- Home
- Products
- InsightIDR
- Use Cases
- Monitor a Remote Workforce
insightIDR
Monitor a Remote Workforce
Enable business continuity across your organization (no matter where they are)
Threat detection and response is a critical piece in an ongoing journey to improve your security program, but feeling confident in your coverage can seem challenging with a remote workforce. When users are remote, they may be operating assets like laptops in potentially hostile networks outside of IT and security’s control. And to do their jobs effectively, your remote employees still need access to company data and key applications.
To combat these challenges, we’ve developed a comprehensive approach to detection and response, to help you enable business continuity, keep your organization protected (no matter where they are), and build a foundation for success across your entire environment.
Remote users
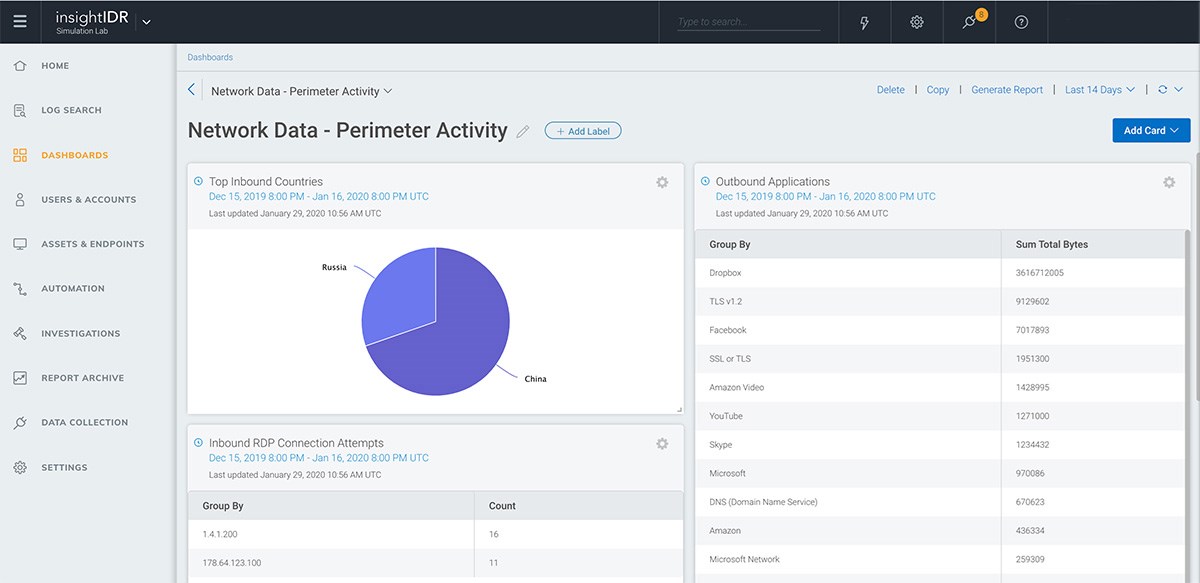
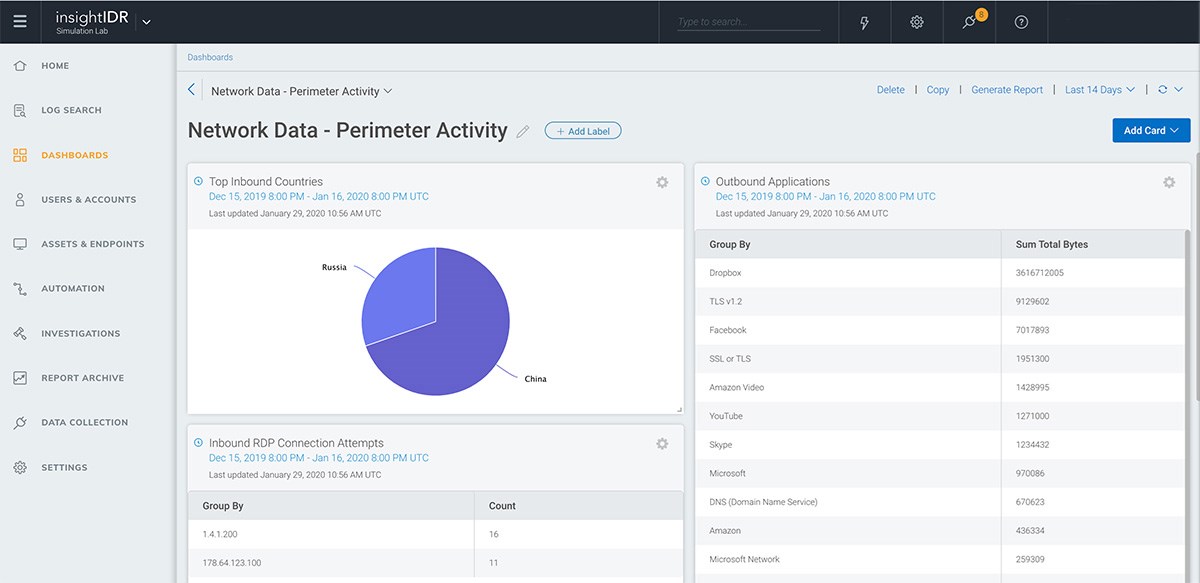
When employees move off campus, establishing what a new normal looks like can be a challenge for security teams. Is this a valid user working somewhere else, or malicious use of credentials? InsightIDR has a deep heritage around User Behavior Analytics and leverages finely tuned analytics and machine learning to quickly establish a baseline and recognize anomalous activity. We also include valuable reporting, such as our Ingress Locations dashboard, to provide vital information for your analysts to confidently investigate. By recording and displaying historical activity on remote user location (including authentications from outside the US), failed login attempts, and more, you and your team can easily identify malicious vs. normal user activity.
When users are remote, you may also use more cloud applications and services, such as Office 365, Azure, and AWS. InsightIDR can aggregate Security Center alerts from Microsoft Event Hubs, and recognize user or environment changes in AWS and alert teams on these changes right away.
Remote endpoints
Our lightweight, cloud-hosted Insight Agent provides critical, real-time visibility across your Windows, Mac, and Linux assets—no matter where they are in the world. The agent collects user activity and, for InsightVM customers, asset vulnerability data. You’ll marry real-time endpoint data with user activity and log search for comprehensive incident detection across the entire attack chain. With the ability to search assets by username, InsightIDR allows you to quickly and accurately track which assets your users log on to most frequently and expedite the process of granting remote access to those devices.
Remote network access
With the Insight Network Sensor, you’ll monitor, capture, and assess the end-to-end network traffic moving throughout your physical and virtual environment, including remote workers when deployed alongside your VPN solution.
Our approach to Network Traffic Analysis (NTA) is unique in that our Managed Detection and Response (MDR) team has curated a library of the most critical Intrusion Detection System (IDS) alerts for teams to focus on, helping cut down on noise and increase analysts’ confidence in taking action. We also leverage a proprietary Deep Packet Inspection (DPI) engine to capture all raw network traffic flows, extracting rich metadata. This information is enriched with our User Behavior Analytics attribution engine, so you can quickly identify which user and what asset is associated with a network flow.