Back in July we announced a substantial improvement to our search functionality, searching your log data with logical operators. Today we are happy to announce another big step in improving our search facility. You can now perform **field-level searches**in Logentries. Field-level searches allow you to search for events where a particular field is equal to, less than or greater than a particular value and thus allow you to perform much more powerful searches very easily. You can also combine field level searching with regular expressions to identify fields values that match a particular pattern. To take advantage of our field-level search capabilities, your log events must conform to a particular structure (i.e. JSON structured fields, or the classical form of ‘field=value’). Note, a typical log entry contains a timestamp, event type, and parameters. For example, a typical log entry may look like this:
2013-06-28T10:29:28+00:00 source=web operation=POST status=200 url='/login/' size=19341bytes response=6.25e-3
This log entry tells us about one POST login request on the web server. The response returned was 19341 bytes in size and it took 6.25ms to return the request. If you assign names to parameters as in the above log event, you have a key-value relation (key=value). This is called a field. A Field’s value can be any textual data, including integers, and floats. For Logentries to be able to work with numerical values, they must be formatted as an integer, floating-point value, or in the scientific notation. Note, Logentries will also understand JSON-like and, Ruby or Perl-like dictionaries so if you prefer your favorite serialization language, you can use these too! So for example, Logentries will automatically detect fields and values formatted the following ways:
{"version":"1.23"}, "response_time"=>1.23
Searching
Logentries provides an intuitive way to query for particular fields and then test their value. Just type in a field’s name, a comparator, and a value. You can test whether a field equals or does not equal a certain value (equality =, inequality !=), or test whether a field is less <, less or equal <=, greather >, or greather or equal >= a numerical value. For example, with a log entry structured similar to the example above, we can search for all web requests (i.e. source=web) which took longer than 2 seconds:
source=web response>=2
We can search for web requests whose status code is not 200 and 204:
source=web (status!=200 AND status!=204)
We can also combine field level search with regular expressions to match fields with values that contain a particular pattern. For example, we can search for all web requests, with urls that contain a user_id:
source=web url=/\/user\/\d+\//
That’s it for today folks! You can learn more about how to use field level search to get the most from your log data in our more detailed documentation. Search away and do let us know if you have any feedback!
Article Tags
Related blog posts
Products and Tools
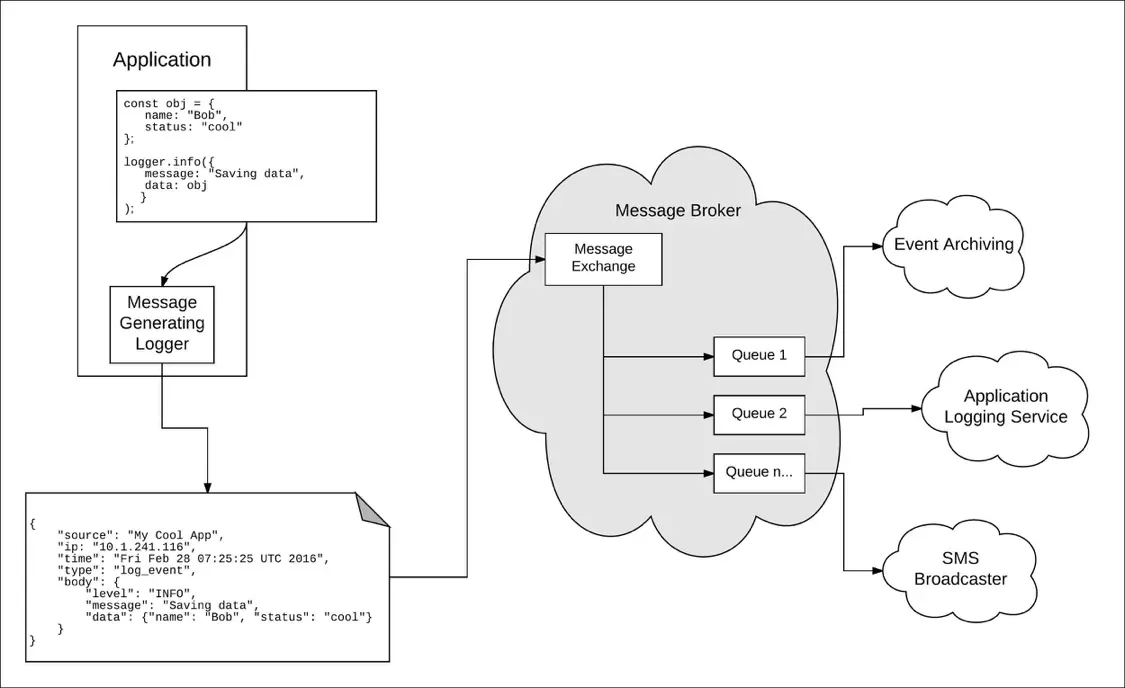
Taking a Message-Based Approach to Logging
Robert Reselman
Detection and Response
6 Best Practices for Effective IT Troubleshooting
Robert Reselman

Security Operations
3 Steps to Building an Effective Log Management Policy
Robert Reselman

Security Operations
3 Core Responsibilities for the Modern IT Operations Manager
Robert Reselman
