Today’s SIEM tools aren’t just for compliance and post-breach investigations. Advanced analytics, such as user behavior analytics, are now core to SIEM to help teams find the needles in their ever-growing data stacks. That means in order for project success, the right data sources need to be connected: “If a log falls in a forest and no parser hears it, the SIEM hath no sound.”
We’ve included endpoint visibility in InsightIDR since the beginning—it’s the key to detecting attacks involving remote workers or lateral movement early in the attack chain. InsightIDR now supports the Insight Agent for Mac, meaning you can deploy a single agent on any Windows, Mac, or Linux system for it to feed real-time data across our product portfolio.
What’s the Benefit of the Insight Agent?
Installing and maintaining too many agents adds to your existing workload. The Insight Agent is therefore designed to universally collect data for all Insight solutions and automatically update—although if needed, it can adapt to your patching cycles. Most importantly, we constantly ensure that the Insight Agent is not disruptive to the end user. It has a tiny (50 MB) disk footprint and transmits a daily average of 1-2 MB. The computational analytics take place in InsightIDR, and not the endpoint itself.
Deploying the Insight Agent gives you three benefits in InsightIDR:
- System-level visibility
- Real-time, deceptive detections
- Endpoint investigation and hunting
Visibility
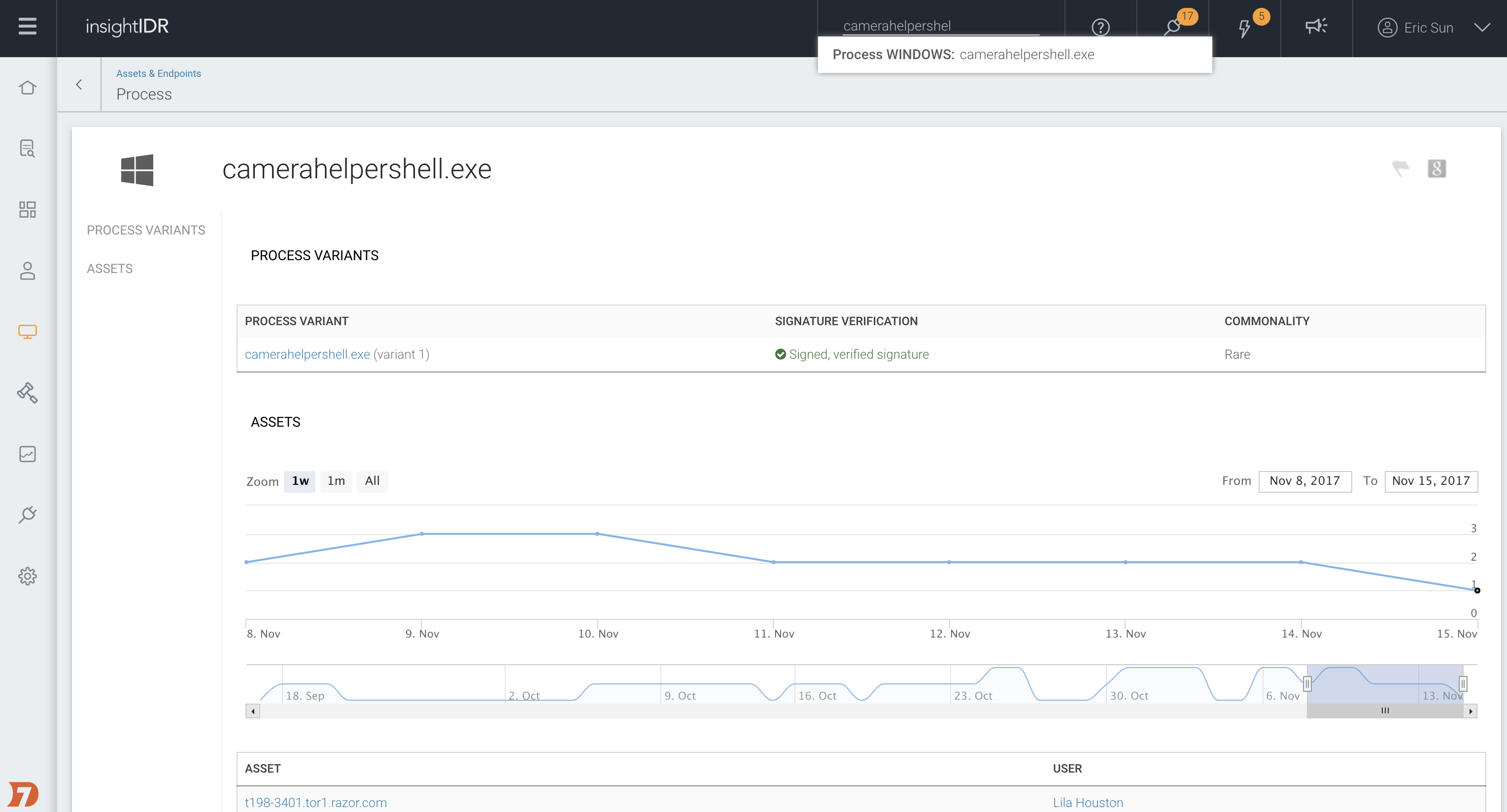
- Running processes. Every process on your endpoints is matched against multiple threat intelligence sources, ranging from intel from our Managed Detection and Response (MDR) Services team to a composite of anti-virus signatures. Across all your assets, unique and rare processes are surfaced to reveal Shadow IT (programs installed without IT oversight) and “unknown-unknowns.”
- Anomalous admin action. Across InsightIDR, administrative activity is correlated to identify attacks on privileged accounts. Suspicious local-level activity, such as privilege escalation or log deletion, results in alerts to help you react earlier in the attack chain.
Intelligent Detection with a Dash of Deception
- Lateral movement: Active Directory (AD) is a foundational data source for InsightIDR, but the authentication logs aren’t comprehensive. Our user behavior analytics combine endpoint with AD, LDAP, DHCP, VPN, and cloud APIs to detect lateral movement across assets and services.
- Password and protocol attacks (e.g. MimiKatz, Responder): Once the Insight Agent is deployed, honey credentials are injected onto the endpoint—fake password hashes that don’t grant access to any system. If an attacker tries these hashes elsewhere, you’ll receive an alert. An endpoint presence also allows us to creatively detect Responder, a very popular tool that steals user credentials by spoofing as a trusted network service.
Endpoint Hunting
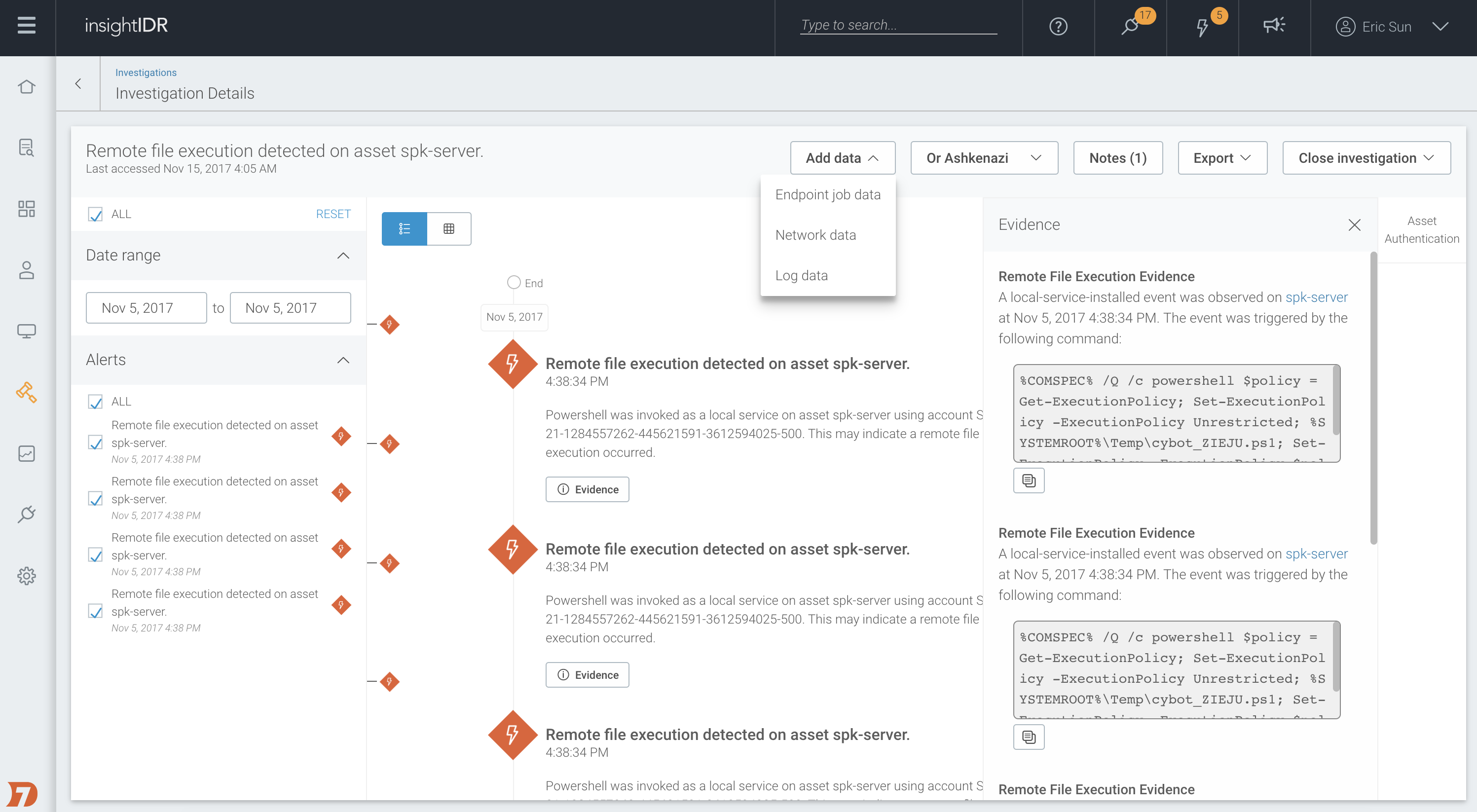
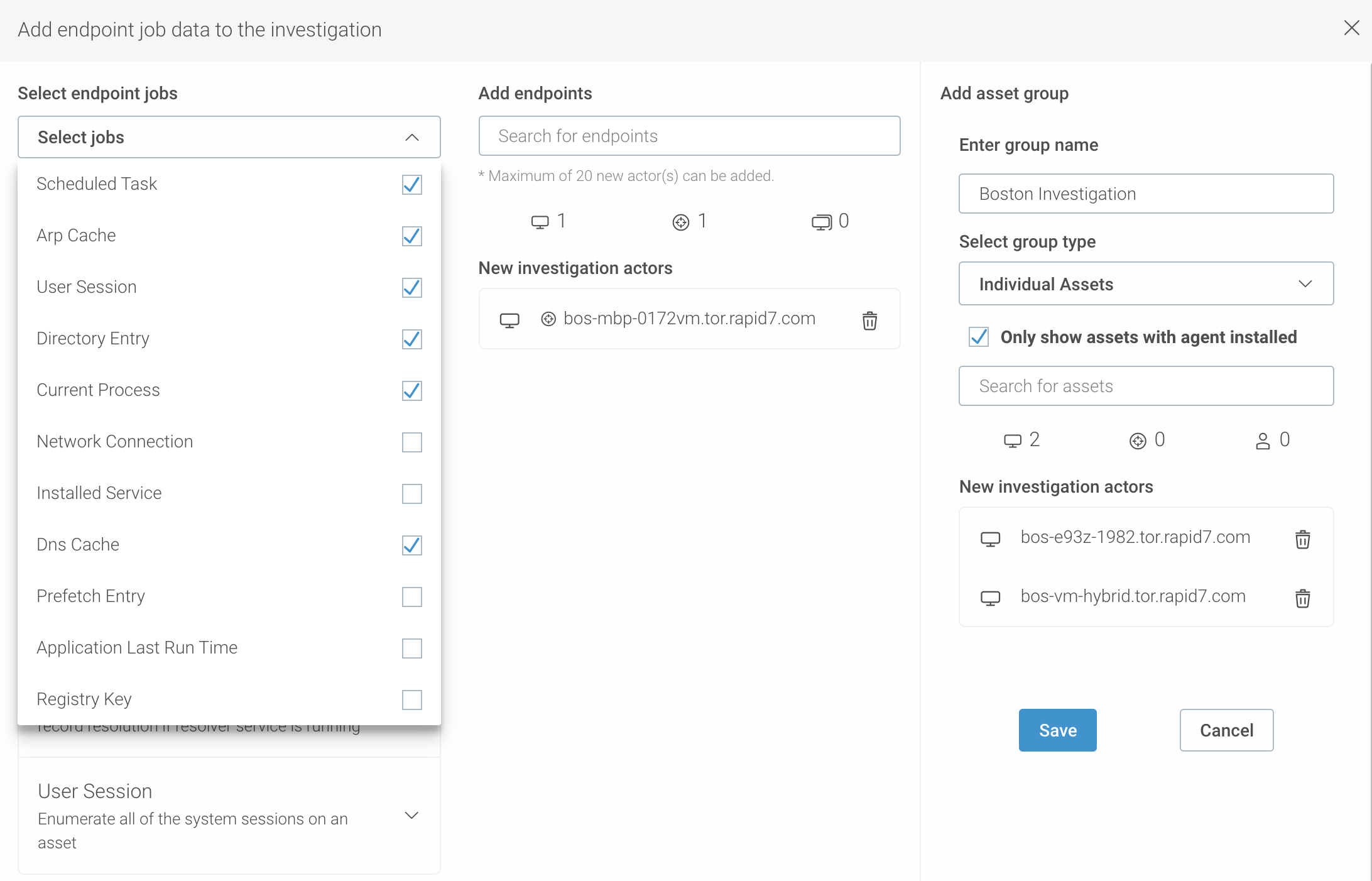
- On-Demand Investigation. Every alert generated by InsightIDR comes with a visual timeline that highlights the involved users, assets, and their behaviors. The Insight Agent allows you to go a layer deeper by running on-demand jobs that can pull additional context such as registry keys, scheduled tasks, prefetch data, and more.
- Managed Detection and Response hunts. Insight Agent data is a key component of the User-Host-Process (UHP) analysis model used by our MDR team. Hunting includes running frequency analysis on process data, applying vertical-specific threat intelligence, and simply “digging for evil”, such as identifying behaviors regular users simply don’t make.
Mac Agent Installation
We strongly recommend you deploy the Insight Agent across your environment. Deploying the Mac agent only takes a few steps:
- Head to the Data Collection page in InsightIDR.
- Download the zipped Insight Agent installation file and run it. You can also use a command line installation (tools included) for a silent, scalable roll-out.
Article Tags
Related blog posts

Products and Tools
InsightIDR AI Alert Triage Automatically Classifies Alerts with 99.93% Benign Alert Accuracy
Chris Wraight

Detection and Response
New IDR Log Search Enhancements: Accelerate, Streamline, and Simplify Investigations
Rapid7

Products and Tools
What’s New in Rapid7 Products & Services: Q3 2024 in Review
Margaret Wei

Detection and Response
Rapid7 Named a Leader in IDC MarketScape: Worldwide SIEM for SMB and Enterprise
Meaghan Buchanan