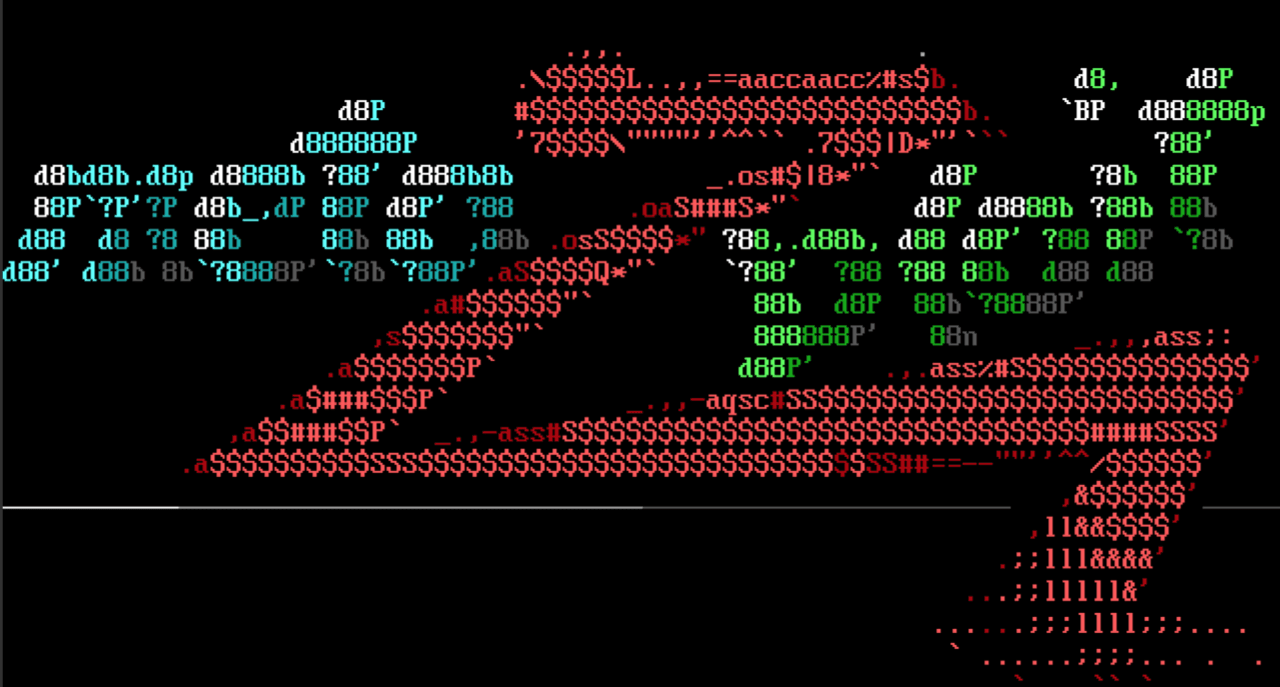
Nobody expects the Python installation!
New this week is the post/windows/manage/install_python module from bluesentinelsec, which automates the installation of an embeddable Python interpreter on a target. Note that this module does not require admin privileges or user interaction for the installation to complete.
Pining for the Hordes
We've also added an exploit module for the Horde Data API, commonly bundled with software such as Horde Groupware Webmail Edition Suite, thanks to user cyrus-and. The Horde Data API versions 2.1.4 and below are vulnerable to code execution via unescaped strings in its CSV import/export functionality.
And now for something completely different...
...ok, maybe not so different. There's now a new exploit module for Microsoft SharePoint Workflows, thanks to zeroSteiner. This module exploits CVE-2020-0646, and achieves remote execution of C# code by escaping a value from XOML data.
New modules (3)
- Horde CSV import arbitrary PHP code execution by Andrea Cardaci, which exploits CVE-2020-8518
- SharePoint Workflows XOML Injection by Soroush Dalili and Spencer McIntyre, which exploits CVE-2020-0646
- Install Python for Windows by Michael Long
Enhancements and features
- PR #12988 by cn-kali-team adds functionality to leverage the Windows APIs for managing local and domain users and groups over Meterpreter. This PR also updates several modules to use this new feature, rather than relying on OS command execution.
- PR #13133 by h00die updates documentation for several modules by stevenseeley, and standardizes them to be in line with the new documentation format.
- PR #13124 by h00die updates the startup tip for info to better highlight the functionality of the info -d option. (If you missed the introduction of productivity tips from a few weeks ago, check them out here!)
- PR #13059 by smcintyre-r7 adds limits to the size of payload string options, in order to ensure that they will fit within defined buffers.
Bugs fixed
- PR #13143 by acammack-r7 fixes a bug with the check command for the exploit/linux/redis/redis_unauth_exec module. The check now successfully executes, and does not show up as unsupported.
- PR #13130 by busterb adds some transport and pivot fixes for Meterpreter.
- PR #13118 by srikwit updates the Linux privesc example module in order to correctly identify it as a local exploit instead of a remote one.
- PR #13070 by debifrank fixes the regular expression used in the /exploits/multi/http/cisco_dcnm_upload_2019 module, allowing the module to find directories within paths that contain a space.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest. To install fresh without using git, you can use the open-source-only Nightly Installers or the binary installers (which also include the commercial edition).