After a couple of relatively light weeks (blame SXSW, I guess), this week's update has quite a few neat new additions. As always, if you don't already have Metasploit, what are you waiting for? For the rest of us, here's what's new.
Importapalooza
This week's update has support for importing asset lists exported from Spiceworks, courtesy of Rapid7's Brandon Perry. Spiceworks is a free asset management application used by tons of IT pros and IT amateurs alike, and Metasploit can now take the Spiceworks small and medium business folks -- specifically, the results of the "Spiceworks Inventory Summary CSV export" and turn that into a target list of IP addresses. This brings the total number of supported import formats Metasploit can handle to 23 (including libpcap, nmap XML, Nessus, Qualys, Nexpose of course, and a pile of others).
More interestingly, I believe it's the first non-security-centric asset management format we cover. If you have a favorite asset management tool that produces some kind of parsable report (XML, CSV, or whatever), we'd love to see a sample of the output, or even better, a pull request to handle the format along with your sample.
Apple Filing Protocol
Community contributor Gregory Man added support for the Apple Filing Protocol (AFP) this week, in support of his afp_login module, adding to the parade of authentication protocols that Metasploit supports. While AFP is a relatively simple protocol in the scheme of things (it's small, nicely documented, and common), actually implementing any new wire protocol in pure Ruby is no small task. Thanks a ton for that, Gregory!
The MS12-020 RDP "Exploit"
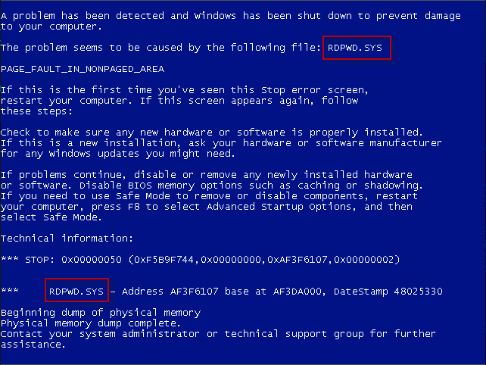
This week, there was some small amount of buzz over at over at ThreatPost around Wei "sinn3r" Chen's addition of the denial-of-service module ms12_020_maxchannelids. Various Metasploit contributors and other security researchers got together over the weekend on Freenode IRC to see if they couldn't put together a proper exploit for the vulnerability patched by MS12-020 based on publicly-available information. This module is certainly not the end of that story -- it's somewhere in the middle, really. It does exercise the vulnerability, though, and crashes the target with a bluescreen, so defenders can use this module to get an idea of what to look for when either detecting a "real" exploit, and exploit writers can refer to it for guidance in case they missed the IRC pow-wow.
On the right, you see a screenshot of a BSOD when this vulnerability is exploited. If one of your server bluescreens detailing RDPWD.SYS, you may be under attack by a Terminal Services mischief maker.
New HTTP Downloader Payload
Finally, this week we've committed Peter "corelanc0d3r" Van Eeckhoutte's new HTTP downloader payload, windows/download_exec_https. The name is a little misleading, though, because it supports HTTP, HTTPS, and FTP protocols, as it uses the native InternetConnectA functionality in Microsoft's standard wininit.dll, and that guy handles all three.
It seems to work pretty well on all the platforms we tested, so if you're already using windows/download_exec to deliver executables to exploited targets, you might want to give this one a shot. The option syntax is identical, so it should just be a matter of swapping out one for the other. The module itself is at much better documented internally than the old download_exec standby, so it's a little less mysterious as to what's going on. Thanks for all the work on this, corelandc0d3r!
Additional New Modules
- netdecision_traversal, by sinn3r, exploits _blank">OSVDB-7986 found in NetDecision's NOCVision Server.
- netdecision_http_bof, by sinn3r, exploits OSVDB-79651 found in NetDecision's HTTP service.
- sockso_traversal, by sinn3r, exploits BID-52509 in Sockso's Music Host Server.
- dell_webcam_crazytalk, by sinn3r, exploits OSVDB-80205 in Dell's WebCam CrazyTalk ActiveX control.
- rails_mass_assignment, by Gregory Mann, exploits a the mass-assignment Rails configuration error recently discussed on GitHub.
- enum_protections, by ohdae, details the security software installed an a target Linux machine.
- enum_adium, by sinn3r, interrogates the Mac OSX's built-in chat client Adium for account info and chat logs.
In addition, some post modules were shuffled and recombined to more immediately useful for end users -- most of this work was by ohdae and sinn3r:
- enum_system combines the functionality previously a part of enum_cron, enum_services, enum_packages, as well as some of the functions in enum_linux
- The rest of enum_linux was broken out into the post modules enum_configs, enum_network, enum_users_history
Availability
If you're new to Metasploit, you can get started by downloading Metasploit for Linux or Windows. If you're already tracking the bleeding-edge of Metasploit development, then these modules are but an msfupdate command away. For readers who prefer the packaged updates for Metasploit Community and Metasploit Pro, you'll be able to install the new hotness today when you check for updates through the Software Updates menu under Administration.
For additional details on what's changed and what's current, please see Jonathan Cran's most excellent release notes.
Related blog posts

Products and Tools
Weekly Metasploit Update: Apache ActiveMQ RCE, Gogs Rebase RCE, and Windows Kernel Pointer Enum
Brendan Watters

Products and Tools
Metasploit Wrap Up 05/29/2026
Spencer McIntyre

Products and Tools
Metasploit Wrap Up 05/22/2026
Martin Sutovsky

Products and Tools
Metasploit Wrap-Up 05/15/2026
Martin Sutovsky
