Throw another log [file] on the fire
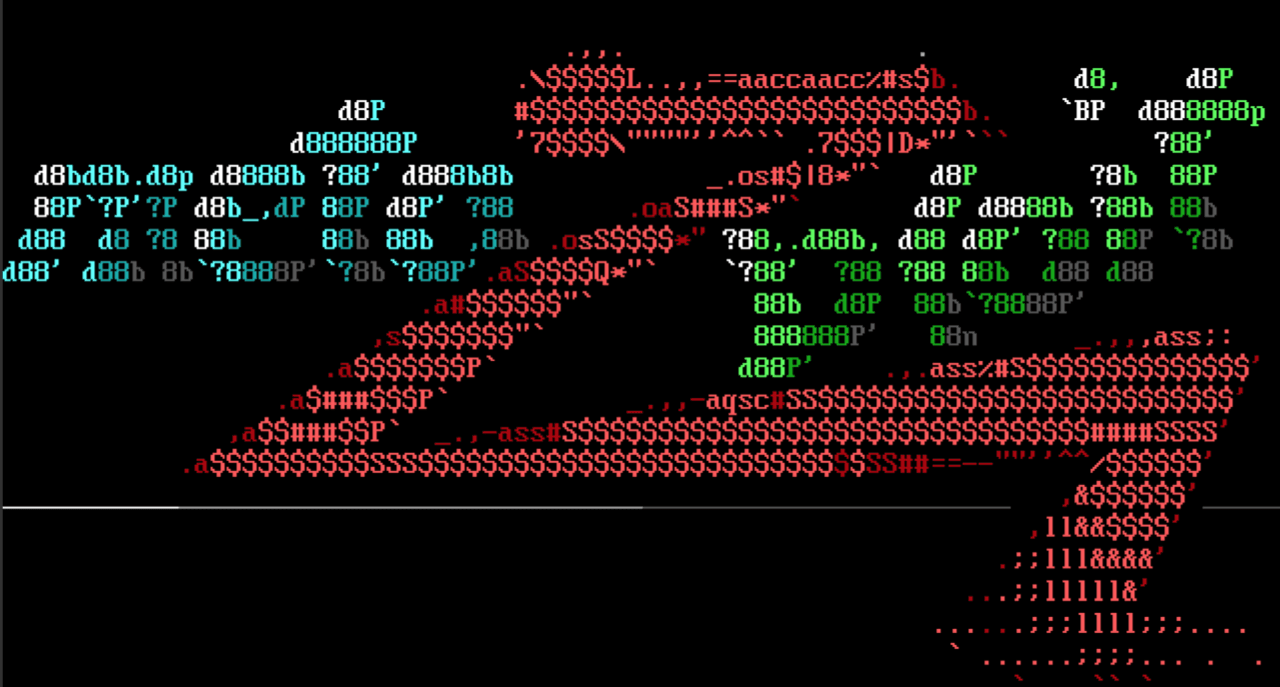
Our own Stephen Fewer authored a module targeting CVE-2023-26360 affecting ColdFusion 2021 Update 5 and earlier as well as ColdFusion 2018 Update 15 and earlier. The vulnerability allows multiple paths to code execution, but our module works by leveraging a request that will result in the server evaluating the ColdFusion Markup language on an arbitrary file on the remote system. This allows a user to execute markup language in an arbitrary file on the remote host. The attack writes this markup language to the remote host by sending an incorrect JSON blob containing ColdFusion Markup language to the server, and the server recognizes the incorrect JSON and logs it to a log file. We then request to evaluate the log file which now contains the arbitrary ColdFusion Markup that we wish evaluated, and collect shells.
This vulnerability was added to the CISA’s Known Exploited Vulnerabilities catalog in March.
WOW64 Hashdump Support
One of Meterpreter’s oldest features is the ability to dump hashes from LSASS. Until recently, this capability required that the Meterpreter instance running on the Windows target system matched the hosts native architecture. When users attempted to dump hashes from a Meterpreter running in a WOW64 process they’d see the following cryptic error that was tribal knowledge among Metasploit users for “you need to open a new session with a 64-bit Meterpreter”.
meterpreter > hashdump
[-] priv_passwd_get_sam_hashes: Operation failed: The parameter is incorrect.
In our latest release, we have shipped new support allowing hashdump to work in WOW64 environments with no changes or further actions required on the users’ part. Simply run the hashdump command and Meterpreter will take care of the rest.
For those interested in the technical details, the old limitation was related to the way in which Meterpreter carved the code to inject into LSASS out of itself. This was where the requirement that the two architectures matched came from. Since LSASS would always be the host’s native architecture, Meterprter would also need to be the host’s native architecture. The new approach uses Reflective DLL Injection to encapsulate the injected code which allows Meterpreter to select the correct one at runtime.
New module content (3)
Icingaweb Directory Traversal in Static Library File Requests
Authors: Jacob Ebben, Thomas Chauchefoin, and h00die
Type: Auxiliary
Pull request: #17915 contributed by h00die
AttackerKB reference: CVE-2022-24716
Description: A new module has been added in for CVE-2022-24716, an unauthenticated arbitrary file read in Icinga Web 2 versions 2.9.0 to 2.9.5 inclusive, and 2.8.0 to 2.8.5 inclusive that can be used to leak sensitive configuration information from a target server.
Adobe ColdFusion Unauthenticated Remote Code Execution and Unauthenticated Arbitrary File Read
Author: sf
Type: Exploit
Pull request: #17856 contributed by sfewer-r7
AttackerKB reference: CVE-2023-26360
Description: This adds two modules; an RCE exploit for CVE-2023-26360 (Adobe ColdFusion) and an auxiliary gather module for the same vulnerability that can be leveraged to read arbitrary files. ColdFusion 2021 Update 5 and earlier as well as ColdFusion 2018 Update 15 and earlier are affected.
Enhancements and features (2)
- #16390 from sempervictus - Two new libraries, Rex::Proto::DNS::CachedResolver and Rex::Proto::DNS::Cache, have been added to extend the functionality of Rex::Proto::DNS::Resolver and add the ability for users to cache DNS responses, specify the name server that they would like to use when trying to resolve DNS names, and load and cache existing DNS entries in their hostfile.
- #17963 from h00die - Updates auxiliary/scanner/nfs/nfsmount to include a reference to CVE-1999-0554 - which is related to finding sensitive files on an NFS mount.
Bugs fixed (4)
- #17910 from cgranleese-r7 - Fixes false positives in the auxiliary/scanner/couchdb/couchdb_login module which incorrectly reported successful user authentication when connection timeouts occurred.
- #17911 from cgranleese-r7 - Updates the setting missing datastore values validation to produce a warning instead of an error. This fixes an edgecase where setting options on multi/handler without having first set a payload would fail.
- #17944 from zeroSteiner - A new release of metasploit-payloads is out which adds long awaited WOW64 support for hashdump, fixes an issue with building payloads using MingGW, and adds memory read/write abilities to Windows version of Python Meterpreter.
- #17947 from bcoles - Updates exploits/osx/local/feedback_assistant_root.rb to no longer assume that OSX version nil/zero is vulnerable - which may occur when running against non-OSX systems.
Documentation
You can find the latest Metasploit documentation on our docsite at docs.metasploit.com.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
binary installers (which also include the commercial edition).