- Home
- Products
- InsightIDR
- Use Cases
- Search and Visualize Your Security Data
insightIDR
Search and Visualize Your Security Data
Get a Free Trial
No credit card necessary
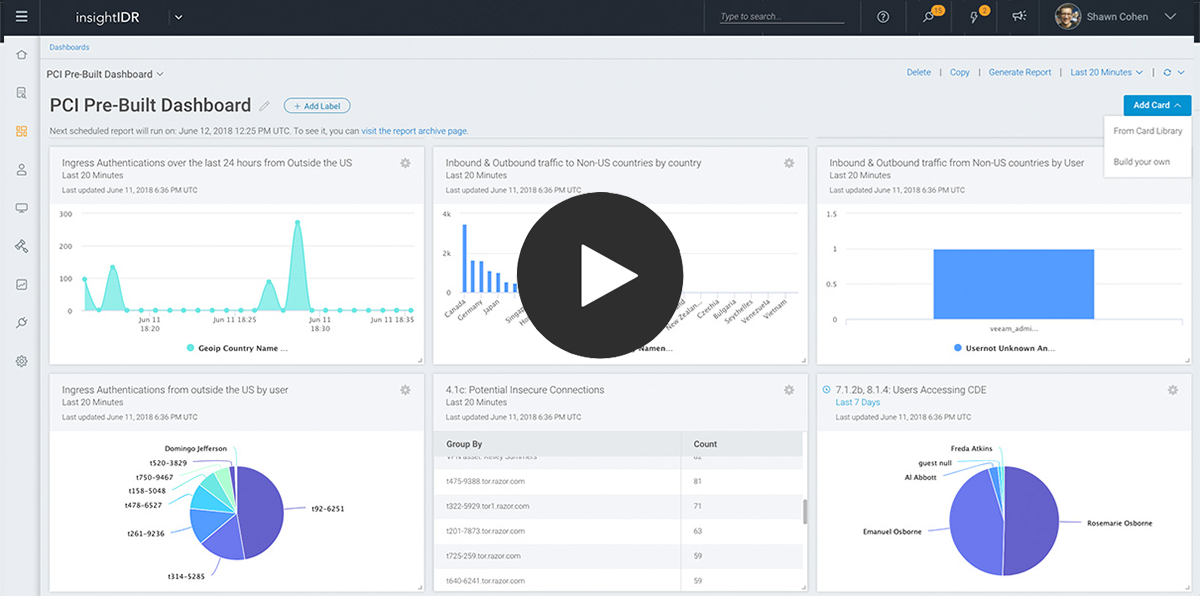
Watch Demo
See how it all works
Find answers from your data, no hardware required
With the cloud architecture and intuitive interface in InsightIDR, it's easy to centralize and analyze your data across logs, network, endpoints, and more to find results in hours—not months. User and Attacker Behavior Analytics, along with insights from our threat intel network, is automatically applied against all of your data, helping you detect and respond to attacks early.