Microsoft is addressing 86 vulnerabilities this August Patch Tuesday, including one zero-day vulnerability, as well as five critical remote code execution (RCE) vulnerabilities, and 12 browser vulnerabilities. An unpatched zero-day malicious document vulnerability from July also receives Windows OS updates and clarification in August.
ASP.NET: zero-day denial of service in Kestrel web server
The lone zero-day vulnerability patched this month is CVE-2023-38180, a denial of service (DoS) vulnerability in .NET , ASP.NET Core 2.1, and recent versions of Visual Studio. Microsoft is aware of in-the-wild exploitation. While the only impact noted is availability, administrators responsible for web apps built on ASP.NET are well-advised to patch as soon as possible. The cross-platform Kestrel web server is included in ASP.NET Core, and contains protections so that it can detect and disconnect a potentially malicious client. However, Kestrel will sometimes fail to disconnect the client, leading to denial of service. Microsoft notes that mitigating factors may include a reverse proxy or Web Application Firewall (WAF), since these are designed to detect and mitigate HTTP-based attacks.
Teams: critical RCE on joining malicious meeting
Potentially of greater concern are a pair of Microsoft Teams critical remote code execution (RCE) vulnerabilities. While the CVSS base score of 8.8 is at the top end of NVD’s High severity, Microsoft assesses both CVE-2023-29328 and CVE-2023-29330 as Critical on its own proprietary severity rating, and the advisories make clear why that is: both vulnerabilities allow an attacker to execute code in the context of anyone who joins a Teams meeting set up by the attacker. This affects Teams on all platforms: Windows Desktop, macOS, iOS, and Android. Given how widely Teams is used not just within organizations, but for collaboration outside of the organization in contexts requiring a level of trust of third parties not known to participants – pre-sales calls, scoping calls, industry association calls and so on – these vulnerabilities surely deserve immediate remediation attention.
Windows MSMQ: critical RCE
The Windows Message Queuing Service is once again the site of multiple critical RCE vulnerabilities this month. CVE-2023-36910, CVE-2023-36911, and CVE-2023-35385 all come with a CVSSv3 base score of 9.8, reflecting the serious potential impact, lack of privileges required, and low attack complexity. One mitigating factor: the Microsoft Message Queueing Service must be enabled and listening on port 1801 for an asset to be vulnerable, and the Message Queueing Service is not installed by default. As Rapid7 has noted previously, however, a number of applications – including Microsoft Exchange – may quietly introduce MSMQ as part of their own installation routine.
Outlook, or perhaps Word: critical maldoc arbitrary code execution
Rounding out the August critical RCE vulnerabilities, CVE-2023-36895 describes a flaw in Microsoft Outlook where an attacker who can convince a user to open a specially-crafted malicious file will be able to execute code in the context of the victim. However, although the advisory describes CVE-2023-36895 as an Outlook vulnerability, linked KB articles for Microsoft Installer versions of Office (e.g. KB5002464 for Office 2016) describe a security update for Word. At time of writing, it isn't clear whether this is because the vulnerable code is in a shared Office component, or whether this apparent discrepancy is an oversight.
Patch Tuesday watchers will be familiar with Microsoft’s clarification that this type of exploit is sometimes referred to as arbitrary code execution (ACE) since the attack is local – a malicious document opened on the asset – even if the attacker is remote. With no known public disclosure, no known exploitation in the wild, and Microsoft assessing that exploitation is less likely, this is hopefully a case of patch-and-forget.
July unpatched zero-day: revised and patched in August
One month ago, on Patch Tuesday July 2023, Microsoft published a zero-day vulnerability for which they provided no patch, leaving many defenders understandably concerned. Exploitation of CVE-2023-36884 requires that the user opens a malicious document crafted by an attacker, and as Rapid7 noted when the vulnerability was originally published, Microsoft did provide several mitigation strategies. Happily, the August 2023 Windows updates bring relief from CVE-2023-36884 in the form of patches for every current version of Windows: from Windows 11 and Server 2022 all the way back to Windows Server 2008 for 32-bit Systems Service Pack 2. These patches supersede last month’s mitigation advice, but at least some of those mitigation strategies remain generally applicable.
The advisory for CVE-2023-36884 has been radically updated today with a new title (Windows Search Remote Code Execution Vulnerability) in place of the previous title (Office and Windows HTML Remote Code Execution Vulnerability). Microsoft now states that the vulnerability is in fact a Windows Search security bypass involving a Mark of the Web (MOTW) removal leading to code execution on the victim system. Microsoft has also released a complementary non-CVE advisory ADV230003 with the latest defense-in-depth advice for Microsoft Office administrators; Microsoft claims that following the defense-in-depth advice will stop the attack chain leading to exploitation of CVE-2023-36884, and thus potentially also protect against other as-yet-unknown vulnerabilities. However, defenders should consider that other attack chains may exist which do not involve Office at all.
Exchange: critical elevation of privilege
Exploitation of CVE-2023-21709 allows an attacker to authenticate as a different user. Exchange admins should note that additional remediation actions must be taken after patching. Although the CVSSv3 base score is a Critical-ranked 9.8, Microsoft's proprietary severity scale assesses this vulnerability as Important rather than Critical, since exploitation involves brute-forcing passwords, and strong passwords are challenging to brute force.
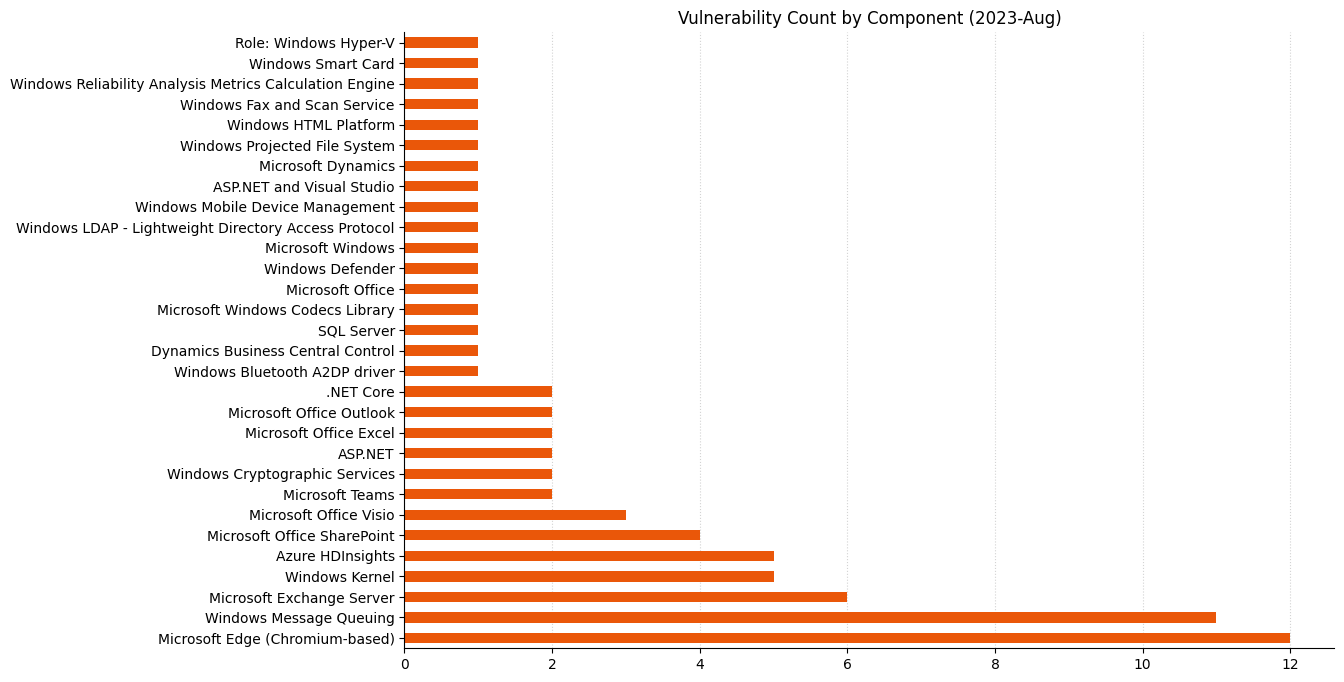
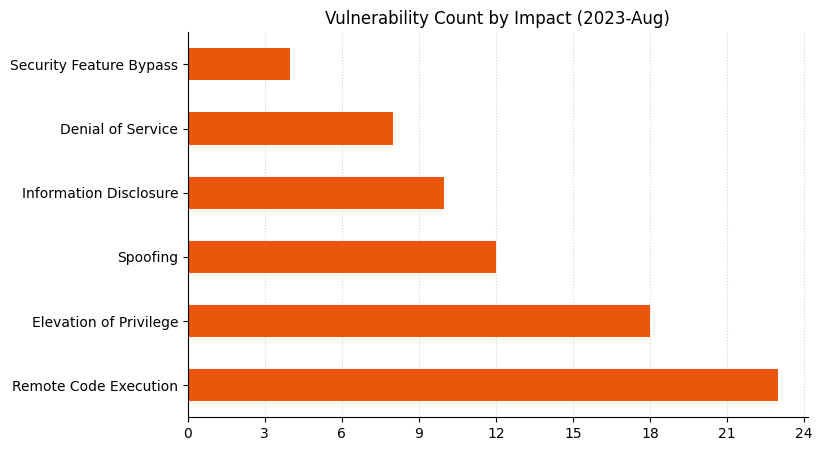
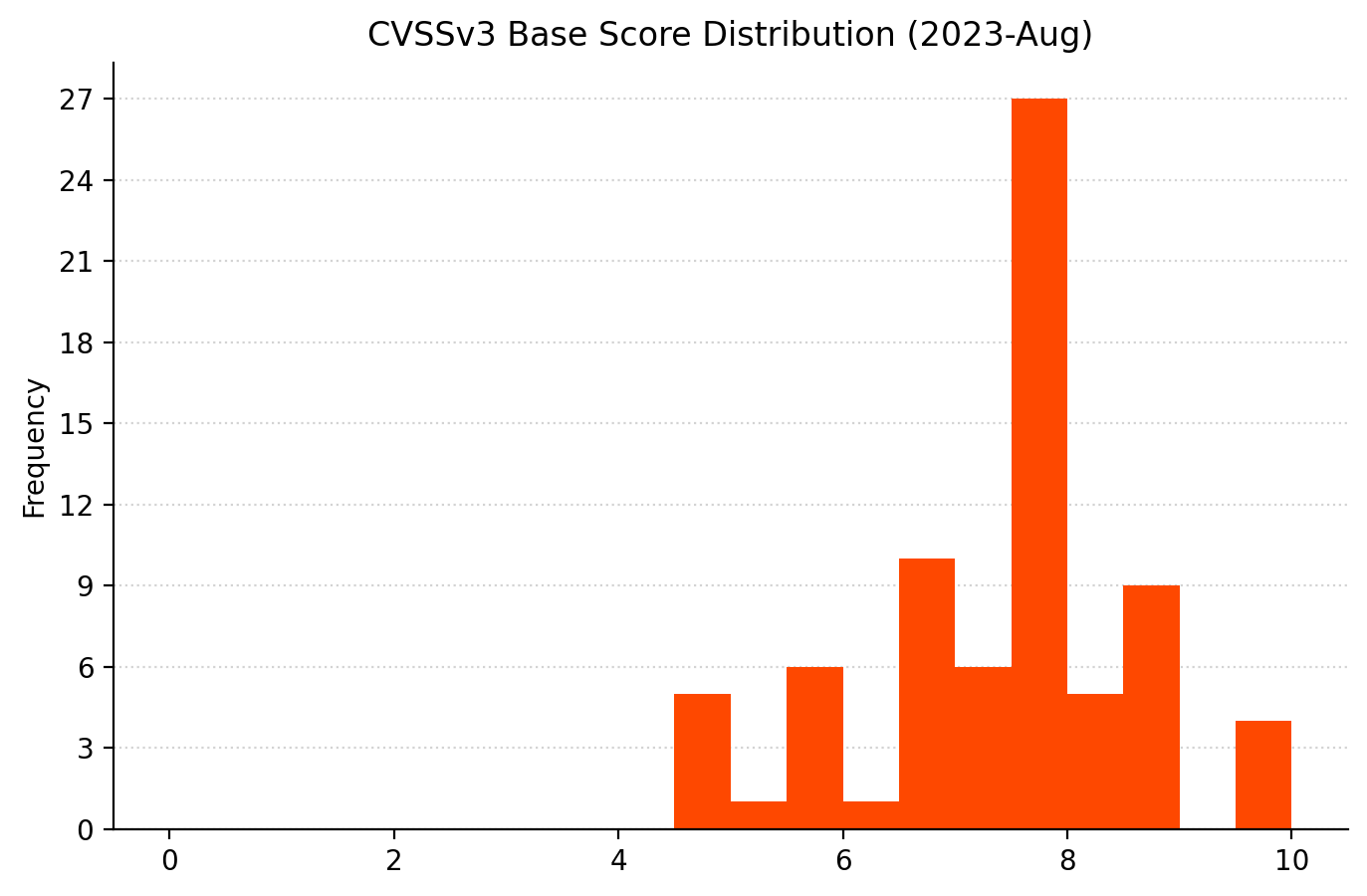
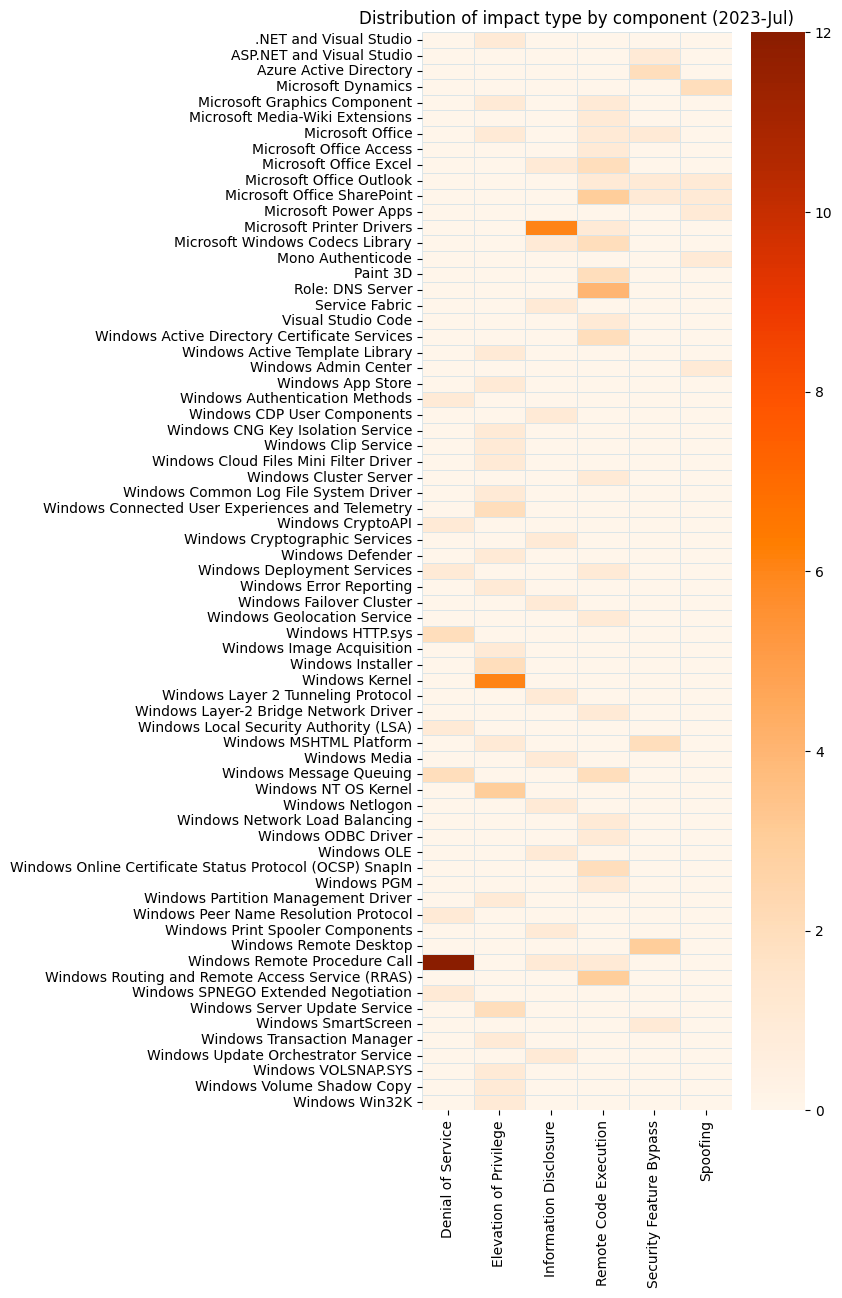
Summary Charts
Summary Tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-38176 | Azure Arc-Enabled Servers Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2023-35394 | Azure HDInsight Jupyter Notebook Spoofing Vulnerability | No | No | 4.6 |
| CVE-2023-36877 | Azure Apache Oozie Spoofing Vulnerability | No | No | 4.5 |
| CVE-2023-35393 | Azure Apache Hive Spoofing Vulnerability | No | No | 4.5 |
| CVE-2023-38188 | Azure Apache Hadoop Spoofing Vulnerability | No | No | 4.5 |
| CVE-2023-36881 | Azure Apache Ambari Spoofing Vulnerability | No | No | 4.5 |
Azure Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-36869 | Azure DevOps Server Spoofing Vulnerability | No | No | 6.3 |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-38157 | Microsoft Edge (Chromium-based) Security Feature Bypass Vulnerability | No | No | 6.5 |
| CVE-2023-4078 | Chromium: CVE-2023-4078 Inappropriate implementation in Extensions | No | No | N/A |
| CVE-2023-4077 | Chromium: CVE-2023-4077 Insufficient data validation in Extensions | No | No | N/A |
| CVE-2023-4076 | Chromium: CVE-2023-4076 Use after free in WebRTC | No | No | N/A |
| CVE-2023-4075 | Chromium: CVE-2023-4075 Use after free in Cast | No | No | N/A |
| CVE-2023-4074 | Chromium: CVE-2023-4074 Use after free in Blink Task Scheduling | No | No | N/A |
| CVE-2023-4073 | Chromium: CVE-2023-4073 Out of bounds memory access in ANGLE | No | No | N/A |
| CVE-2023-4072 | Chromium: CVE-2023-4072 Out of bounds read and write in WebGL | No | No | N/A |
| CVE-2023-4071 | Chromium: CVE-2023-4071 Heap buffer overflow in Visuals | No | No | N/A |
| CVE-2023-4070 | Chromium: CVE-2023-4070 Type Confusion in V8 | No | No | N/A |
| CVE-2023-4069 | Chromium: CVE-2023-4069 Type Confusion in V8 | No | No | N/A |
| CVE-2023-4068 | Chromium: CVE-2023-4068 Type Confusion in V8 | No | No | N/A |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-35390 | .NET and Visual Studio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-36899 | ASP.NET Elevation of Privilege Vulnerability | No | No | 7.5 |
| CVE-2023-38180 | .NET and Visual Studio Denial of Service Vulnerability | Yes | No | 7.5 |
| CVE-2023-38178 | .NET Core and Visual Studio Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2023-36873 | .NET Framework Spoofing Vulnerability | No | No | 7.4 |
| CVE-2023-35391 | ASP.NET Core SignalR and Visual Studio Information Disclosure Vulnerability | No | No | 7.1 |
Developer Tools Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-36897 | Visual Studio Tools for Office Runtime Spoofing Vulnerability | No | No | 8.1 |
ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-35379 | Reliability Analysis Metrics Calculation Engine (RACEng) Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36876 | Reliability Analysis Metrics Calculation (RacTask) Elevation of Privilege Vulnerability | No | No | 7.1 |
Exchange Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-21709 | Microsoft Exchange Server Elevation of Privilege Vulnerability | No | No | 9.8 |
| CVE-2023-38181 | Microsoft Exchange Server Spoofing Vulnerability | No | No | 8.8 |
| CVE-2023-38185 | Microsoft Exchange Server Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-35368 | Microsoft Exchange Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-35388 | Microsoft Exchange Server Remote Code Execution Vulnerability | No | No | 8 |
| CVE-2023-38182 | Microsoft Exchange Server Remote Code Execution Vulnerability | No | No | 8 |
Microsoft Dynamics vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-38167 | Microsoft Dynamics Business Central Elevation Of Privilege Vulnerability | No | No | 7.2 |
| CVE-2023-35389 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | No | No | 6.5 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-29328 | Microsoft Teams Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-29330 | Microsoft Teams Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-36891 | Microsoft SharePoint Server Spoofing Vulnerability | No | No | 8 |
| CVE-2023-36892 | Microsoft SharePoint Server Spoofing Vulnerability | No | No | 8 |
| CVE-2023-36895 | Microsoft Outlook Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-36865 | Microsoft Office Visio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-36866 | Microsoft Office Visio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-35372 | Microsoft Office Visio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-35371 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-36896 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-36890 | Microsoft SharePoint Server Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2023-36894 | Microsoft SharePoint Server Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2023-36893 | Microsoft Outlook Spoofing Vulnerability | No | No | 6.5 |
SQL Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-38169 | Microsoft OLE DB Remote Code Execution Vulnerability | No | No | 8.8 |
System Center vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-38175 | Microsoft Windows Defender Elevation of Privilege Vulnerability | No | No | 7.8 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-35387 | Windows Bluetooth A2DP driver Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2023-38186 | Windows Mobile Device Management Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-35382 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-35386 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-38154 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36904 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36898 | Tablet Windows User Interface Application Core Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-38170 | HEVC Video Extensions Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2023-35378 | Windows Projected File System Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2023-36905 | Windows Wireless Wide Area Network Service (WwanSvc) Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2023-36914 | Windows Smart Card Resource Management Server Security Feature Bypass Vulnerability | No | No | 5.5 |
| CVE-2023-35384 | Windows HTML Platforms Security Feature Bypass Vulnerability | No | No | 5.4 |
Windows ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|
| CVE-2023-36910 | Microsoft Message Queuing Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2023-36911 | Microsoft Message Queuing Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2023-35385 | Microsoft Message Queuing Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2023-35381 | Windows Fax Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-36882 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-36903 | Windows System Assessment Tool Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-35359 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-35380 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-36900 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2023-38184 | Windows Lightweight Directory Access Protocol (LDAP) Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2023-35383 | Microsoft Message Queuing Information Disclosure Vulnerability | No | No | 7.5 |
| CVE-2023-36912 | Microsoft Message Queuing Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2023-38172 | Microsoft Message Queuing Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2023-36913 | Microsoft Message Queuing Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2023-36909 | Microsoft Message Queuing Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2023-35376 | Microsoft Message Queuing Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2023-38254 | Microsoft Message Queuing Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2023-35377 | Microsoft Message Queuing Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2023-36908 | Windows Hyper-V Information Disclosure Vulnerability | No | No | 5.7 |
| CVE-2023-36889 | Windows Group Policy Security Feature Bypass Vulnerability | No | No | 5.5 |
| CVE-2023-36906 | Windows Cryptographic Services Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2023-36907 | Windows Cryptographic Services Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2023-20569 | AMD: CVE-2023-20569 Return Address Predictor | No | No | N/A |