Monitoring traffic on your network is important if you want to keep it secure and running efficiently. The information obtained by network traffic monitoring tools can be used in multiple security and IT operational use cases to identify security vulnerabilities, troubleshoot network issues, and analyze the impact new applications will have on the network. These five tips should help you get the most out of your Network Traffic Analysis (NTA) tool.
1. Choose the right data source(s)
Whatever your motive for monitoring network traffic, you have two main data sources to choose from:
- Flow data, which can be acquired from layer 3 devices like routers
- Packet data, which can be sourced from SPAN, mirror ports, or via TAPs
Flow data is great if you are looking for traffic volumes and mapping the journey of a network packet from its origin to its destination. This level of information can help detect unauthorized WAN traffic and utilize network resources and performance. However, flow-based tools for monitoring network traffic lack the detailed data to detect many network security issues or perform true root cause analysis.
Packet data extracted from network packets can help network managers understand how users are implementing/operating applications, track usage on WAN links, and monitor for suspicious malware or other security incidents. Deep packet inspection (DPI) tools provide 100% visibility over the network by transforming the raw metadata into a readable format and enabling network managers to drill down to the most minute detail.
2. Pick the correct points on the network to monitor
A common mistake many people make when deploying a NTA tool is that they include too many data sources at the start. There is no need to monitor every network point. Instead, pick points where data converges. Examples of this would be internet gateways, Ethernet ports on WAN routers, or VLANs associated with critical servers.
If you are new to getting tools in place to monitor network traffic, I would suggest you start by monitoring your internet gateway(s). This can be an excellent source of security and operational data.
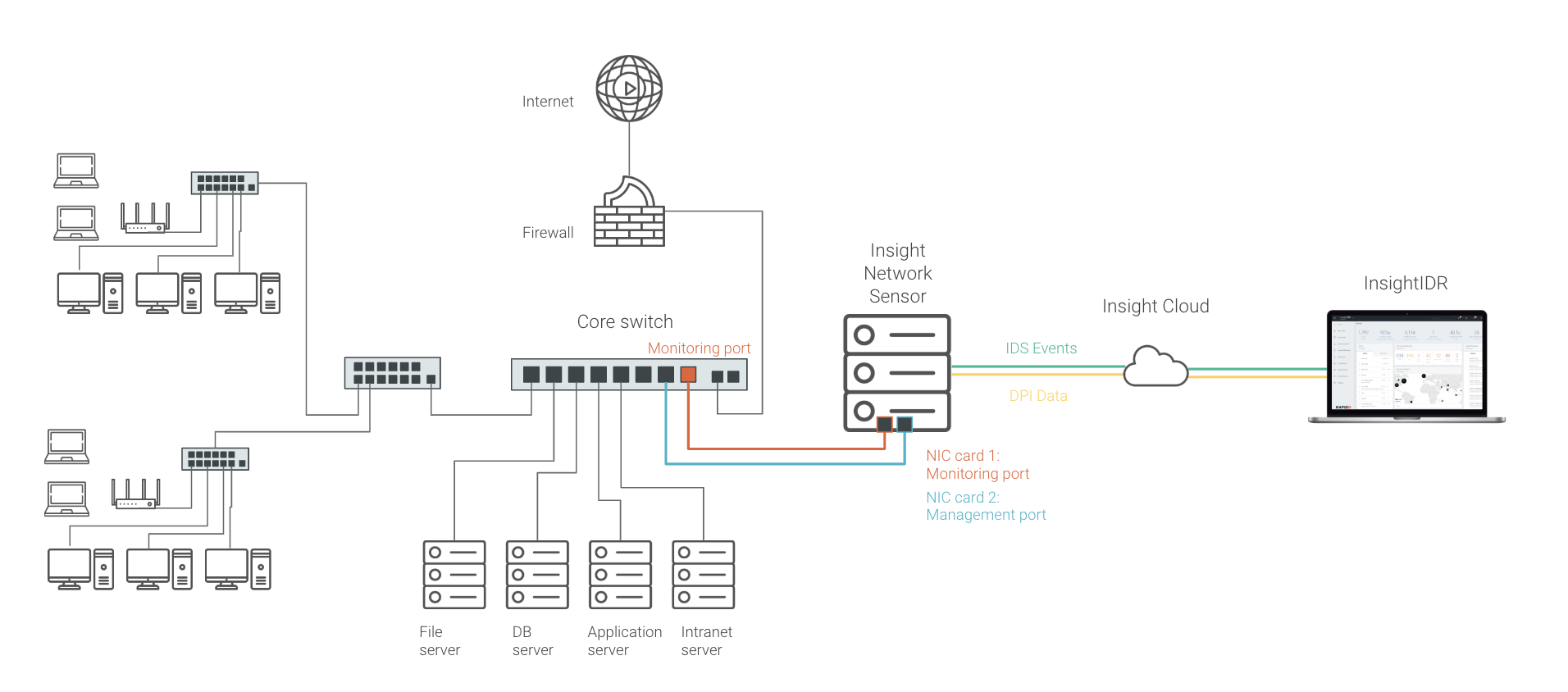
The image below shows a good approach when it comes to network traffic monitoring for most networks. A SPAN or mirror port is configured at the network core, which allows for the capture of any traffic passing through. In my example, this would allow me to capture traffic going to and from the internet, as well as traffic associated with important servers.
3. Sometimes real-time data is not enough
The ability to monitor network traffic in real time is sufficient to achieve many objectives of network traffic monitoring, but sometimes, real-time data is not enough. Historical traffic metadata is ideal for network forensics and is just as important if you want to analyze past events, identify trends or compare current network activity with the previous week.
For these objectives, it is best to use tools for monitoring network traffic with deep packet inspection. Some tools for monitoring network traffic choose to age data. This means the further back you go historically, the less detail you get. While this can save on disk space, it is not an ideal solution if you are trying to determine how an intruder managed to overcome your defenses to plant malware on the network. Without accurate and complete data relating to the event, you can be left looking for answers that no longer exist.
It is also a good idea to be aware that some security information and event management (SIEM) and network traffic monitoring systems base their pricing on the amount of data you want to store. Keep an eye out for this when you are evaluating solutions.
4. Associate the data with usernames
Traditional network traffic monitoring tools usually report on activity using IP or MAC addresses. While this is useful information, it can be problematic in DHCP environments if you are trying to find a problematic device. One piece of information that can bring together network activity and devices is usernames. Username association will let you know who is doing what on the network.
5. Check the flows and packet payloads for suspicious content
Many networks have intrusion detection systems (IDS) at the edge, but very few have this type of technology monitoring internal traffic. All it takes is one rogue mobile or IoT device to compromise a network. Another issue I often see are firewalls allowing suspicious traffic through where a rule was misconfigured.
Summary
Network traffic analysis is an essential way to monitor network availability and activity to identify anomalies, maximize performance, and keep an eye out for attacks. It’s a core piece of the visibility and security analysis needed to discover threats and remediate them fast.
When choosing a NTA solution, consider the current blind spots on your network, the data sources from which you need information, and the critical points on the network where they converge for efficient monitoring. With NTA added as a layer to your security information and event management (SIEM) solution, you’ll gain visibility into even more of your environment and your users.
Related blog posts

Products and Tools
InsightIDR AI Alert Triage Automatically Classifies Alerts with 99.93% Benign Alert Accuracy
Chris Wraight

Detection and Response
New IDR Log Search Enhancements: Accelerate, Streamline, and Simplify Investigations
Rapid7

Products and Tools
What’s New in Rapid7 Products & Services: Q3 2024 in Review
Margaret Wei

Detection and Response
Rapid7 Named a Leader in IDC MarketScape: Worldwide SIEM for SMB and Enterprise
Meaghan Buchanan