What’s the Wi-Fi KRACK vulnerability all about?
Fundamental weaknesses in the most common Wi-Fi security protocols in use today—Wireless Protected Access versions I and II (WPA1 and WPA2)—have been discovered by cybersecurity researchers at KU Leuven. You know it’s a real, modern vulnerability because it has a website and logo, too: https://www.krackattacks.com/. Their website has a detailed explanation along with a video showing proof that the vulnerability exists and how it can be exploited.
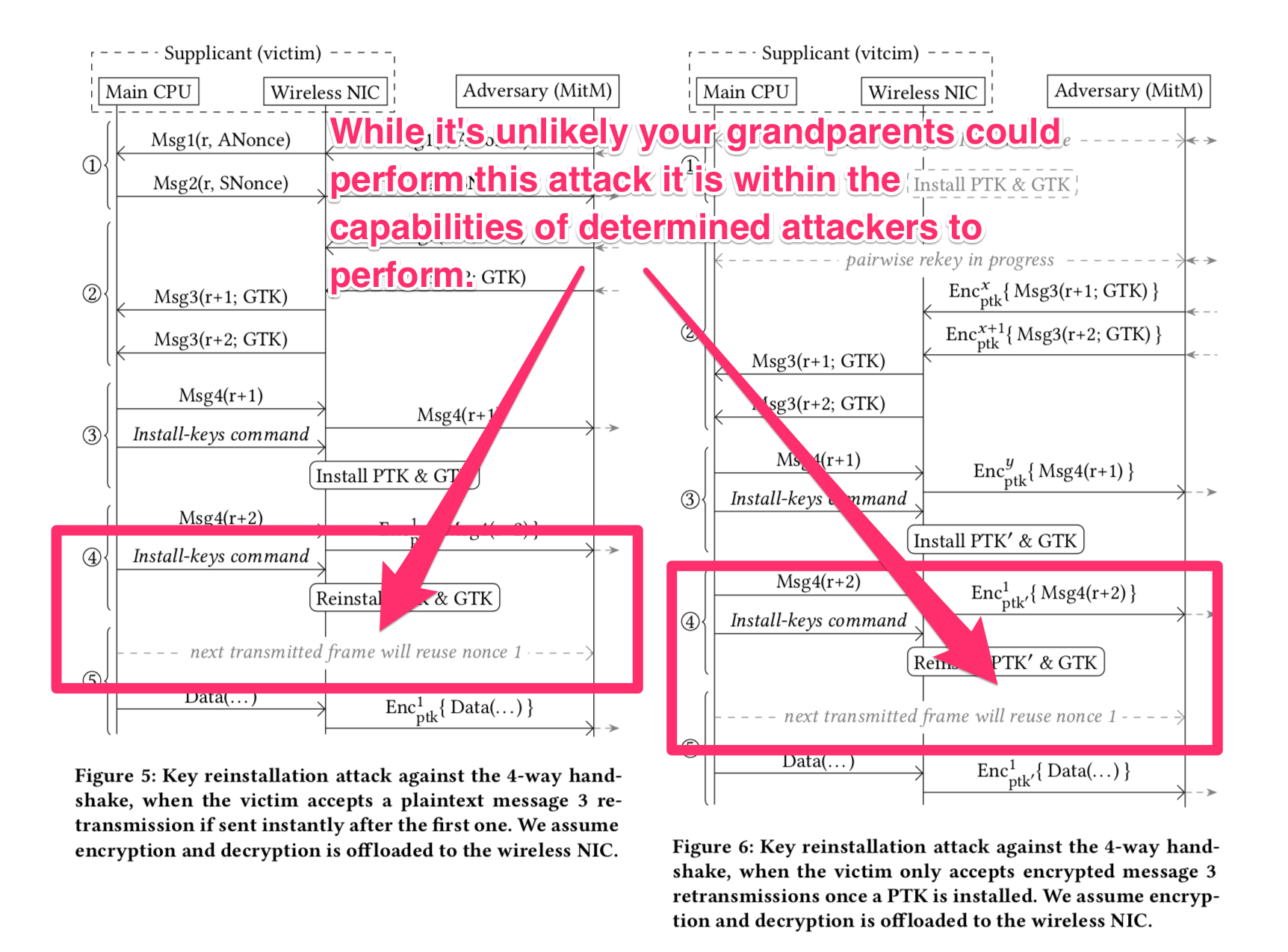
By repeatedly sending one component—message 3—out of a sequence of 4 messages used to set up encryption keys in a WPA connection handshake, attackers can gather enough data from Wi-Fi connections to potentially break the encryption (i.e., impact confidentiality) of what are supposed to be secure network transmissions between Wi-Fi clients (phones, laptops, etc.) and Wi-Fi access points/routers. For the most vulnerable devices (some Linux and all Android 6.0 and higher devices), attackers can also inject/modify the contents of network packets (i.e., impact integrity).
Hence the name KRACK: Key Reinstallation Attack*s. When two or more data streams are encrypted with the same key, it’s much, much, much easier to decrypt the contents of the streams.
Who is vulnerable to the KRACK vulnerability?
Everyone using Wi-Fi is vulnerable (until this vulnerability is patched).
No, seriously. Who is vulnerable?
Seriously: everyone using Wi-Fi is vulnerable. This weakness impacts Wi-Fi routers/access points as well as endpoint devices that run Android, iOS, macOS, Windows, Linux (computers, IoT devices, etc.), and more.
This is a fundamental protocol-level weakness that impacts both WPA1 and WPA2 protocols (those used to secure both home and enterprise Wi-Fi networks). Attackers only need to be within signal range of your Wi-Fi networks to launch the KRACK attack, and no authentication is required. Those with malicious intent just need to mess with the Wi-Fi connection setup in one place (see figure below) to cause encryption key-reuse.
The “sky is absolutely not falling” and there are no indications that this vulnerability is being exploited at this time, but it just became easier for attackers in proximity to your network to break information confidentiality and integrity.
What should I do?
Organizations and home users should actively check for patches for their phones (especially Android), tablets, computers, IoT devices, and Wi-Fi access points and patch them immediately after a fix has been issued by vendors. This is not as easy as it sounds. Home users and small business users who rely on equipment provided by their internet service providers (ISPs) should contact said providers to find out when/if the KRACK vulnerability is being patched. If your Wi-Fi router vendor or ISP has no plans to patch this vulnerability, you should buy a new device that is patched.
If possible, configure WPA2 equipment to use and enforce the AES-CCMP (AES-Counter Mode CBC-MAC) protocol, as it makes it much more difficult for eavesdroppers to eavesdrop (in general, though it does not thwart this attack) and helps ensure integrity of all communication by preventing tampering.
Anyone who has installed their own Wi-Fi equipment should be checking their equipment provider’s web site for patches and installing them as soon as they are available.
CERT/CC has posted a list of vendors (with vulnerability and patch status).
What else should I do?
There are ways to protect yourself or your organization’s network even without patching.
All users should use a VPN service when connected via public Wi-Fi or fully ensure they only connect to websites over HTTPS. The VPN route is most reliable as everything is encrypted that way. This site lets you compare VPN options: https://www.safetydetectives.com/best-vpns/ to pick the one that is right for you.
Your devices’ operating systems and the software/apps that run on them make many network connections without HTTPS. Also you can’t even ensure a website with HTTPS transfers all website components over HTTPS or has configured their HTTPS servers to be protected against HTTPS attacks. You can use browser extensions such as HTTPS Everywhere to help ensure you’re working over HTTPS whenever possible via a supported web browser.
Organizations should consider re-architecting their Wi-Fi networks to treat them as “untrusted zones” that only route device traffic out to the Internet and always require a VPN to access resources in the main organizational network. It’s also a good, modern practice to have this be the case for all networks—even wired ones—where user devices connect.
It cannot be stressed enough that home users (especially those in densely populated areas) absolutely must monitor for patches for their existing Wi-Fi equipment and devices/operating systems or migrate to new devices that don’t have this vulnerability.
If you are really worried about eavesdropping or loss of data integrity, consider disabling Wi-Fi on your mobile devices and use your 3G or LTE connections until this vulnerability is patched. Also consider using wired connections at home or work until this vulnerability is patched.
Can this attack be detected?
It may be possible to detect this attack if you are an organization that has Wi-Fi equipment capable of verbose logging and are monitoring for this attack. It is a very noisy, active attack and should be detectable by the vast majority of enterprise cybersecurity monitoring systems if they are configured to watch for it.
There are a few Wi-Fi vendors who provide intrusion prevention systems built-into the Wi-Fi access point devices that will also detect and block man-in-the-middle attacks as well as detect vulnerable devices and prevent them from joining the network.
More to come
Rapid7 product teams are releasing detections for vulnerable systems and Rapid7 researchers are keeping an eye on the vendor patch status, so check back for more information.
Update 10/23/17
Time has passed and there are some new events and resources that may help folks stay on top of the Wi-Fi KRACK vulnerability. So far, Rapid7 researchers and incident responders have not seen any sign of active attacks exploiting the KRACK vulnerabilities in the wild.
First up is a great "patch tracker" setup on GitHub by Kristopher Tate. The community is contributing to keeping a much more detailed tracker up-to-date with a very handy vendor response table that lists patch/mitigation dates and resoures. One especially useful aspect of the site is the detailed tracking on Android operating system versions/flavors with notes from various device manufacturers on when they plan on having patch releases out.
As of this update, 54 out of 111 tracked vendors have "No Known Official Response", meaning that only 52% of tracked vendors have patches available or plans to have a patch available at some point in the future.
It's important to note that many vendors have plans to release patches in Q1 or Q2 of 2018, so it is vital that you make sure you know when your devices will be patched and consider switching devices/vendors if the patch delay does not track with your risk appetite.
Second is news from Google that an Android patch will be forthcoming on November 6th (2017) and reports from Apple that their iOS, tvOS, watchOS and macOS beta channels are currently testing a patch that will be released "soon". It is not known if Apple will be releasing patches for older versions of their operating systems or just keeping curret revisions patched.
Penultimately, there's a spiffy script by Mathy Vanhoef (one of the KRACK vulnerabilty paper authors) that can help test wireless access points to see if they are susceptible to the KRACK vulnerability.
Finally, it's worth re-emphasizing that there are many devices in the "Internet of Things" (IoT) category which you need to patch. Not just at home, either. Many building HVAC systems and other "industrial" IoT environments rely on 802.11 wireless networks for data upload and command-and-control. One area we've not seen mentioned much is that of Wi-Fi in automobiles. Many modern cars are Wi-Fi clients and even more are now Wi-Fi access point "hubs". In fact, there were 97 automobile models with Wi-Fi options and 123 in 2017.
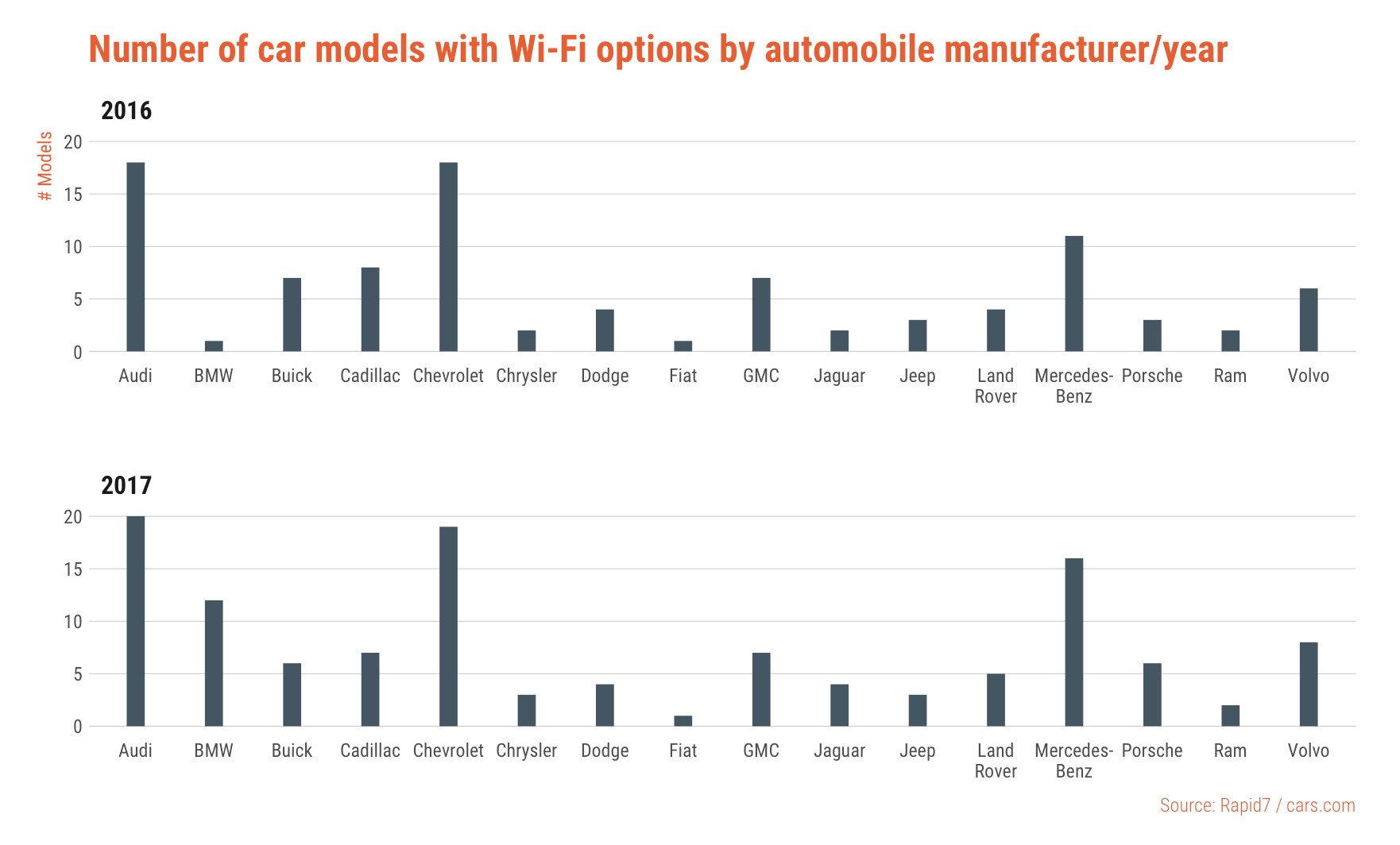
To-date, there has not been any word from automobile manufacturers how, when or if they will be addressing the KRACK issue in their vehicles. Along with IoT devices, these may be the last components to see an update, but many of them have direct access to calendar, contacts, mail and more. Individuals or fleet managers with Wi-Fi-enabled vehicles should check with their service contacts to see when they may be receiving an update.
As usual, Rapid7 researchers will continue monitoring and investigating and provide updates when warranted.
Banner image (used CC-BY-SA) by Peter Clarkson
Article Tags
Related blog posts

Exposure Management
Patch Tuesday - May 2026
Adam Barnett

Artificial Intelligence
Project Glasswing and the Next Challenge for Defenders: Turning Faster Discovery into Faster Action
Craig Adams

Exposure Management
Patch Tuesday - April 2026
Adam Barnett

Products and Tools
Negotiating with the Board: Translating Active Risk into Financial Exposure
Trevor Christiansen
