Don't Create Blind Spots
As a consultant for a security company like Rapid7, I get to see many of the processes and procedures being used in Vulnerability Management programs across many types of companies. I must admit, in the last few years there have been great strides in program maturity across the industry, but there is always room for improvement. Today I am here to help you with one of these improvements – avoiding asset risk blind spots.
One of the more common “broken” processes that I still come across relates to the methods and procedures for managing those assets which are too easily ignored… Excluded Assets. These assets are the “black sheep” of vulnerability and risk management, due to the inability to assess risk on assets you cannot “see.” There are valid reasons to create asset exclusions, but this must be managed with appropriate process and procedure to avoid creating inadvertent blind spots during your vulnerability assessment.
Creating Asset Exclusions
Nexpose provides two options for excluding assets from vulnerability scans. This capability is critical in a mature vulnerability scanning tool due to the requirements of operational and risk management teams. These asset exclusion options are permanent configurations that allow for persistent asset exclusion. The permanence of these options are where vulnerability management program processes seem to break down due to the lack of cyclical management and review procedures.
Let's begin by reviewing these asset exclusion configuration options:
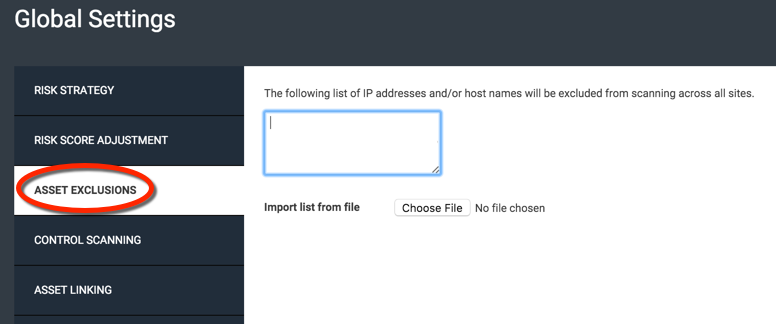
- Global Asset Exclusion: Administration -> Global -> Manage -> Asset Exclusions (Permanent)
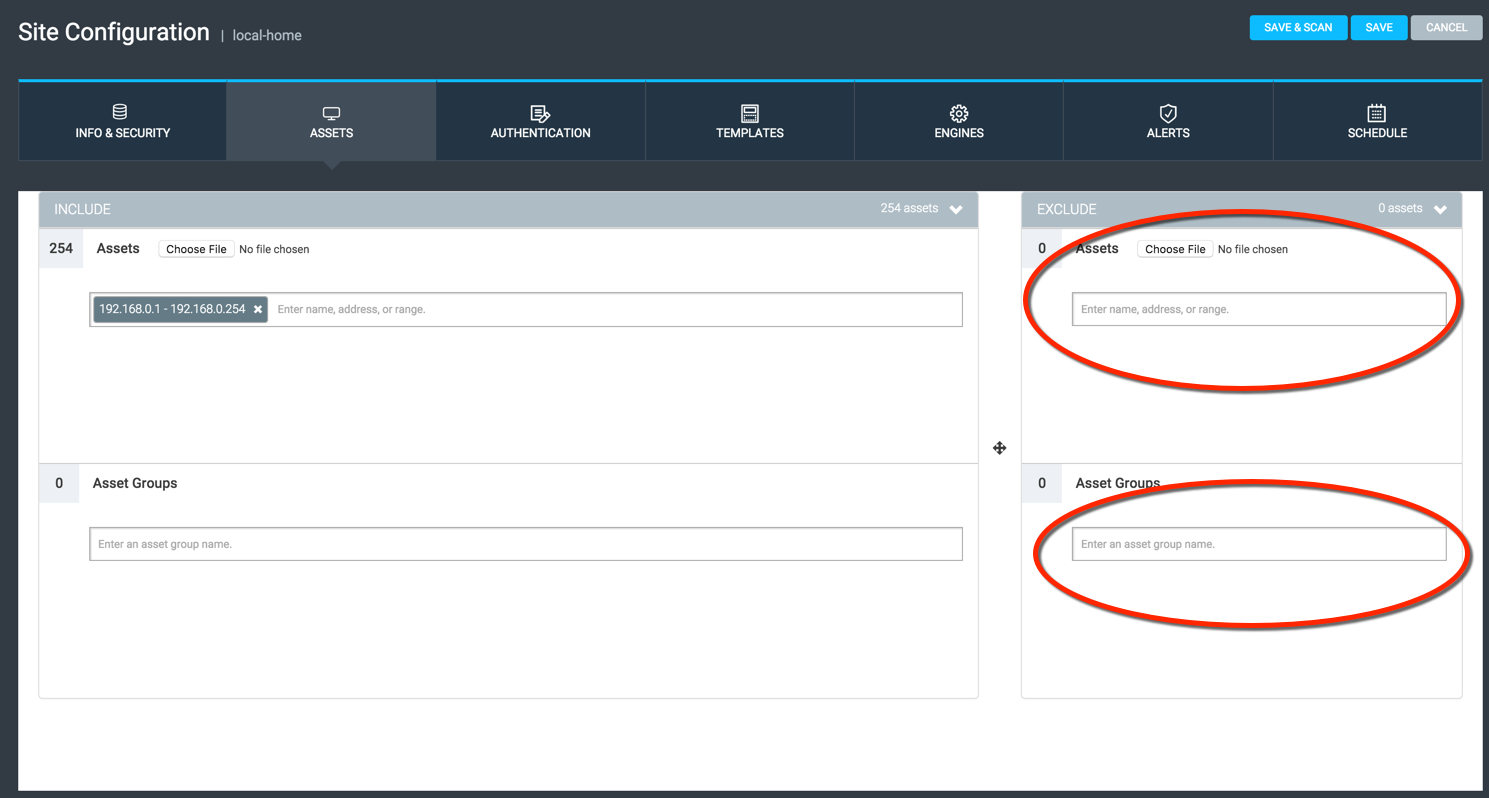
- Site Asset Exclusion: Site -> Assets -> Exclude (Permanent)
One of the primary reasons that operations teams, system owners, and risk management teams request Nexpose administrators to add certain assets to these exclusions is to address perceived or real availability impacts. During my career in vulnerability management, there have been times during the lifecycle of vulnerability scanning tools in which specific vulnerability tests can cause adverse impacts to certain assets with specific identified vulnerabilities. These asset exclusion options provide a way to avoid these specific impacts.
Managing Asset Exclusions
The break in the process is that once an asset (IP address) is placed into these exclusion lists, they are usually not revisited… ever. No, really. Set it, and forget it. Vulnerability management is not like cooking a rotisserie chicken, you can't just set it and forget it. Mature vulnerability management programs involve cyclical processes which involve assessment, reporting, remediation/mitigation, and verification (reassessment). I know the question you have now is…
“How can we apply that same cyclical process to manage asset exclusions?”
Winner, Winner, Chicken Dinner!
Following this 4 step cyclical process can help remove this blind spot in your vulnerability management program caused by unmanaged asset exclusions:
- Assessment – Identify the asset to be excluded and assess the risk of removing the asset from vulnerability scanning. Ensure that the risk assessment documentation includes the data which resides on the asset, controls that are in place to protect the asset, and the reason that the exclusion request was created.
- Reporting – Run periodic reports of all assets which are currently excluded from vulnerability scans, both global and site level exclusions. Ensure that the reason for the exclusion and date the asset was added for exclusion is tracked (excel, database, etc).
- Remediation/Mitigation – Identify if the reason given to exclude an asset is something related to specific vulnerability tests in the vulnerability scans. Look into creating a scan template which excludes the specific vulnerability test, and remove the asset from exclusion. You may find that there are “classes” of assets which are impacted by the same (or related) vulnerability tests and these can be managed with a reasonable number of ‘custom' scan templates.
- Verification (Monthly, Quarterly, Annually) – Does this asset still need to be excluded from vulnerability management scans? Apply the same risk assessment provided in step
• Repeat Step 1
Put It into Practice
Can it get any easier? These simple 4 steps can add a critical process to address the possible “blind spots” that unmanaged asset exclusions can add to your enterprise. Ensuring that your vulnerability management program has a cyclical process to address vulnerability scanning asset exclusions will increase the accuracy of your risk management reporting for your company and reduce the overall risk exposure of unknown vulnerabilities.
Example SQL Query:
SELECT ds.name AS site, dst.target AS excluded
FROM dim_site_target as dst
JOIN dim_site ds USING (site_id)
WHERE included = false
ORDER BY ds.name, dst.target;
Output:
| site | excluded |
|---|---|
| Affiliate: Network 1 | 1. 10.0.0.1-10.0.0.254 |
| Company: CIS Benchmarks | 1. 10.0.0.1-10.0.0.25 |
Want to help improve Asset Exclusion management in Nexpose?
Rapid7 offers a way for customers and clients to provide feedback on product “IDEAS” through our IDEA Portal on our Support site. It is an interactive process involving posting an idea, promoting it through “up voting”, and then finally having it included into the product through a release.
Related blog posts

Vulnerabilities and Exploits
CVE-2025-20333, CVE-2025-20362, CVE-2025-20363 - Multiple critical vulnerabilities affecting Cisco products
Ryan Emmons

Vulnerabilities and Exploits
CVE-2025-10035 - Critical unauthenticated RCE in GoAnywhere MFT
Stephen Fewer

Vulnerabilities and Exploits
CVE-2025-7775: Critical NetScaler vulnerability exploited in-the-wild
Stephen Fewer

Vulnerabilities and Exploits
CVE-2025-6543: Zero Day Exploitation of NetScaler ADC and NetScaler Gateway
Stephen Fewer