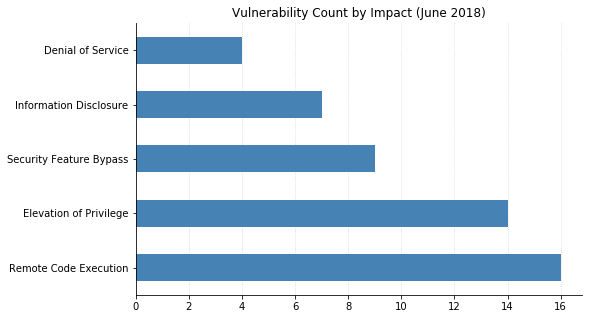
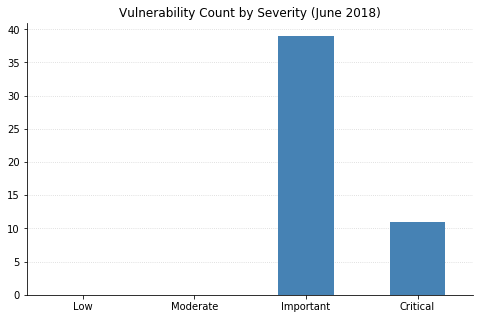
This month's Patch Tuesday is rather run-of-the-mill, with a total of 50 vulnerabilities being addressed by Microsoft. However, a bit of excitement came earlier this month, with an out-of-band patch for Adobe Flash Player released last Thursday to fix four security issues. Two of these were flaws that can lead to remote code execution (RCE), one of which (CVE-2018-5002) had been seen actively exploited in the wild. Attackers were using Office documents with embedded malicious Flash content in targeted email campaigns.
None of the Microsoft vulnerabilities patched today have been seen in the wild, although CVE-2018-8267 (an RCE vulnerability in Internet Explorer) had been publicly disclosed before today's release and is likely to be exploited soon if it hasn't already been.
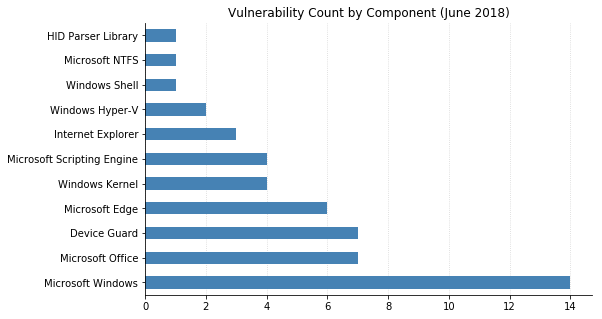
The majority of vulnerabilities this month are in Windows, which is a bit of a change from the usual bevy of browser-based bugs. Microsoft Office has a handful of vulnerabilities being addressed as well, including CVE-2018-8248 (an RCE in Excel). On the server side, two privilege escalation vulnerabilities in SharePoint Server and one in Office Web Apps Server have been fixed. There is also an HTTP Protocol Stack RCE, CVE-2018-8231, which affects Windows 10 and Server 2016 and could be exploited by an unauthenticated actor sending a maliciously crafted packet to a server running Http.sys.
It's also worth noting that seven separate Device Guard vulnerabilities which allowed code integrity policies to be bypassed have been patched. (Device Guard is a feature available in Windows 10 Enterprise and Server 2016 that blocks unauthorized code from being loaded.)
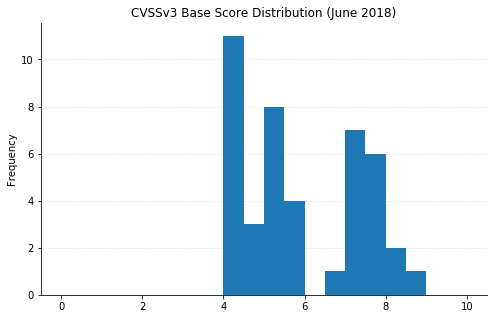
Note: not all CVEs had CVSSv3 data available at the time of writing