Our security team knows a thing or two about conquering a conference – making the most out of the day and night. So the team got together to share their personal recommendations on things to do and things to know in this handy Black Hat 2018 Survival Guide.
We’ve got you covered on all things Black Hat.
- Getting Around – Monorail, shuttle services, and hotels
- Where to Party – The full list of official and unofficial parties
- Recoup and Recover – There are a ton of spots to escape the chaos
- Top Sessions:
- Come Say Hi – Stop at our booth L17 for shwag and prizes
GETTING AROUND
Knowing where to go is half the battle. Knowing how to get there is a game changer. Here’s everything you need to know to get you there on time.
MANDALAY BAY MAP:
http://www.smartervegas.com/hotels/mandalay_bay/propertymap.aspx
WHERE TO STAY: Black Hat has discounted rooms of all shapes and sizes. If you haven’t booked your room yet, head on over to https://www.blackhat.com/us-18/travel.html#hotels for the best price and location.
VEGAS STRIP MONORAIL: If you didn’t book your hotel at Mandalay Bay, no worries. Vegas has a monorail that runs from SLS Las Vegas to MGM Grand, and another free monorail from the Mandalay Bay to Excalibur. The Vegas Monorail is one of the easiest ways to get around the strip, so if you’re here all week, you can buy your tickets ahead of time. Check out this reference map to better plan your day:
THE AIRPORT SHUTTLE SERVICE:
Need a ride from the Las Vegas airport to your hotel? Black Hat USA 2018 has partnered with LASxpress to offer one-way airport transfers for as low as $11.00 and round trip for $32. Book now to receive this special rate.
WHERE’S THE PARTY AT?
If you’ve had enough sessions, there are no shortage of things to do and we’ve got the ‘Unofficial List of Parties’ to keep you in the know.
https://www.blackhat.com/us-18/features/schedule/
PARTIES YOU CAN’T MISS:
- LIGHT UP THE NIGHT W/ BIZ MARKIE – DISTILL
Tuesday, August 7 | 8:00pm-12:00am – REGISTER - CHAMPAGNE TOAST
Wednesday, August 8 | 10:55am-11:15am – MORE INFO - QUEERCON HAPPY HOUR
Wednesday, August 8 | 4:00pm-6:00pm – MORE INFO - PWNIE AWARDS
Wednesday, August 8 | 6:30pm-7:30pm – MORE INFO - NAVY SEAL CISO HELICOPTER TOUR EVENT – TCELL + COBALT
Wednesday, August 8 | 6:00pm-10:00pm – REQUEST INVITE - CISCO TOP GOLF PARTY
Wednesday, August 8 | 8:00pm-11:00pm – REGISTER
RECOUP AND RECOVER
- CHILL SPACE
Saturday, August 4 | 10:00am-5:00pm | Palm Foyer, Level 3 - REVIVE LOUNGE
August 8 + 9 | 10:00am-5:00pm | South Pacific C, North Hall - YOGA
Wednesday, August 8 | 6:00pm-7:00pm | South Pacific C, North Hall
Thursday, August 9 | 1:15pm-2:15pm | South Pacific C, North Hall - DAYCARE – SIGN UP
Wednesday, August 8 08:00 – 18:00
Thursday, August 9: 08:30 – 18:30 - SMOOTHIE SOCIAL
Wednesday, August 8 | 3:30pm-3:50pm | Oceanside & Shoreline Ballrooms, Level 2 - MIMOSAS
Thursday, August 9 | 11:50am-12:10pm | Business Hall, Shoreline Ballroom, Level 2 - ICE CREAM SOCIAL
Thursday, August 9 | 3:20pm-4:00pm | Oceanside & Shoreline Ballrooms, Level 2
TOP SECURITY SESSIONS
GET HANDS ON SESSIONS
DefCon
DEF CON is a hacker convention which takes place immediately following Black Hat in Las Vegas every year.
Upon purchase of Black Hat Briefings and/or Trainings passes, each registrant will also have the option to purchase a single (1) advance ticket to DEF CON 2018, at a rate of $280 per ticket, one ticket purchase per person, up until the close of “Late” registration on August 3, 2018 at 23:59 PT.
- When: August 9-12, 2018
- Where: Caesar’s Palace & Flamingo, Las Vegas
- How much?: $280 USD cash only at the door.
Kaizen Capture the Flag Contest
Show off your cyber savvy in the Booz Allen Kaizen Capture the Flag! Our Internet-accessible CTF has challenges for all skill levels. Over $2,000 in prizes up for grabs! Register here!
- When is the CTF?
Start: 12:01 AM PDT on Wednesday, August 8th
End: 11:59 PM PDT on Thursday, August 9th - Where is the CTF? Register at https://blackhat.kaizen-ctf.com/register.
The CTF will be hosted online and can be completed remotely, we will have a few challenges available only to in-person attendees our booth (#1607). - What do I need? We recommend a laptop with a 64-bit Kali Linux virtual machine. Commercial reversing tools (e.g., IDA Pro, Binary Ninja) would be helpful on the binary reversing and exploitation challenges.
- What are the prizes?
1st place — $1,000
2nd place — $600
3rd place — $400
APPSEC AND NETWORK DEFENSE SESSIONS
Edge Side Include Injection: Abusing Caching Servers into SSRF and Transparent Session Hijacking
When caching servers and load balancers became an integral part of the Internet’s infrastructure, vendors introduced what is called “Edge Side Includes” (ESI), a technology allowing malleability in caching systems. This legacy technology, still implemented in nearly all popular HTTP surrogates (caching/load balancing services), is dangerous by design and brings a yet unexplored vector for web-based attacks.
The ESI language consists of a small set of instructions represented by XML tags, served by the backend application server, which are processed on the Edge servers (load balancers, reverse proxies). Due to the upstream-trusting nature of Edge servers, the ESI engine tasked to parse and execute these instructions are not able to distinguish between ESI instructions legitimately provided by the application server, and malicious instructions injected by a malicious party. Through our research, we explored the risks that may be encountered through ESI injection: We identified that ESI can be used to perform SSRF, bypass reflected XSS filters (Chrome), and silently extract cookies. Because this attack vector leverages flaws on Edge servers and not on the client-side, the ESI engine can be reliably exploited to steal all cookies, including those protected by the HttpOnly mitigation flag, allowing JavaScript-less session hijacking.
Identified affected vendors include Akamai, Varnish Cache, Squid Proxy, Fastly, IBM WebSphere, Oracle WebLogic, F5, and countless language-specific solutions (NodeJS, Ruby, etc.). This presentation will start by defining ESI and visiting typical infrastructures leveraging this model. We will then delve into to the good stuff; identification and exploitation of popular ESI engines, and mitigation recommendations.
Who’s Talking? Louis Dion-Marcil|Security Analyst, GoSecure
Session Room Venue: Jasmine Ballroom
Format: 25 min
Date: Wednesday, August 8 | 10:30am-10:55am
Deep Neural Networks for Hackers: Methods, Applications, and Open Source Tools
Anyone who keeps up with technology news has read about deep neural networks beating human champions at Go, achieving breakthrough accuracy at voice recognition, and generally driving today’s major advances in artificial intelligence. Little has been said, however, about the ways deep neural network approaches are quietly achieving analogous breakthroughs in intrusion detection. My goal with this presentation is to change this, by demystifying deep neural network (deep learning) concepts, presenting research that shows that we can use deep learning methods to achieve breakthrough cyber-attack detection, and by introducing open source deep learning tools, so that attendees can leave equipped to start their own security deep neural network research.
The presentation will start with an intuitive overview of deep neural networks, introducing the ideas that allow neural networks to learn from data and make accurate decisions about whether, for example, files are good or bad, or a given URL or domain name is malicious. After introducing deep neural networks, I’ll go on to describe a case study: a deep neural network that uses a convolutional neural network approach to detect previously malicious URLs at higher accuracy than any previously reported techniques, which we have evaluated on live, real world data. Finally, I’ll introduce the open source tools available for doing security deep learning research, giving attendees a starting place for incorporating deep neural networks into their own security practice.
Who’s Talking? Joshua Saxe|Chief Data Scientist, Sophos
Session Room Venue: South Seas ABE
Format: 50 min
Date: Wednesday, August 8 | 11:15am-12:05pm
OWASP TOP 10
Threats to the application layer is not a new thing, but they have become more and more prevalent over the past number of years. The rise in attacks stems from the increase in high-value data being stored in constantly changing environments. The OWASP top 10 is based on data submissions from firms that specialize in application security and an industry survey and provides basic techniques to protect against these high-risk problem areas. The aim is to provide guidance on where to go from here.
In this workshop I will provide an overview of the OWASP Top 10. I will discuss what the issues are, why they are so important to organizations and how developers can become more proactive in preventing these risks in their code.
Who’s Talking? Owen Pendlebury|OWASP Global Board of Director
Session Room Venue: South Pacific IJ, North Hall
Format: Community Workshop
Date: Wednesday, August 8 | 1:40pm-2:30pm
Are You Trading Stocks Securely? Exposing Security Flaws in Trading Technologies
With the advent of electronic trading platforms and networks, the exchange of financial securities now is easier and faster than ever; but this comes with inherent risks. Nowadays, not only rich people can invest in the money markets, but also anyone with as little as $10 could start trading stocks from either a mobile phone, a desktop application or a website.
The problem is that this area of the fintech industry has not been fully under the cybersecurity umbrella. Sometimes we assume that a product is secure by its nature, such as technologies that are used to trade hundreds of billions per day, but security testing tells us a different story.
In this talk, vulnerabilities that affect millions of traders will be shown in detail. Among them are unencrypted authentication, communications, passwords and trading data; remote DoS that leave the applications useless, weak password policies, hardcoded secrets, poor session management, etc. Also, many of these applications lack of countermeasures such as SSL certificate validation and root detection in mobile apps, privacy mode to mask sensitive values, anti-exploitation and anti-reversing mitigations.
Moreover, the risk of social trading will be discussed too as well as how malicious expert advisors (trading robots) and other plugins could include backdoors or hostile code that would be hard to spot for non tech-savvy traders.
The analysis encompassed the following platforms, which are some of the most used ones:
– 16 Desktop applications
– 29 Websites (7 focused on cryptocurrencies)
– 34 Mobile apps
Who’s Talking? Alejandro Hernandez|Sr. Consultant, IOActive
Session Room Venue: South Seas CDF
Format: 50 min
Date: Thursday, August 9 | 11:00am-11:50am
WebAssembly: A New World of Native Exploits on the Browser
WebAssembly (WASM) is a new technology being developed by the major browser vendors through the W3C. A direct descendent of NaCl and Asm.js, the idea is to allow web developers to run native (e.g. C/C++) code in a web page at near-native performance. WASM is already widely supported in the latest versions of all major browsers, and new use case examples are constantly popping up in the wild. Notable examples include 3D model rendering, interface design, visual data processing, and video games. Beyond providing significant performance benefits to developers, WebAssembly is also touted as being exceptionally secure. Developers claim that buffer overflows will be an impossibility, as any attempted access to out-of-bounds memory will be caught by a Javascript error. Their documentation claims that control flow integrity is enforced implicitly and that “common mitigations such as data execution prevention (DEP) and stack smashing protection (SSP) are not needed by WebAssembly programs.” However, the documentation also outlines several possible vectors of attacks, including race conditions, code reuse attacks, and side channel attacks.
The goal of this talk is to provide a basic introduction to WebAssembly and examine the actual security risks that a developer may take on by using it. We will cover the low-level semantics of WebAssembly, including the Javascript API, the linear memory model, and the use of tables as function pointers. We will cover several examples demonstrating the theoretical security implications of WASM, such as linear memory being shared between modules and the passing of a Javascript ‘Number’ to a WASM function that expects a signed integer. We will also cover Emscripten, which is currently the most popular WebAssembly compiler toolchain. Our assessment of Emscripten will include its implementation of compiler-and-linker-level exploit mitigations as well as the internal hardening of its libc implementation, and how it’s augmentation of WASM introduces new attack vectors and methods of exploitation. As part of this we will also provide practical examples of memory corruption exploits in the WASM environment that may lead to hijacking control flow or even executing arbitrary JavaScript within the context of the web page. Finally, we will provide a basic outline of best practices and security considerations for developers wishing to integrate WebAssembly into their product.
Who’s Talking? Justin Engler|Technical Director, NCC Group
Tyler Lukasiewicz|Security Consultant, NCC Group
Session Room Venue: Islander FG
Format: 50 min
Date: Thursday, August 9 | 12:10pm-1:00pm
It’s a PHP Unserialization Vulnerability Jim, but Not as We Know It
Recent years have seen the emergence of PHP unserialization vulnerabilities as a viable route to remote code execution or other malicious outcomes. The presentation will start with a brief refresher on the issue as it has previously been understood before introducing new research which shows how unserialization can be induced when other types of vulnerability occur, including some that would previously have been considered low impact.
The presentation will include demos of long lived and previously unidentified RCE exploits against some of the most widely deployed open source PHP web applications and libraries.
Who’s Talking? Sam Thomas|Director of Research, Secarma Ltd
Session Room Venue: Lagoon JKL
Format: 50 min
Date: Thursday, August 9 | 5:00pm-6:00pm
SECURITY DEVELOPMENT LIFECYCLE SESSIONS
Threat Modeling in 2018: Attacks, Impacts and Other Updates
Attacks always get better, and that means your threat modeling needs to evolve. This talk looks at what’s new and important in threat modeling, organizes it into a simple conceptual framework, and makes it actionable. This includes new properties of systems being attacked, new attack techniques (like biometrics confused by LEDs) and a growing importance of threats to and/or through social media platforms and features. Take home ways to ensure your security engineering and threat modeling practices are up-to-date.
Who’s Talking? Adam Shostack|President, Shostack & Associates
Session Room Venue: Islander EI
Format: 50 min
Date: Wednesday, August 8 | 2:40pm-3:30pm
Stop that Release, There’s a Vulnerability!
The AWS Security, Risk, and Compliance Simulation takes mixed teams of security management, IT, and Business leaders through an experiential exercise that highlights key decision points to enable a secure cloud journey. This team-based exercise uses gamification techniques to work through an industry case study that requires your team to make critical decisions and investment choices. Participants also experience the impact of these investments and decisions on critical aspects of their secure cloud adoption. From the simulation, gain an understanding of the major success factors to building security, risk, and compliance in the cloud, and how to apply similar decision and investment approaches to your specific cloud adoption journey. The simulation is best suited to participants who are key to executing your cloud security strategy, ranging from security management and risk management, to decision-makers from Legal and Compliance and the business side. Attendees should have some role in the cloud security strategy for their company.
Who’s Talking?
Christine Gadsby|Director, Product Security Operations, BlackBerry
Session Room Venue: Islander EI
Format: 25 min
Date: Thursday, August 9 | 9:00am-9:25am
SECURITY AND THE ENTERPRISE SESSIONS
Identity Theft: Attacks on SSO Systems
SAML is often the trust anchor for Single Sign-On (SSO) in most modern day organizations. This presentation will discuss a new vulnerability discovered which has affected multiple independent SAML implementations, and more generally, can affect any systems reliant on the security of XML signatures. The issues found through this research affected multiple libraries, which in turn may underpin many SSO systems.
The root cause of this issue is due to the way various SAML implementations traverse the XML DOM after validating signatures. These vulnerabilities allow an attacker to tamper with signed XML documents, modifying attributes such as an authenticating user, without invalidating the signatures over these attributes. In many cases, this allows an attacker with authenticated access to a SAML Identity Provider to access services as an entirely different user – and more easily than you’d expect.
This talk will also discuss another demonstrated class of vulnerabilities in user directories that amplify the impact of the previously mentioned vulnerability, and in some cases, can enable authentication bypasses on their own.
Who’s Talking? Kelby Ludwig |AppSec Engineer, Duo Security
Session Room Venue: South Pacific F
Format: 5O min
Date: Thursday, August 9 | 9:45am-10:35am
An Attacker Looks at Docker: Approaching Multi-Container Applications
Containerization, such as that provided by Docker, is becoming very popular among developers of large-scale applications. This is likely to make life a lot easier for attackers.
While exploitation and manipulation of traditional monolithic applications might require specialized experience and training in the target languages and execution environment, applications made up of services distributed among multiple containers can be effectively explored and exploited “from within” using many of the system- and network-level techniques that attackers, such as penetration testers, already know.
The goal of this talk is to provide a penetration tester experienced in exploitation and post-exploitation of networks and systems with an exposure to containerization and the implications it has on offensive operations. Docker is used as a concrete example for the case study. A penetration tester can expect to leave this presentation with a practical exposure to multi-container application post-exploitation that is as buzzword-free as is possible with such a trendy topic.
Who’s Talking?
Wesley McGrew|Director of Cyber Operations, HORNE Cyber
Session Room Venue: South Pacific F
Format: 50 min
Date: Thursday, August 9 | 5:00pm-6:00pm
The Full Agenda: https://www.blackhat.com/us-18/briefings/schedule/
COME SAY HI
We’re going to be tweeting on site all the things going on at Black Hat 2018. Be sure to follow us @tcellio #BHSurvivalGuide. We’d love to see you in between sessions and activities, so stop by Booth L17 to have a chat, grab a tShirt, and enter to win a coveted Nintendo Switch!

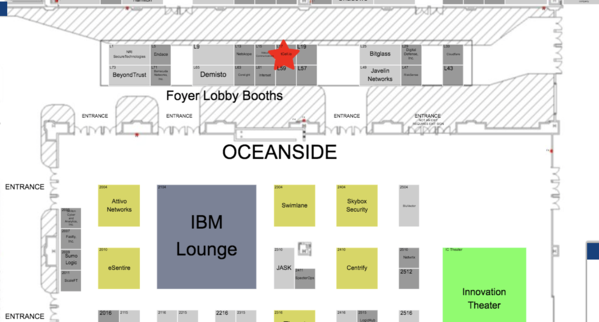
Not sure where the heck Booth L17 is? We’re in the Foyer Lobby near Oceanside. Here’s the map.
See you there,
tCell

