- Home
- Products
- InsightIDR
- Use Cases
- Solve Multiple Compliance Regulations
insightIDR
Solve Multiple Compliance Regulations
Get a Free Trial
No credit card necessary
Watch Demo
See how it all works
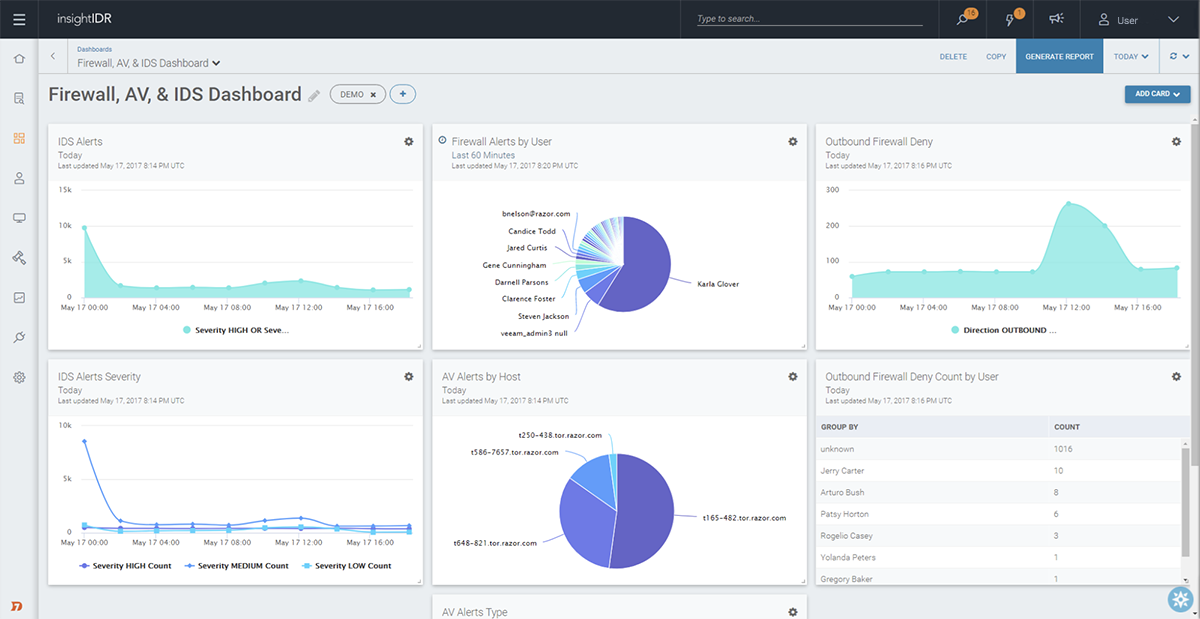
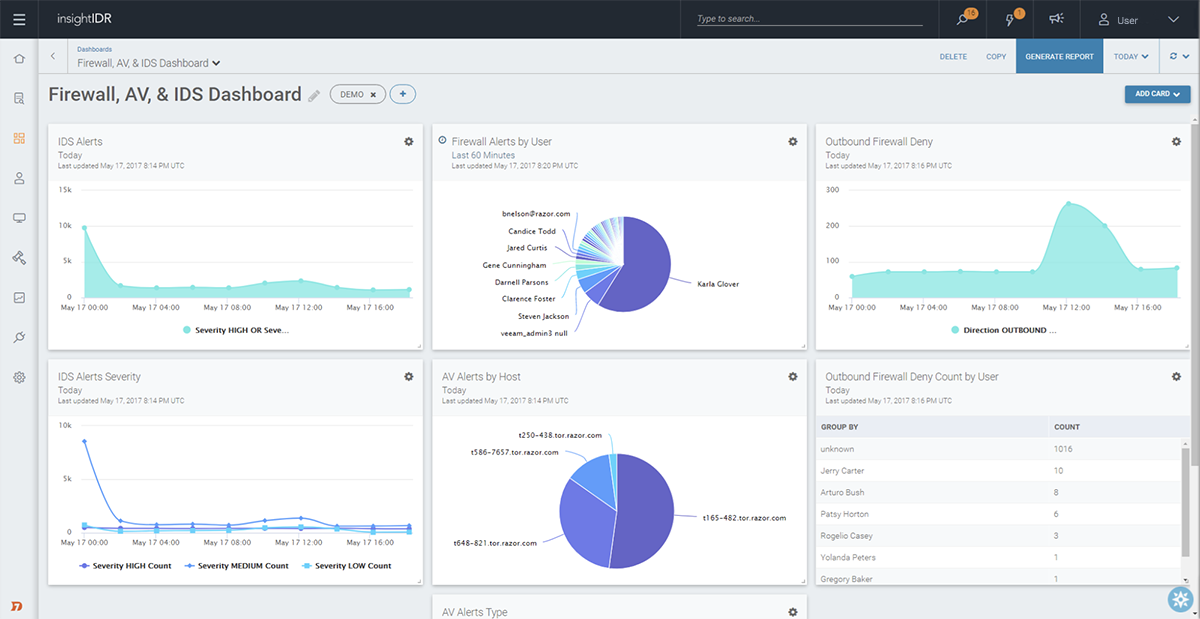
Benefit from audit logging, user monitoring, and file integrity monitoring all-in-one
While compliance doesn’t add up to security, it’s important to be able to share the health of your network with key third-parties. In addition to automatically analyzing your data for attacker behaviors and anomalous user activity, you’re able to search, visualize, and report across your data.