary to add user context to investigations. If you are sick of receiving alerts from various security solutions that tell you that "10.1.1.72 just violated policy 'never blindly open EXEs'" or "10.2.5.15 just uploaded the source code repository to www.command-and-control.su" and having to scramble to figure out who was on the IP address and whether there could be a legitimate reason, you will be be pleased to know that with UserInsight, your FireEye TAP alerts will include the user.
Related blog posts

Vulnerabilities and Exploits
ClickFix Phishing Campaign Masquerading as a Claude Installer
Nicholas Spagnola

Vulnerabilities and Exploits
FortiGate CVE-2025-59718 Exploitation: Incident Response Findings
Eric Carey, Olivia Henderson +1
Products and Tools
Identifying and Mitigating Potential Velociraptor Abuse
Christiaan Beek

Detection and Response
Rapid7 Q2 2025 Incident Response Findings
Chris Boyd