On Wednesday, March 28, NBC reported Grindr security flaws expose users' location data, a story which ticks a couple hot-button topics for security professionals and security reporters alike. It’s centered around the salacious topic of online dating in the LGBT community, and hits a personal safety concern for people using the app everywhere, not to mention the possibility of outing LGBT people in regions where being gay, bisexual, or trans is illegal or dangerous.
Unfortunately, this story is guilty of some of the worst kind of FUD — fear, uncertainty, and doubt — that still happens when some journalists cover our industry. I am here to tell you, dear Grindr user, there is nothing going on at Grindr that is unreasonably exposing your location data. In this case, the angel is in the details.
What’s Not A Vuln
Ultimately, when you read the the NBC story, you can see where this reporting shifts from news to FUD:
His website allowed users to see who blocked them on Grindr after they entered their Grindr username and password. Once they did so…
I’m going to just stop you right there, since this is a pretty big red flag about this described vulnerability. “After they entered their Grindr username and password,” means, “After the user voluntarily compromised themselves.” Any vulnerability that exposes user data that depends entirely on already having the best bit of user data available — the password — isn’t a vulnerability.
Of course, I had to be missing something. Maybe there was some privilege escalation trick in play that let the attacker, armed with any username and password, see other people’s data, or all the data, or something like that. Also, the location data bit seemed off, too — I was pretty sure Grindr used normal SSL and normal API calls for location services, so I wasn’t sure what the location exposure was about. Did that also depend on already having the user’s password?
Phishing for LOLs
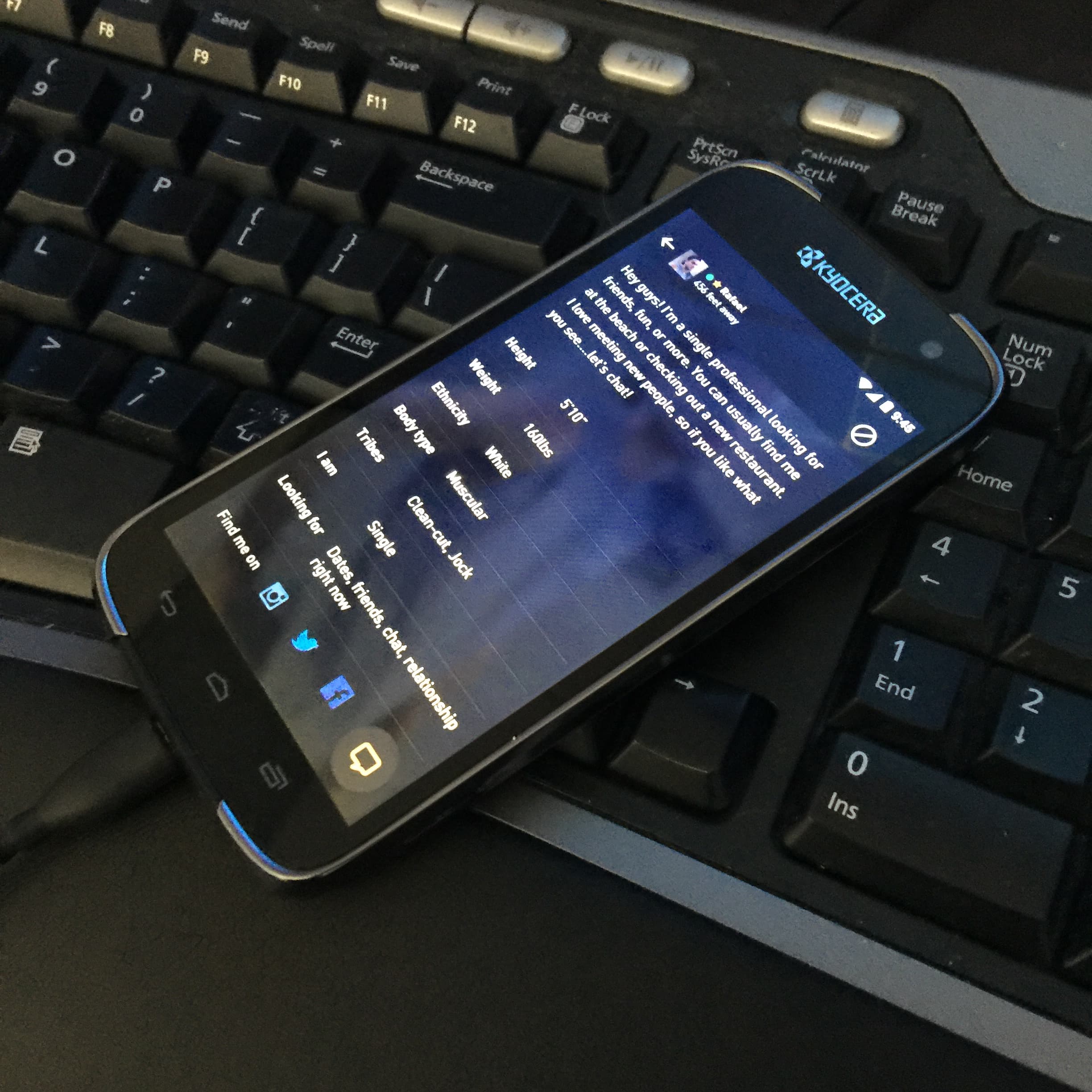
To get to the bottom of this, I got on the phone with Trever Faden the next day to ask for his write up, since I didn’t see that linked in any of the stories. Turns out, he didn’t do any formal research. Trever is a nice guy and a smart web services developer, but he told me bluntly that he’s “not a security expert.” With that caveat, he then enthusiastically described what was actually going on with Grindr and his own service, C*ck Blocked (hereafter referred to as “CB”).
CB worked like this: You, a Grindr user, provide a username and password. CB turns around and authenticates to Grindr, as you, and makes a normal-looking API request for status, and that response includes an array of users who have blocked you. This array isn’t normally displayed in the Grindr UI, so that’s the service CB provides.
Now, you can make an argument that this is an information disclosure, kinda-sorta similar to the Yopify issue we disclosed almost a year ago. Sometimes APIs provide data that’s sensitive, and rely on client-side protections to keep that data private. However, the information on who blocked you isn’t really all that sensitive; it tends to be pretty obvious to the user when the suspected blocker suddenly disappears, and easy to verify just by creating a new account. So, this isn’t so much a security vulnerability, but more of a software misfeature.
No matter how you cut it, though, it does all depend on already learning the person’s username and password, and while Trever absolutely seems like a stand up guy, there’s no way to guarantee that he wasn’t secretly logging all 16,000 or so people’s account credentials. If you provided CB your password, you should change it right away.
Your Location Is (Mostly) Safe
The other issue identified is around the location services that Grindr requires for its match-making. While users can opt out of displaying their location, Grindr still collects it, and it’s still transmitted to Grindr HQ in California. Since California is a land of laws, your data could be recovered by people who have subpoena power. However, that’s not usually something we’d consider a software vulnerability.
The real issue identified by Trever is that while the Grindr app enforces SSL certificate pinning, Apple iOS does make it fairly easy to subvert the implementation by installing a new trusted certificate authority (CA). Now, we’re big fans of cert pinning, and our own Deral Heiland has talked at length about its virtues, and I'm pleasantly surprised that Grindr employs it, even though someone with operating system control could disable it.
This OS control requirement is another red flag. It’s a really long walk to get from “An attacker with physical access to the phone can MITM Grindr data as it leaves the phone” to NBC’s “passive observers of internet traffic [...] can identify the location of anyone who opens the app.” The observer, in this case, needs to perform a significant amount of work to get in that privileged position, and cannot perform this attack over the network — they must have trusted, physical access to the device in order to alter the stored, trusted certificates.
FUD Hurts
In the end, I think the thing that bugged me the most about this story on Grindr isn’t that the article gets some technical details wrong, or even that the reporter overstated the risk. I have a problem with the tone. Imagine Grindr users looking at this headline, skimming the details, then getting scared off of the service, never to return. Plenty of people in the LGBT community have personal circumstances where finding compatible people to date can range from problematic to dangerous. For all the snickering about Grindr (and similar apps) being merely useful for anonymous hook-ups, I’m sure plenty of people have found true happiness and human connections through Grindr, and demonizing the app, or others like it, is unnecessary and misses the point.
If there were real vulnerabilities and real risk posed to Grindr users, I would be first in line to tsk-tsk Grindr LLC, and complain, loudly, that they have a special responsibility to their users when it comes to personal privacy and physical safety. However, there’s really not much here. Sure, maybe they could educate their users better about sharing passwords, or employ a 2FA scheme for authentication. But in the end, Grindr hasn’t done anything wrong here, and their app is just as safe as the vast majority of dating and social apps.
Update (Monday, April 2, 2018): It appears that the Grindr app is, in fact, sharing some data over cleartext HTTP (as opposed to encrypted HTTPS) through its use of embedded ad networks and analytics service providers. This is according to research published on GitHub by SINTEF, a Norwegian research organization. In order to intercept this data (which includes GPS data), an attacker would still need to have a privileged position in the network, such as the victim’s WiFi router or an ISP router, but would not have to compromise the handset or install a bogus CA root certificate anywhere. Now that Grindr is aware of this issue, I expect them to update their app to ensure that any personally identifying information (PII) is transmitted using normally-encrypted channels. As promised above, I am admonishing Grindr about this implementation.
Article Tags
Related blog posts

Industry Trends
Navigating Choppy Waters: Top Security Predictions from Rapid7's 2025 Webinar
Rapid7
Industry Trends
Why Cybercriminals Are Not Necessarily Embracing AI
Christiaan Beek

Industry Trends
The Empty SOC Shop: Where Has All the Talent Gone?
Jake Godgart

Industry Trends
Navigating the Evolving Patchwork of Incident Reporting Requirements
Peter Woolverton